ARPSyndicate - Cyber & Open Source Intelligence
1.5K posts


ARPSyndicate - Cyber & Open Source Intelligence
@arpsyndicate
An Information Discovery Company with hyperspecialization in Subdomain and Exploit Intelligence.




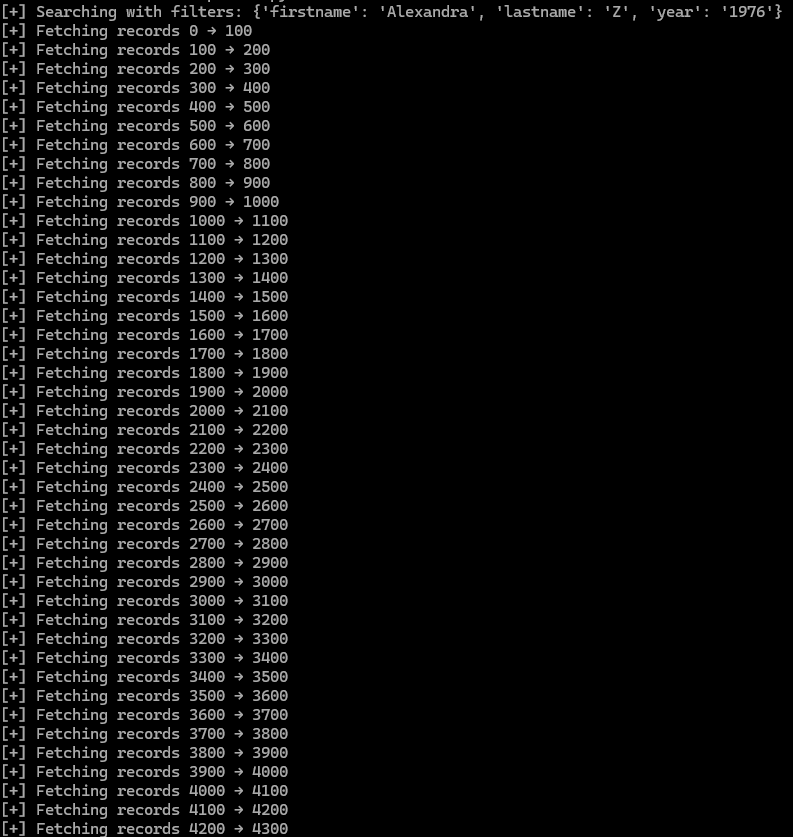
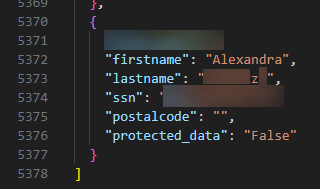
Sitting here staring at an open API that allows you to search for Swedish citizen data.. full names, ssns, postal codes, etc. If a TA knows about this, holy. I have no idea what company this belongs to nor can I share the url.






‼️🇺🇸 Nike has been named a victim to World Leaks Ransomware





There’s some exploit or mass-scale abuse with @Zendesk right now… I just got EIGHT HUNDRED emails from them over the course of about an hour. They’re all scams sent from different Zendesk instances. Many bypassed iCloud’s Junk filters.

Microsoft Threat Intelligence observed the rapid proliferation of RedVDS, a virtual dedicated server (VDS) provider used by financially motivated threat actors for BEC, phishing, account takeover, and financial fraud campaigns spanning multiple sectors. msft.it/6016t7J5m


🇨🇳 THE KNOWNSEC LEAK: Yet Another Leak of China’s Contractor-Driven Cyber-Espionage Ecosystem 01/09/2026 dti.domaintools.com/the-knownsec-l…