Alex Teixeira
12.8K posts


Alex Teixeira
@ateixei
I design and build #SIEM content for a living. Editor at https://t.co/WIrKw7X1p5 #DetectionEngineering & Research, #ML #Stats x-Splunk


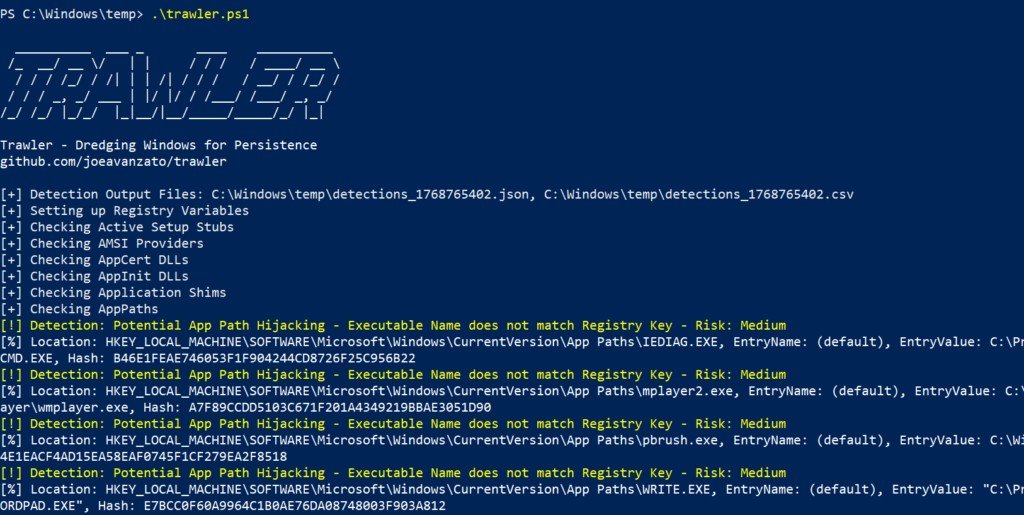




@cyb3rops Did some similar work with reverse engineering binaries with LLMs and realized the same thing — bad things embedded in nice names just cause it to ignore the finding. So wrap your ransomware code in “Ransomware Simulation” strings and you’re off to the races.




POV: You are using an iPhone Green / Yellow dot appears over your screen HELLO HELLO PRIVACY 💀


Pessoas que moravam fora e voltaram para o Brasil. Conheço pessoas que moraram em Londres durante 20 anos e voltaram pra cá e não se arrependeram… Por que voltar?

roses are red violets are blue get your mom kfc she's tired of cooking for you