Azuremis
1.6K posts


Azuremis
@azuremis
ᴏᴍɴɪɢɪɴᴇᴇʀ • 🌍/ᴀᴄᴄ • 🕉️/ᴀᴄᴄ ᴄʀᴀғᴛɪɴɢ ᴛʜᴇ ɢᴇᴏᴍᴇᴛʀʏ ᴏғ ɪɴᴛᴇʟʟɪɢᴇɴᴛ ᴍᴀᴄʜɪɴᴇ𝕤 | ᴀʟɪɢɴᴍᴇɴᴛ ɪs ᴇᴅᴇɴ








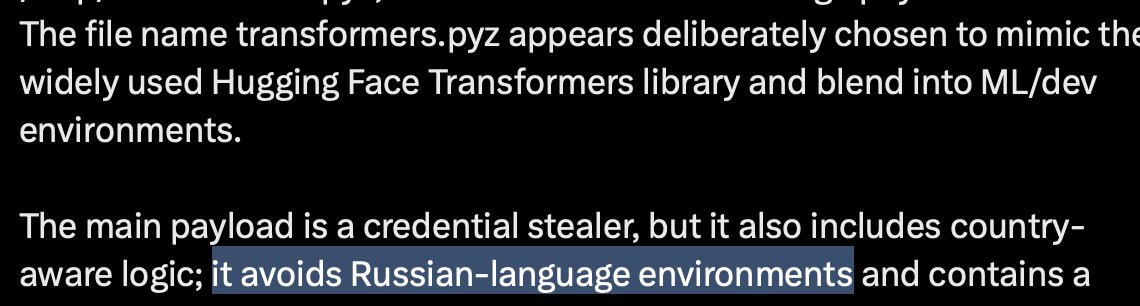
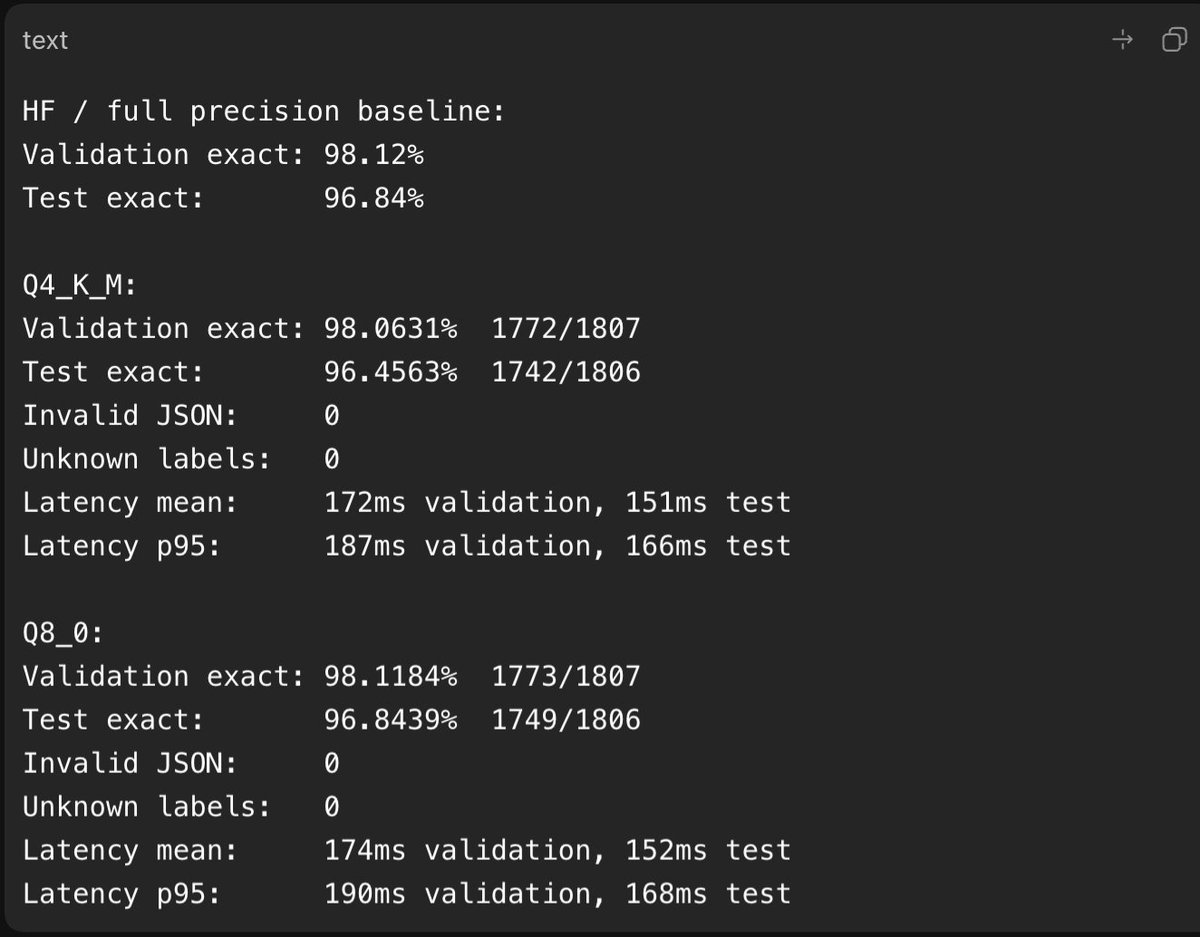
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux. The file name transformers.pyz appears deliberately chosen to mimic the widely used Hugging Face Transformers library and blend into ML/dev environments. The main payload is a credential stealer, but it also includes country-aware logic; it avoids Russian-language environments and contains a geo fenced destructive branch that has 1-in-6 chance of executing rm -rf / when the system appears to be in Israel or Iran. To mitigate this threat: isolate affected Linux hosts, block 83[.]142[.]209[.]194, hunt for /tmp/transformers.pyz, pgmonitor[.]py, and pgsql-monitor.service, and rotate exposed credentials.


What they don't tell you in calculus