Alex Beszedin 🧬
9.9K posts


Alex Beszedin 🧬
@beszedin
developer https://t.co/KYwmaWdBmf | Cryptocurrency is good.

Not sure who needs to hear this, but acquiring old NFT projects is usually neither a good idea for the buyer nor bullish for holders. Cases where abandoned NFT projects are successfully "revived" are extremely rare. It also requires immense effort (financially, creatively and socially). Buying an NFT because of a random acquisition (or worse, acquisition rumors) won't age well


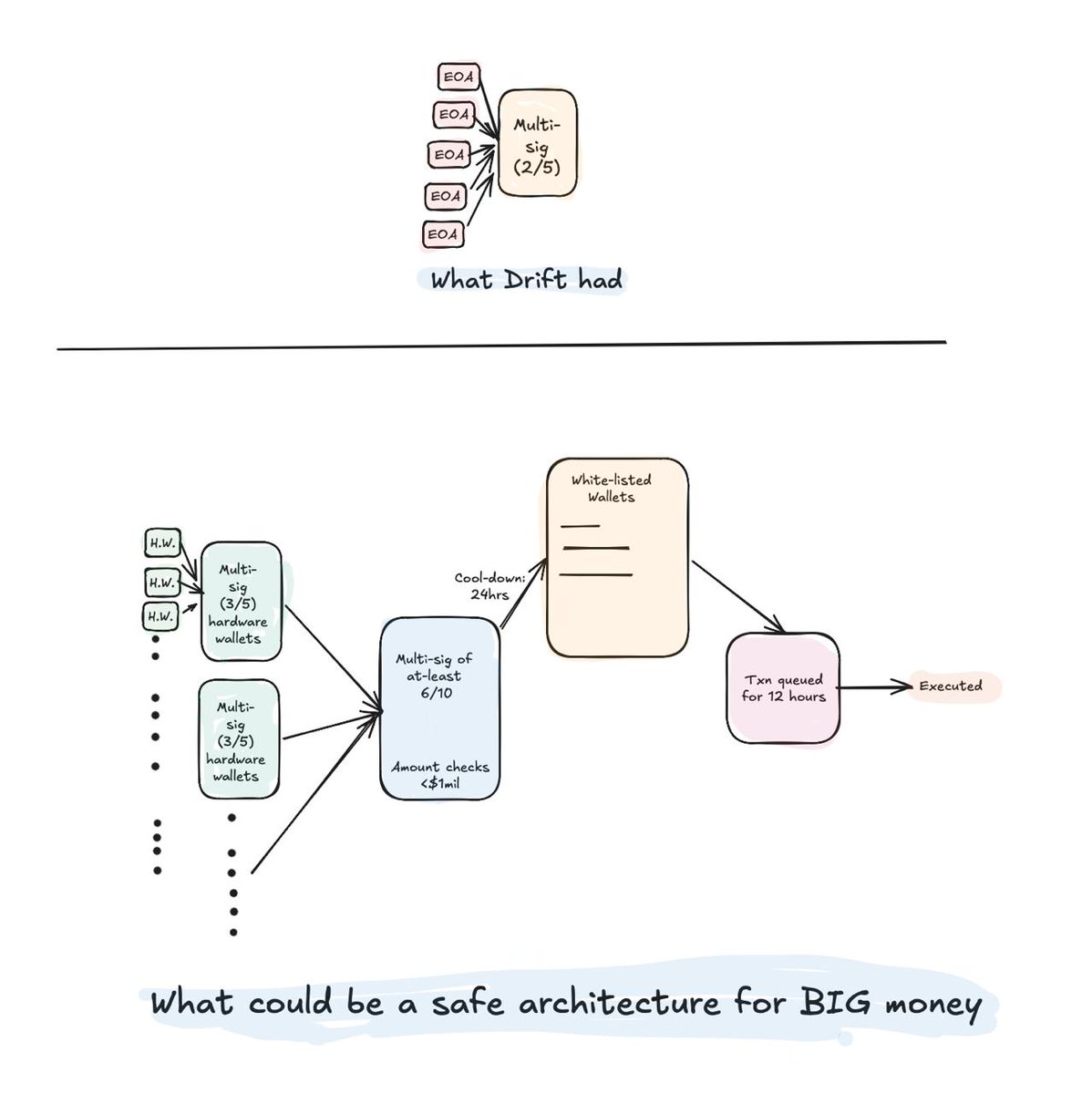
Following the KelpDAO hack, we built an open analysis of DVN security configurations across every active OApp on LayerZero over the last 90 days. Of ~2,665 unique OApp contracts: 47% run a 1-of-1 DVN security floor, 45% run 2-of-2, and ~5% run 3-of-3 or higher. As we know, KelpDAO's rsETH sat in the first bucket. Open query, public methodology, feedback welcome: dune.com/dune/layerzero…








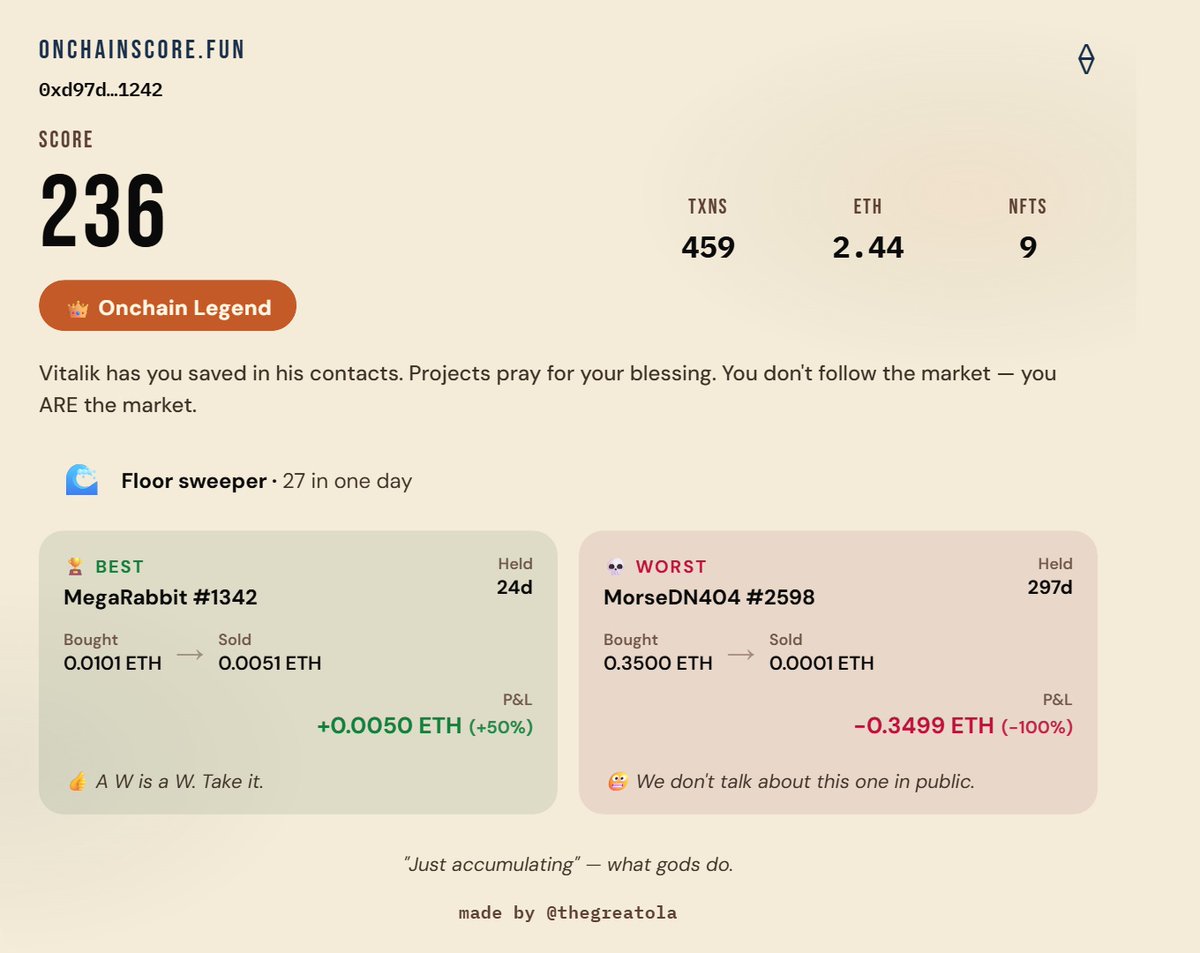
I built a fun on-chain wallet checker that scores you based on your wallet history and performance. Check your score here: onchainscore.fun