David
93.4K posts


David
@blueblooded_AP
Saved By Jesus Christ, receiver of the Holy Spirit, Husband, Father, Gators For Life, Proud American, PureBlood




Under the SAVE Act, you cannot use your driver's license to register to vote. Republicans want you to buy a passport instead. If you can afford one. This is a modern-day poll tax.

As war with Iran threatens to disrupt economy, CalPERS considers risks to fund sacbee.com/news/politics-…



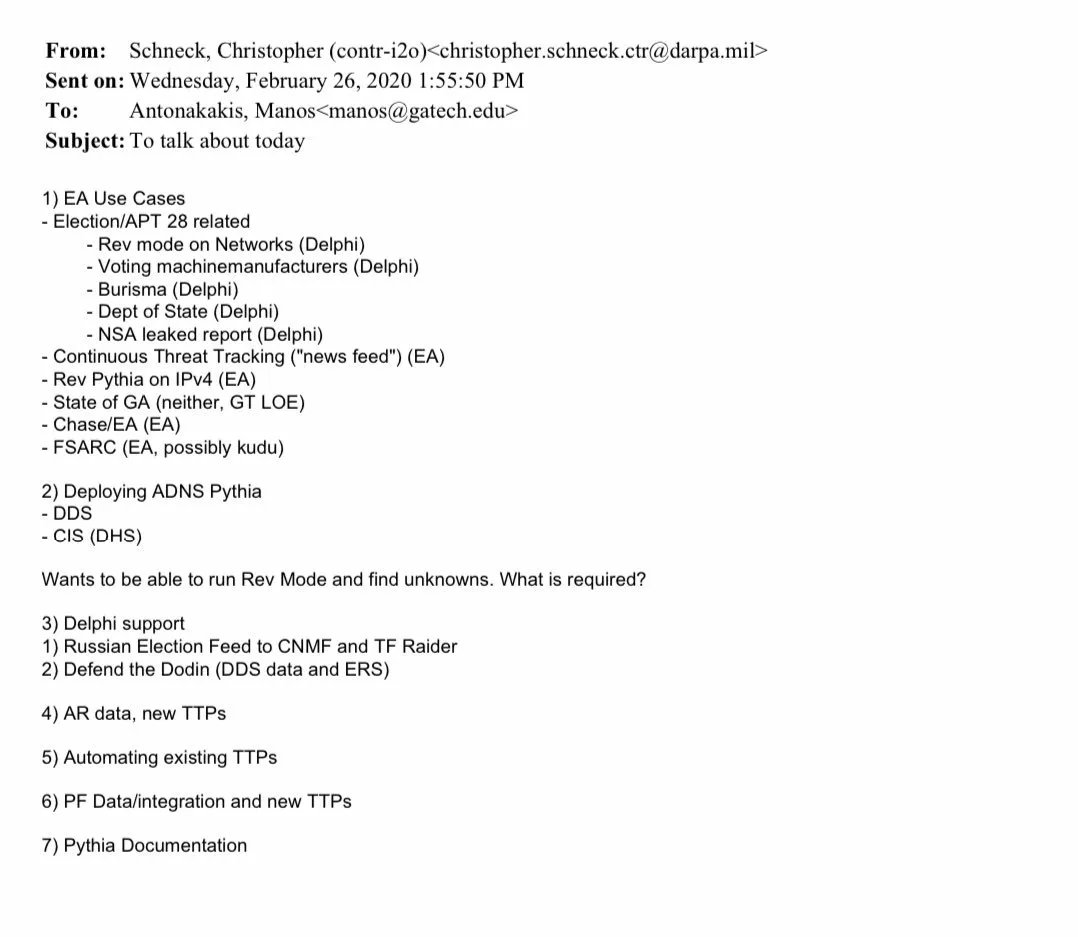
Three Charged with Conspiring to Unlawfully Divert Cutting Edge U.S. Artificial Intelligence Technology to China “The indictment unsealed today details alleged efforts to evade U.S. export laws through false documents, staged dummy servers to mislead inspectors, and convoluted transshipment schemes, in order to obfuscate the true destination of restricted AI technology—China,” said John A. Eisenberg, Assistant Attorney General for National Security. “These chips are the product of American ingenuity, and NSD will continue to enforce our export-control laws to protect that advantage.” 🔗: justice.gov/opa/pr/three-c…










Senator John Hickenlooper LIES that the Save America Act will force all Americans to re-register to vote: HICKENLOOPER: “It requires every voter...to find their birth certificate, find their passport, just so they can register to vote."



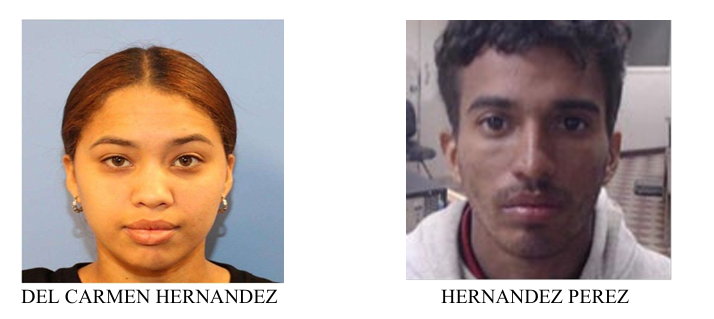


I just got off the phone with a whistle blower in the Skid Row election fraud ring. Two courageous individuals are willing to step forward. Their terms are that a food drive is conducted on the Row. Help us raise money for the drive! 👇🏻 givesendgo.com/feednotscam?ut…