Brandon()
602 posts


Microsoft Warns of Exchange Server Zero-Day Exploited in the Wild securityweek.com/microsoft-warn…

🚨 OpenClaw Chain Vulnerabilities Expose 245,000 Public AI Agent Servers to Attack Source: cybersecuritynews.com/openclaw-chain… A chain of four critical vulnerabilities discovered in OpenClaw, one of the fastest-growing open-source platforms for autonomous AI agents, has left an estimated 245,000 publicly accessible server instances exposed to remote exploitation, credential theft, and persistent backdoor installation. Shodan and ZoomEye scans as of May 2026 reveal approximately 65,000 and 180,000 publicly accessible OpenClaw instances, respectively, totaling roughly 245,000 exposed servers. What makes this chain especially dangerous is that the attacker weaponizes the AI agent’s own privileges. #cybersecuritynews


Effective today, we are: 1) Doubling Claude Code’s 5-hour rate limits for Pro, Max, and Team plans; 2) Removing the peak hours limit reduction on Claude Code for Pro and Max plans; and 3) Substantially raising our API rate limits for Opus models.

How do people seek guidance from Claude? We looked at 1M conversations to understand what questions people ask, how Claude responds, and where it slips into sycophancy. We used what we found to improve how we trained Opus 4.7 and Mythos Preview. anthropic.com/research/claud…



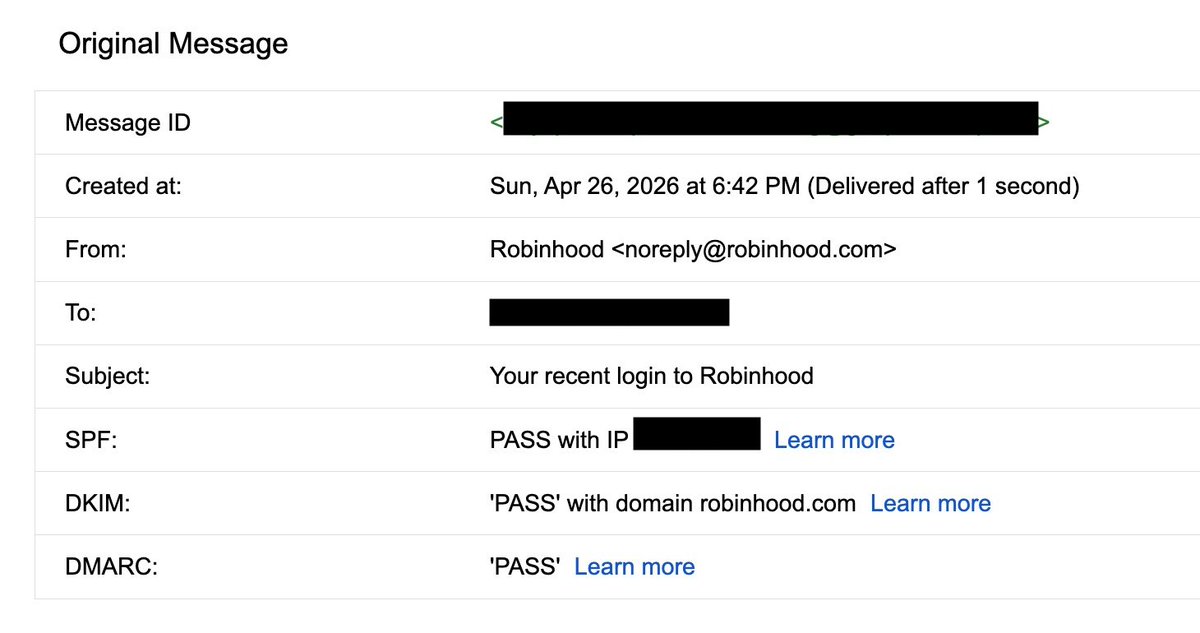



New Robinhood phishing chain that's kinda beautiful: 1. Attacker creates an RH account using the Gmail dot trick of your email (same inbox, different address) 2. Sets device name to HTML 3. RH's "unrecognized activity" email renders the device name unsanitized (html injection) The result is a real email from noreply@robinhood.com, DKIM pass, SPF pass, DMARC pass, with a phishing CTA Just because it's real, doesn't mean it's safe... $HOOD



🚨 Bitwarden CLI 2026.4.0 was compromised as part of the ongoing Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline. We’ll continue updating our coverage as more details are confirmed. socket.dev/blog/bitwarden…

Ever since upgrading to OpenClaw 2026.4.12 (I think) with openai-codex, I've been getting max retry and invalid API response messages in Discord even though my agent replies. Anyone else seeing this too? I upgraded to the newest 2026.4.15 earlier, this doesn't happen with Telegram and I don't see anything in the logs. I have plenty of usage remaining on my plan. ----- Max retries (3) for invalid responses — trying fallback... Invalid API response shape. Likely rate limited or malformed provider response. Max retries (3) exceeded for invalid responses. Giving up.

Did Anthropic unblock first party harness?! Yesterday, this was failing and it appears the OpenClaw docs have been updated. claude -p --append-system-prompt 'A personal assistant running inside OpenClaw.' 'is clawd here?' Yes, Claude is here. What can I help you with?

Anthropic allows OpenClaw usage again. From @openclaw docs.

@daniel_mac8 @openclaw Unfortunately I still couldn't get it to work properly with OpenClaw v2026.4.2 because it wasn't generating the auth-profiles.json file for it. I think it was a bug but not sure - I ended up upgrading to the newest version and switching to GPT-5.4.