
c3y-v2
1.2K posts


c3y-v2
@c3y_v2
.- -. - .. -. .- - .- .-.. .. ... - Li4uLSAuIC0tLiAuLSAtLg== -.-. ...
/dev/null Katılım Nisan 2019
742 Takip Edilen76 Takipçiler
Sabitlenmiş Tweet

“We must accept the fact that no barrier is impenetrable, and detection/response represents an extremely critical line of defense. Let’s stop treating it like a backup plan if things go wrong.”
“Prevention is ideal, but detection is a must.” #soc #CDC #cyberdefence
English
c3y-v2 retweetledi
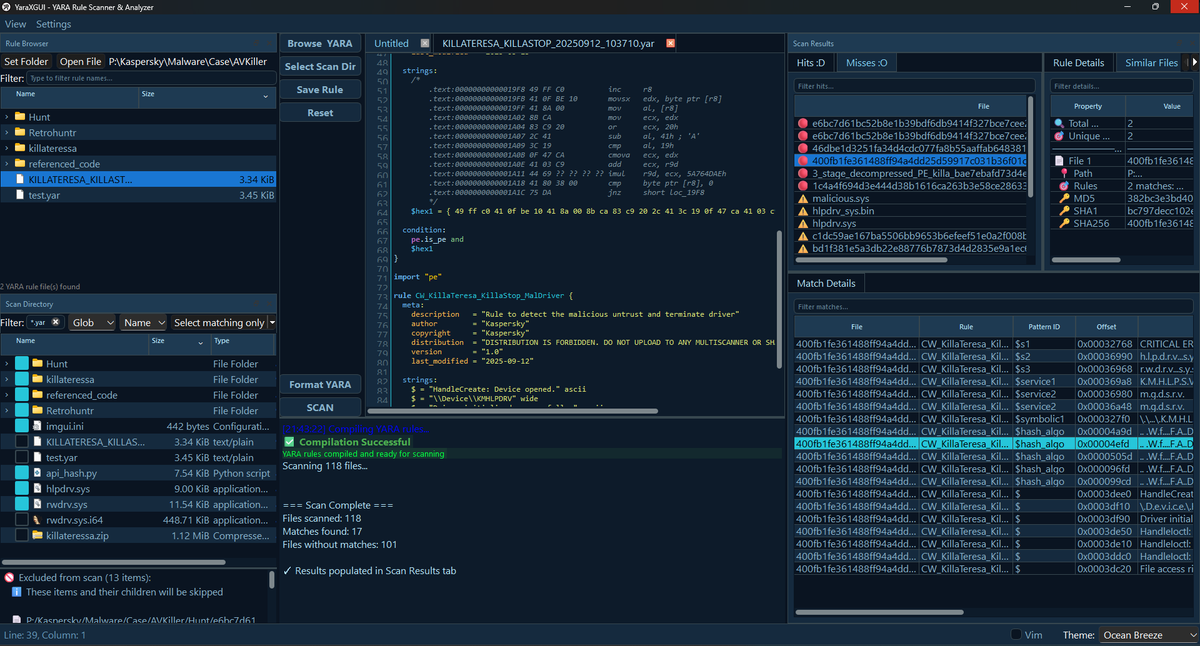
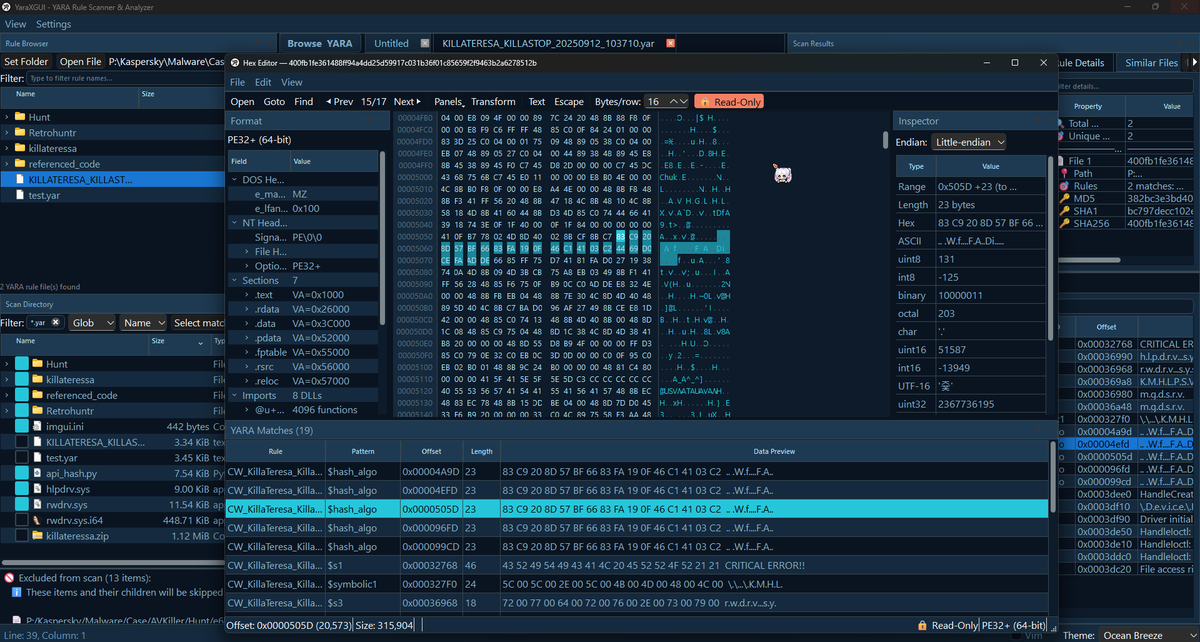
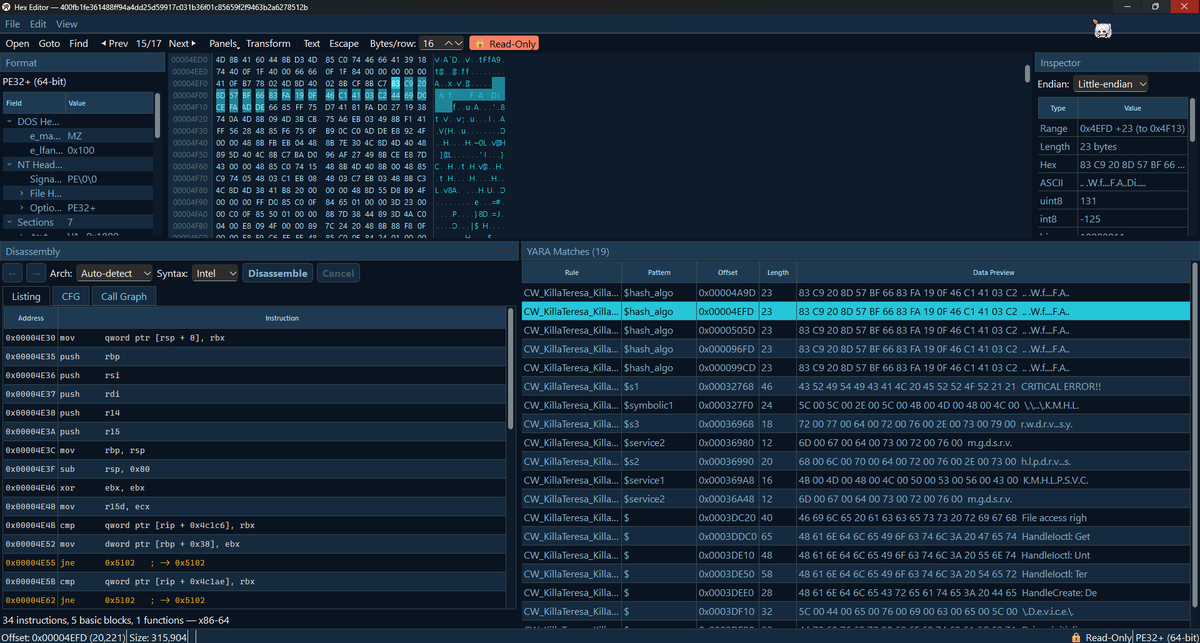
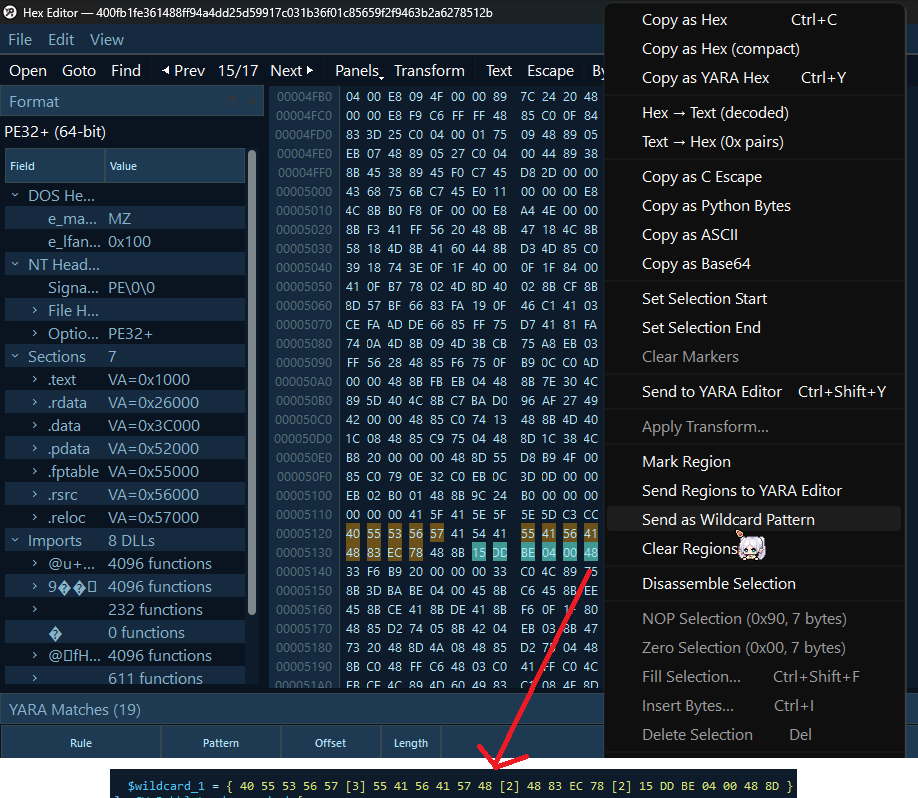
YaraXGUI Improvements
HexEditor, Yara Match Table to show all matches found. It supports more tab, yara formatting fixed as well. We can browse for rules and filter files that we want to scan this time. Hex editor is added with the goal to make it more hassle free.
Within the hexeditor, we can also apply changes, do basic diffing, mark multiple regions and send to YARA editor. Also included a way to select multiple regions and gaps within each regions can be set a wildcard so we do not need to calculate each size.
Can now do disassembly of selected region (capstone), draw basic CFG to do quick checks (maybe for certain obfuscation technique or unique code blocks). Simple parsing for PE and ELF file.
Added a wonky and (not-so-reliable) autocomplete (NOT based off parser) but good enough I guess for my workflow).
To try the new version: github.com/Owl4444/YaraXG…
English
c3y-v2 retweetledi

Eu sei que geral se preocupa com vazamento de .env, mas vocês deram uma olhada nos arquivos dentro do .claude? Mais especificamente o settings.local.json. Armazena senhas, tokens em texto claro, fiquem sempre alertas,verifiquem o arquivo dentro dos seus projetos #bolhasec
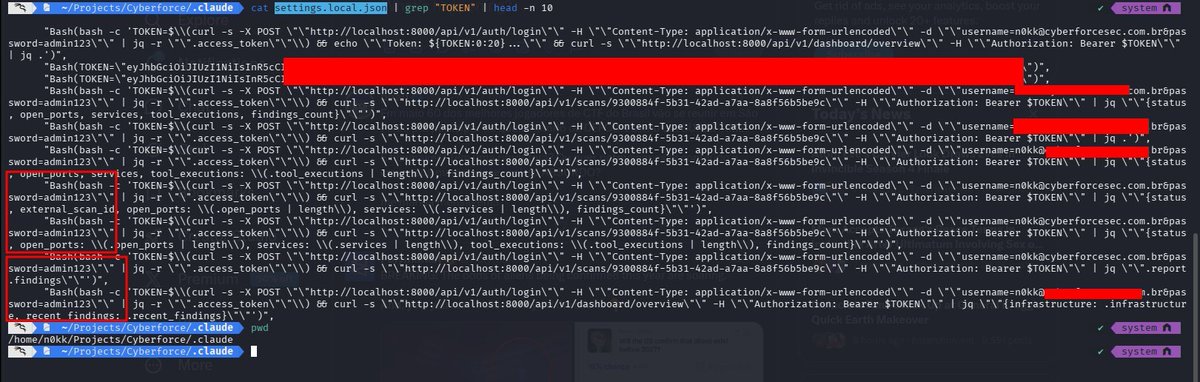
Português
c3y-v2 retweetledi

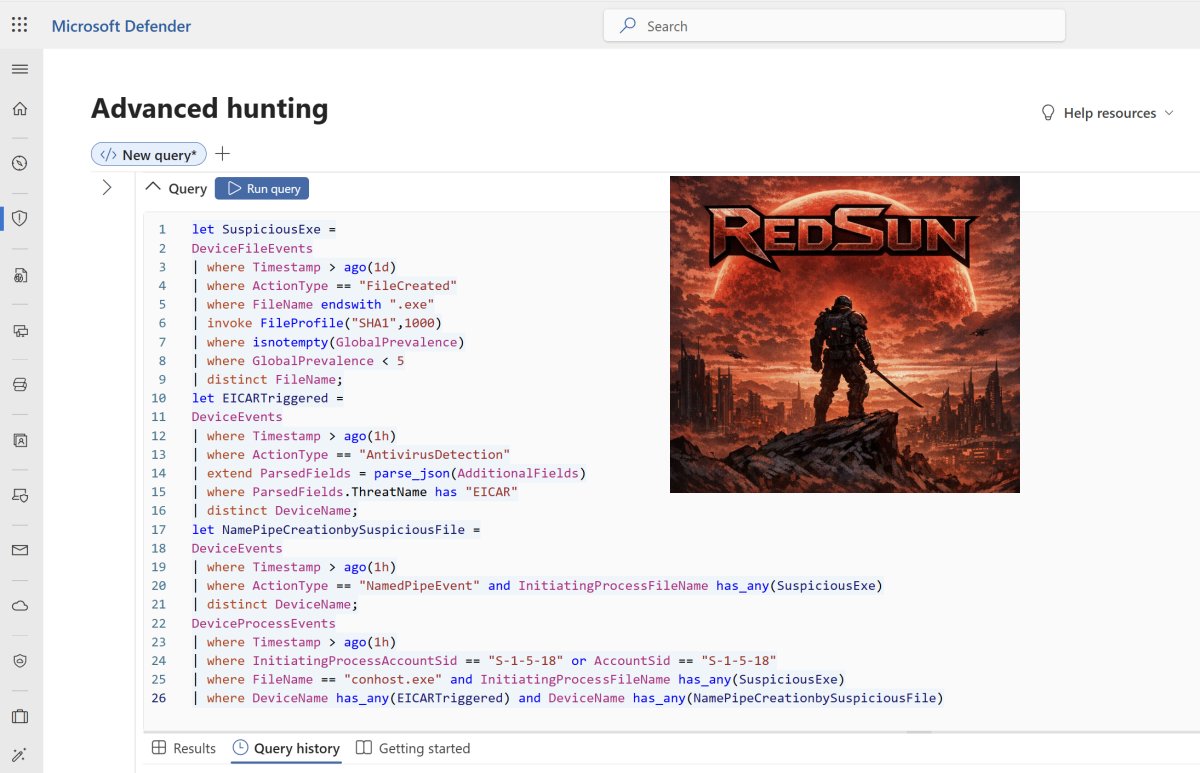
Hunting RedSun 🌞
Inspired by the Nightmare‑Eclipse RedSun PoC, I’ve expanded my BlueHammer KQL detection to uncover Defender’s behavioral blind spots.
Sharing my DefenderXDR hunting logic with the community — evolving the path from BlueHammer to RedSun.🎯
KQL Code: github.com/SlimKQL/Detect…
#CyberSecurity #RedSun #DetectionEngineering #DefenderXDR
English
c3y-v2 retweetledi
c3y-v2 retweetledi

This whole Mythos thing continues to surprise me. Not the model, but the reaction to it.
Guys, it's not even a fucking cyber model. It's just the next thing. It's just a model designed to solve problems well.
This isn't some OMG moment, and if it is for you then you need to massively re-think things.
This is just what you should expect to happen constantly, every few months or a couple times a year. At least.
Every model jump gets better, and some will get WAY better. This is one of those jumps. But it's not the first and won't be the last.
We're barely even good at doing ML research. Our research pipelines are janky as hell. We haven't even automated research with things like autoresearch yet.
It's like we've built vacuum tubes and not even discovered transistors yet, and we're like, "Welp, this is the best vacuum tube so I guess that's the end of the story."
The AI we have today will be studied in museums like Comodore 64's and punch cards.
Mythos is just a tiny glimpse of the new normal.
Plan accordingly.
English
c3y-v2 retweetledi

5 yıldır çalıştığım kurumsal firma, performans düşüklüğü bahanesiyle beni tazminatsız işten çıkardı. Üstelik tüm fazla mesailerimin üstüne yattılar. Bugün tesadüf eseri öğrendim ki, yerime aldıkları kişi genel müdürün yeğeniymiş ve benim 3 katım maaşla başlamış. Avukatımla görüştüm; geriye dönük tüm haklarımı ve manevi tazminatımı alabiliyormuşum. Eğer davayı açarsam şirketin bu usulsüzlüğünü herkes duyacak. Sizce 'hakkımdır' deyip dava mı açmalıyım, yoksa 'dünya hali' deyip hiçbir şey yapmadan başka iş mi bakmalıyım?"
Türkçe

Telemetry source mapping (Event IDs, Sysmon, CloudTrail, auditd, EDR)
Interactive D3FEND defensive technique diagrams per ATT&CK technique
No server, no dependencies, no internet required. Open index.html in any modern browser.
#lolbin #lateralmovement #mitre #d3fend #blueteam
English

lollateral.github.io
LOLLATERAL is a single-file, offline-capable interactive reference for MITRE ATT&CK TA0008 Lateral Movement. It is inspired by LOLEXFIL, LOLBAS,and LOLC2, extending the "Living Off the Land" reference format to cover every lateral movement technique with:
English
c3y-v2 retweetledi

BREAKING: Alibaba tested 18 AI coding agents on 100 real codebases, spanning 233 days each. they failed spectacularly.
turns out passing tests once is easy. maintaining code for 8 months without breaking everything is where AI completely collapses.
SWE-CI is the first benchmark that measures long-term code maintenance instead of one-shot bug fixes. each task tracks 71 consecutive commits of real evolution.
75% of models break previously working code during maintenance. only Claude Opus 4.5 and 4.6 stay above 50% zero-regression rate. every other model accumulates technical debt that compounds with every single iteration.
here's the brutal part:
- HumanEval and SWE-bench measure "does it work right now"
- SWE-CI measures "does it still work after 8 months of changes"
agents optimized for snapshot testing write brittle code that passes tests today but becomes completely unmaintainable tomorrow.
they built EvoScore to weight later iterations heavier than early ones. agents that sacrifice code quality for quick wins get punished when the consequences compound.
the AI coding narrative just got more honest.
most models can write code. almost none can maintain it.
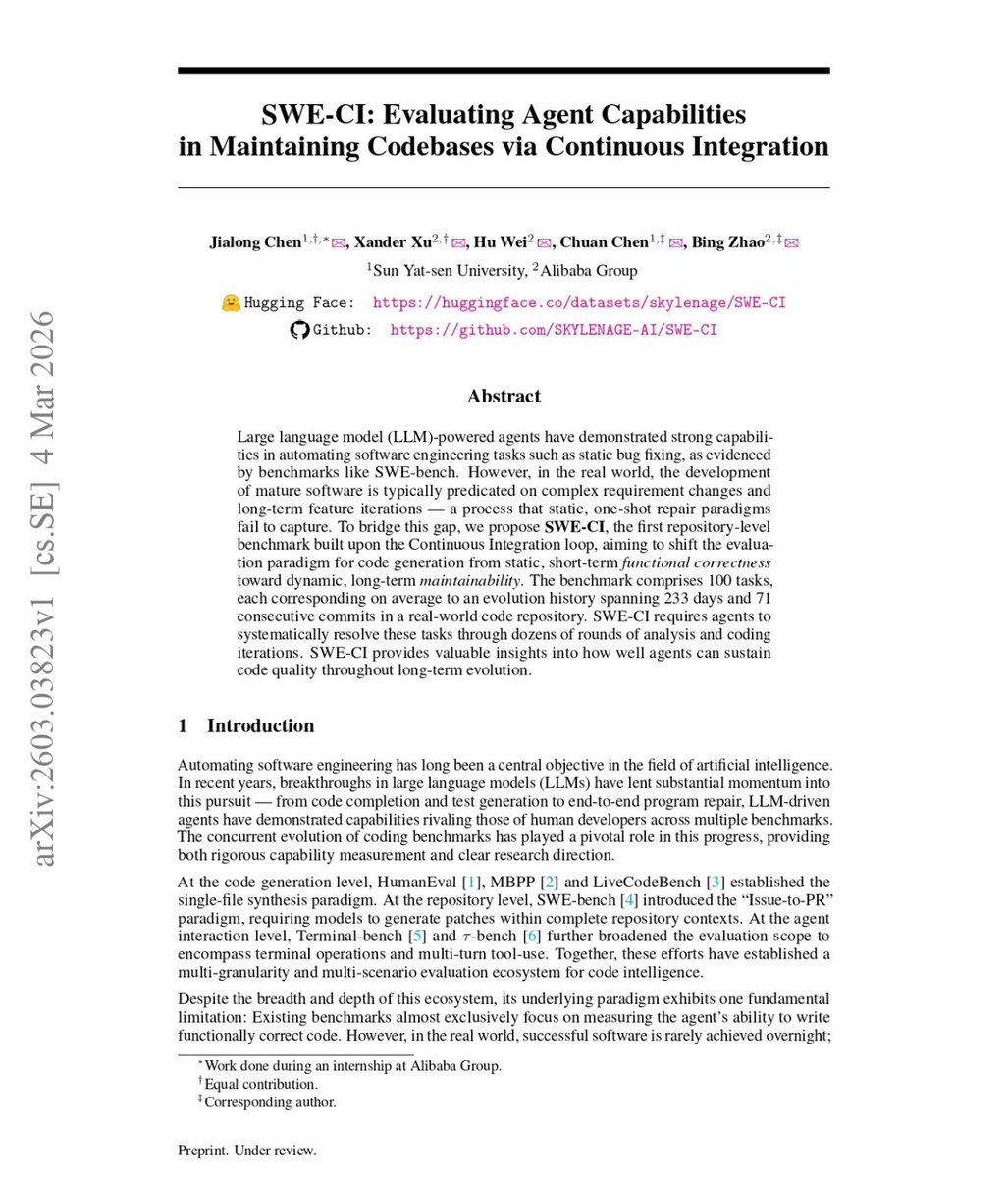
English

#aski #mansuryavas elele verdi Ankara'lıya zulmediyor, bu kadar süren kesintilerin başka bir açıklaması olamaz. Sürekli çıkıp açıklama yapacağınıza biraz iş mi yapmaya çalışsanız acaba. @askiankara
Türkçe

#aski #mansuryavas elele verdi Ankara'lıya zulmediyor, bu kadar süren kesintilerin başka bir açıklaması olamaz. Planlama , organizasyon, zamanlama hiçbirinde mi başarılı olunamaz. Olunamadığını sayenizde görüyoruz.
Türkçe

#aski Yenimahalle, Kardelen Mahallesinde her gün 00.00'da sular kesiliyor ve sabah 7.00 gibi geliyor.Ama bugün 7.00'da da gelmedi.Her gün yeni bir rezillik yaşatmaktan vazgeçmeyeceksiniz anlaşılan. #mansuryavas #fethiyasar
Türkçe

#Yenimahalle'de susuzluktan kırılıyoruz. Yaşattığınız rezillik için sizi tebrik ederim #mansuryavas ve #fethiyasar #ankarasukesintileri #sukesintisi #yenimahalle #batıkent
Türkçe

#aski Yenimahalle Kardelen Mahallesinde her gün 00.00'da sular kesiliyor ve sabah 7.00 gibi geliyor.Ama bugün 7.00'da da gelmedi.Beceriksizliğinizin faturasını neden vatandaşa kesiyorsunuz? #mansuryavas #fethiyasar Aski'yi aradığımızda da ezberletilmiş yanıtlar dısında yanıt yok
Türkçe
c3y-v2 retweetledi

Chinese authorities allege a 27-month NSA operation against the China's National Time Service Center. Initial credential theft apparently via a smartphone-messaging exploit. They relese technical details, including information about 80+ remote logins between April 11 and August 3, 2023 to map the network, followed by deployment of a framework and two documented exfiltration runs
The stated objective is long-term espionage and pre-positioning inside China’s national timing infrastructure, explicitly moving toward the high-precision terrestrial timing/navigation system. The target’s mission (generating and distributing national time) is presented as a lever over telecom synchronization, financial timestamping, energy, transport, and defense.
Entry allegedly came via an SMS service vulnerability on a foreign-brand smartphone used by staff, enabling monitoring of employees and theft of workstation credentials. Early access required repeatedly disabling endpoint antivirus. By March–April 2024 attackers upgraded to a persistent stack. Documented lateral movement hit the internet authentication server and firewall; C2 infrastructure includes nodes in the U.S. and Europe (e.g., Germany, France, Finland, Poland, Denmark).
An attempted reach into the high-precision timing system is described, but there is no evidence in the materials of service disruption. China admits to a long-dwell intrusion with credible pathways to operational impact on national time distribution, even if actual disruption is not demonstrated in the provided record.
How to assess it? In a sense, it is a response to political discussions in the US about Chinese cyberattacks and the deployment (prepositioning) of tools in US infrastructure for potential future attacks, such as sabotage. China essentially says that the US is doing the same thing. cert.org.cn/publish/main/u…




English



