CALLRED retweetledi
CALLRED
338 posts


CALLRED retweetledi
look at that app icon man. no spirit of excellence.
Mwango Capital@MwangoCapital
The Mpesa App is gone from the playstore. It has been replaced by the new My OneApp from Safaricom. Strange.
English

@callreddington Nothing yet, I'm afraid. Finding a new sponsor for such a high-value production isn't easy 🤷
English
CALLRED retweetledi
CALLRED retweetledi
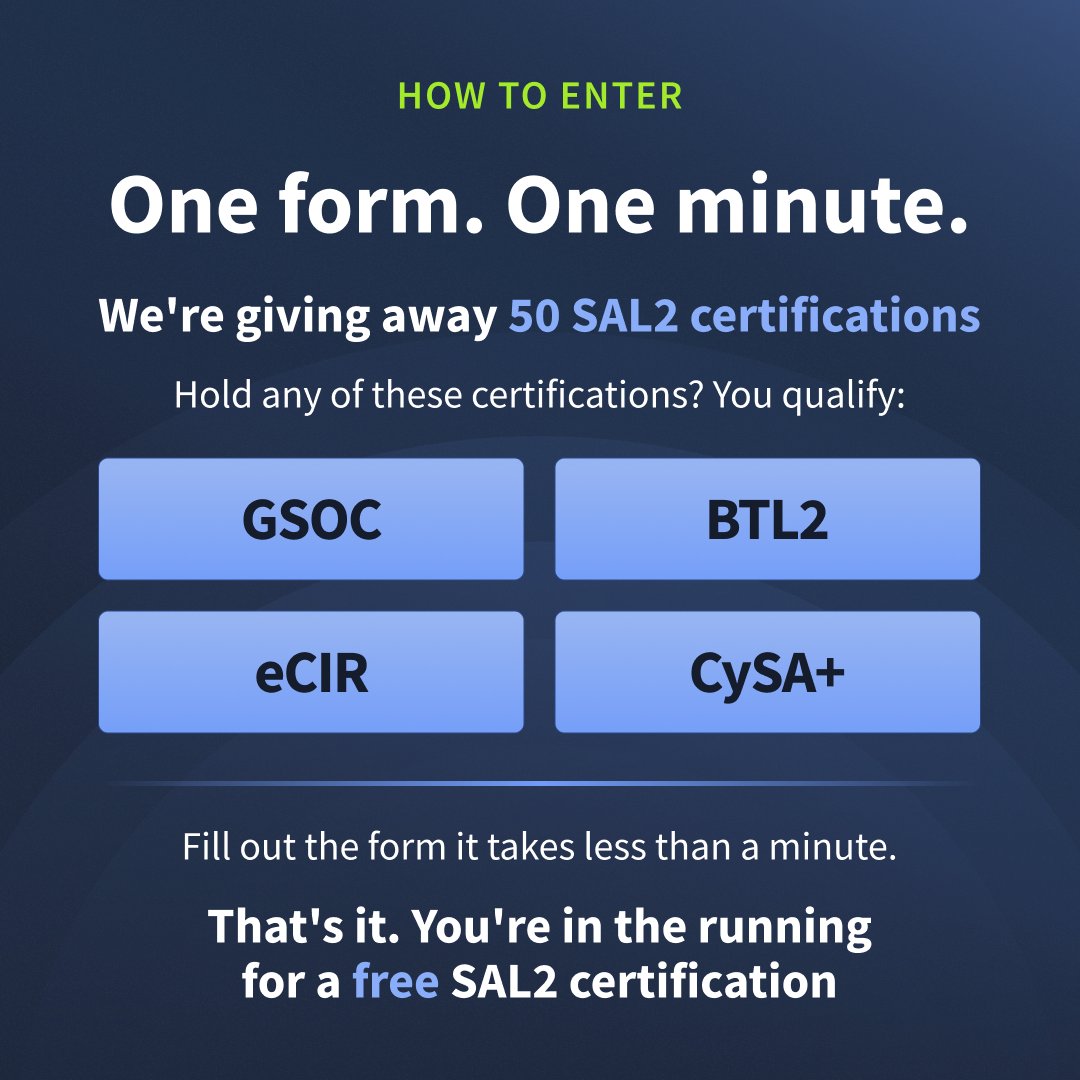
🚀 If you hold a GSOC, BTL2, eCIR, or CySA+, you already qualify. All it takes is one quick form, less than a minute to enter!
🚨 Free cert alert for defenders! We are giving away 50 FREE SAL2 certifications and you could be one of the winners🛡️
⏳ Only 3 days | 50 spots | Closes April 4th
👉 Enter now and secure your next cert for FREE! forms.gle/JPPAPQRfJc4fXG…

English

Hot Take: What if this is how the KitKat heist was done 🤔🤔 #Kitkat
Sri@__karnati
Explaining Virtual Machines
English

@prettycyb3rgirl I wish Michael Bazel would come back @IntelTechniques was awesome podcast especially on Personal Security
English

40 cybersecurity podcasts to listen during your commute
Save this for your next drive/workout 🔖🔁
Add the tech podcast you listen to in the comments.
TRUE CRIME & STORYTELLING
1. Darknet Diaries - Jack Rhysider darknetdiaries.com
2. Malicious Life - Ran Levi malicious.life
3. CYBER - VICE Motherboard vice.com/en/topic/cyber
4. Reply All (Archived) - Gimlet gimletmedia.com/shows/reply-all
DAILY NEWS BRIEFINGS
5. The CyberWire Daily thecyberwire.com/podcasts/daily…
6. Risky Business risky.biz
7. Security Now - Steve Gibson & Leo Laporte twit.tv/shows/security…
8. Smashing Security smashingsecurity.com
TECHNICAL DEEP DIVES
9. Security Weekly - Paul Asadoorian
securityweekly.com
10. Defensive Security Podcast
defensivesecurity.org
11. Brakeing Down Security
brakeingsecurity.com
12. Hacking Humans
thecyberwire.com/podcasts/hacki…
13. The Privacy, Security, & OSINT Show
inteltechniques.com/podcast.html
14. Paul's Security Weekly
securityweekly.com/shows/paul-sec…
CAREER & PROFESSIONAL DEVELOPMENT
15. Cyber Security Interviews
cybersecurityinterviews.com
16. Cyber Work Podcast - Infosec
infosecinstitute.com/podcast/
17. Breaking Into Cybersecurity Podcast
christopherimpey.com/podcast
18. Security Champions - Tom Brennan
securitychampions.com
CLOUD & MODERN INFRASTRUCTURE
19. Cloud Security Podcast
cloudsecuritypodcast.tv
20. The Cloudcast
thecloudcast.net
21. AWS Security Podcast - Ashish Rajan
ashishrajan.com/aws-security-p…
22. Kubernetes Podcast
kubernetespodcast.com
APPLICATION SECURITY
23. Application Security Weekly
securityweekly.com/shows/applicat…
24. The Secure Developer
mydevsecops.io
25. DevSecOps Podcast
devsecops.com
26. Open Source Security Podcast
opensourcesecurity.io
INCIDENT RESPONSE & FORENSICS
27. SANS Internet Storm Center
isc.sans.edu/podcast.html
28. Forensic Lunch
forensiclunch.com
29. 401 Access Denied
delinea.com/resources/401-…
30. Down the Security Rabbithole
podcast.wh1t3rabbit.net
GOVERNANCE, RISK & COMPLIANCE
31. RSA Conference Podcast
rsaconference.com/library/podcast
32. Privacy Please
invoca.com/podcast
33. CISO Series Podcast
cisoseries.com
34. Cyber Security Sauna
withsecure.com/en/whats-new/p…
SPECIALIZED TOPICS
35. Cybercrime Investigations Podcast
cybercrimepod.com
36. What the Shell?
whattheshell.buzzsprout.com
37. Click Here - BBC
bbc.co.uk/programmes/p00…
38. IRL: Online Life is Real Life - Mozilla
irlpodcast.org
39. Unsupervised Learning - Daniel Miessler
danielmiessler.com/podcast/
40. Security Unlocked - Microsoft
microsoft.com/security/blog/…
English

@prettycyb3rgirl @DarknetDiaries got me hooked up to listening to podcasts on commute it's been 4yrs
English
CALLRED retweetledi

Linux Firewall Configuration
1. Introduction
→ A firewall is a security system that controls incoming and outgoing network traffic.
→ It acts as a barrier between trusted internal systems and untrusted external networks.
→ In Linux, firewalls help protect servers, applications, and data from unauthorized access.
2. Why Firewall Configuration Matters
→ Prevent unauthorized access to your system.
→ Protect against network-based attacks.
→ Control which services are exposed to the internet.
→ Monitor and filter traffic based on rules.
→ Strengthen overall system security.
3. Types of Linux Firewall Tools
→ iptables
→ Traditional and powerful firewall tool.
→ Uses rule chains to filter traffic.
→ Operates at a low level in the kernel.
→ nftables
→ Modern replacement for iptables.
→ Simplified syntax and better performance.
→ Supports advanced rule management.
→ UFW (Uncomplicated Firewall)
→ Beginner-friendly firewall interface.
→ Built on top of iptables.
→ Easy to configure and manage.
4. Firewall Concepts
→ Rules
→ Define what traffic is allowed or blocked.
→ Example:
→ Allow SSH (port 22)
→ Block all other incoming traffic
→ Chains
→ Rules are organized into chains:
→ INPUT → Incoming traffic
→ OUTPUT → Outgoing traffic
→ FORWARD → Traffic passing through system
→ Policies
→ Default action for traffic:
→ ACCEPT → Allow traffic
→ DROP → Block traffic silently
→ REJECT → Block traffic with response
5. Using UFW (Simple Approach)
→ Enable Firewall
→ sudo ufw enable
→ Allow a Service
→ sudo ufw allow ssh
→ Allow a Port
→ sudo ufw allow 80
→ Deny a Port
→ sudo ufw deny 21
→ Check Status
→ sudo ufw status
6. Using iptables (Advanced Control)
→ Allow SSH
→ iptables -A INPUT -p tcp --dport 22 -j ACCEPT
→ Allow HTTP
→ iptables -A INPUT -p tcp --dport 80 -j ACCEPT
→ Drop All Other Traffic
→ iptables -A INPUT -j DROP
→ Save Rules
→ iptables-save
7. Using nftables (Modern Approach)
→ Create Basic Rule
→ nft add rule inet filter input tcp dport 22 accept
→ List Rules
→ nft list ruleset
→ Flush Rules
→ nft flush ruleset
8. Common Firewall Configuration Strategy
→ Allow essential services (SSH, HTTP, HTTPS).
→ Deny all unnecessary ports.
→ Restrict access to trusted IP addresses.
→ Enable logging for suspicious traffic.
→ Apply least privilege principle.
9. Firewall Logging
→ Monitor blocked and allowed traffic.
→ Helps detect attacks or misconfigurations.
→ Example (UFW logging):
→ sudo ufw logging on
10. Best Practices
→ Always allow SSH before enabling firewall (avoid lockout).
→ Use default deny policy.
→ Regularly review firewall rules.
→ Keep firewall tools updated.
→ Combine firewall with intrusion detection tools.
11. Tip
→ Linux firewalls are essential for network security.
→ UFW is simple and beginner-friendly.
→ iptables provides deep control.
→ nftables offers modern and efficient rule management.
→ Proper configuration protects systems from unauthorized access.
📘 Linux Mastery Ebook
→ Master Linux internals, security, firewall configuration, system monitoring, and architecture step-by-step.
🔗 Grab the Linux Mastery Ebook:
codewithdhanian.gumroad.com/l/dynwdc

English

@DrKanyuira Raspberry PI could be a viable option, Opensense could run on a microtik if you want DIY
English

@callreddington I just need a router that can run a VPN, not necesarily trave one.
English
CALLRED retweetledi
CALLRED retweetledi

The best LINUX resources that are FREE to learn in 2026:
1. Linux Foundation Training
training.linuxfoundation.org/training/intro…
2. Linux Journey
linuxjourney.com
3. Ubuntu Tutorials
ubuntu.com/tutorials
4. Red Hat Training Resources
developers.redhat.com/learn
5. GNU Documentation
gnu.org/manual
6. OverTheWire Bandit (Linux Wargames)
overthewire.org/wargames
7. The Linux Command Line Book
linuxcommand.org/tlcl.php
8. MIT Missing Semester (Linux & CLI)
missing.csail.mit.edu
9. DigitalOcean Linux Tutorials
digitalocean.com/community/tuto…
10. Linux From Scratch
linuxfromscratch.org
11. Arch Linux Wiki
wiki.archlinux.org
12. freeCodeCamp Linux Course
freecodecamp.org/news/tag/linux
13. Linux Survival
linuxsurvival.com
14. NDG Linux Essentials
netacad.com/courses/linux-…
15. Bash Guide
tldp.org/LDP/Bash-Begin…
Add more link in the comment section to help others study.
English


@tryhackme Almost had me,
Guess I will go outside and see the new 12T trailer of kitkat parked at the neighbors
English
CALLRED retweetledi