
David Odes
12K posts


@chiefdavidsays
Cybersecurity & Privacy Researcher, Speaker and Instructor. Founder @WebSecurityLab. Tweets on how technology, cybersecurity and policy impact society.



After almost twenty years on the platform, EFF is logging off of X. This isn’t a decision we made lightly, but it might be overdue. 🧵(1/5)






I’ve probably setup sshkeys on a server a 100 times but for some reason, I have to google/ask AI each time I need to do it again.




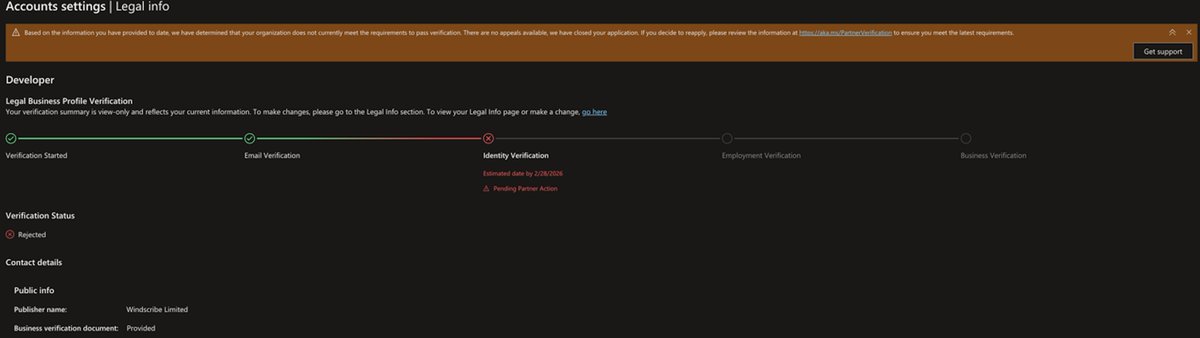
Microsoft suspended the developer account for WireGuard (and also VeraCrypt). Why? Literally nobody knows. Presumably it's because Microsoft hates everyone and wants us all to suffer.



Three weeks ago, a threat actor called ByteToBreach walked through Nigeria’s financial infrastructure using a single unpatched vulnerability at Sterling Bank as the door. What followed was nine days of undetected access with core banking data, sensitive customer information and employee records exfiltrated before the actor pivoted into Remita, Nigeria’s government payment backbone. From Remita they took everything. 3TB of data. Including sensitive and personal information of over a million Nigerians (across both breaches). I spent the last week reconstructing the full attack chain from the artefacts the actor published. I have now produced a narrative investigation on my new substack and a technical analysis on @WebSecurityLab covering the complete breach from the first CVE exploit to the published HSM key directory. This was published in the hope that the lessons from these events prove more durable than the events themselves. Security failures of this scale are painful. They are also, when documented carefully and honestly, among the most valuable contributions one can make to an ecosystem that is still maturing. Nigeria’s banking story is one of the most compelling in the world. It deserves a security culture to match. Read the full investigation here: securityintelligence.substack.com/p/sterling-ban…

Nigeria have Any Hacking Group or Even State Actors?

@pcaversaccio @eiritana I would be interested in seeing data that supports the idea that DPRK workers are stopped dead in their tracks upon being required to insult Kim.