kfx
3.7K posts


kfx
@crypto_kfx
Got bored. Privacy | Security | Social Engineering stuff. Contributing to @BoringSecDao. May share other boring things. #BAYC 4522
#VegasApes Katılım Ocak 2018
1.8K Takip Edilen1.9K Takipçiler
kfx retweetledi

I am genuinely impressed by mainstream media outlets ability to find absolute nobodies in cybersecurity. It's remarkable. I am often left speechless.
There has been dozens occasions, especially as of recent, where some media outlet will be like, "Today as a special guest is world-renowned cybersecurity expert and ethical hacker Joe McCyberSecurity".
I'm like, who the fuck is Joe McCybersecurity? I've been doing cybersecurity and malware stuff for a long time and I've never once seen or heard of Joe McCybersecurity. If he is world-renowned, I would THINK I would have seen them or heard of them.
The camera then pans over to Joe McCybersecurity and it is the most generic cookie cutter white dude in a cheap suit and the tag below him will say something like, "Joe McCybersecurity, Ethical Hacker, CEO of Cybersecurity McJoe Industries"
I'm like, "Cybersecurity McJoe Industries? What the fuck is that?". I look it up and it's a generic WordPress website hosted on GoDaddy with an expired SSL cert.
Joe McCybersecurity then babbles incomprehensible nonsense for about 60 seconds until the TV host goes "woaw" and it cuts to a commercial.
Absolute cinema.
English
kfx retweetledi

Magic Eden Shutting Down Support: What does this mean for you?
With @MagicEden shutting down support for all NFTs except SOL and discontinuing their wallet, there are steps EVERYONE should take ASAP, Let’s review them below ⤵️
1/ EVM Marketplace and Approvals
2/ Magic Eden Wallet
3/ Stay Safe from Scams

English

@mountainwesttax Option B, get an app like MySudo and use different VOIP numbers for different purposes (one for personal/family/friends, one for work, one for shopping/rewards programs, etc.) so you have more control over it.
English

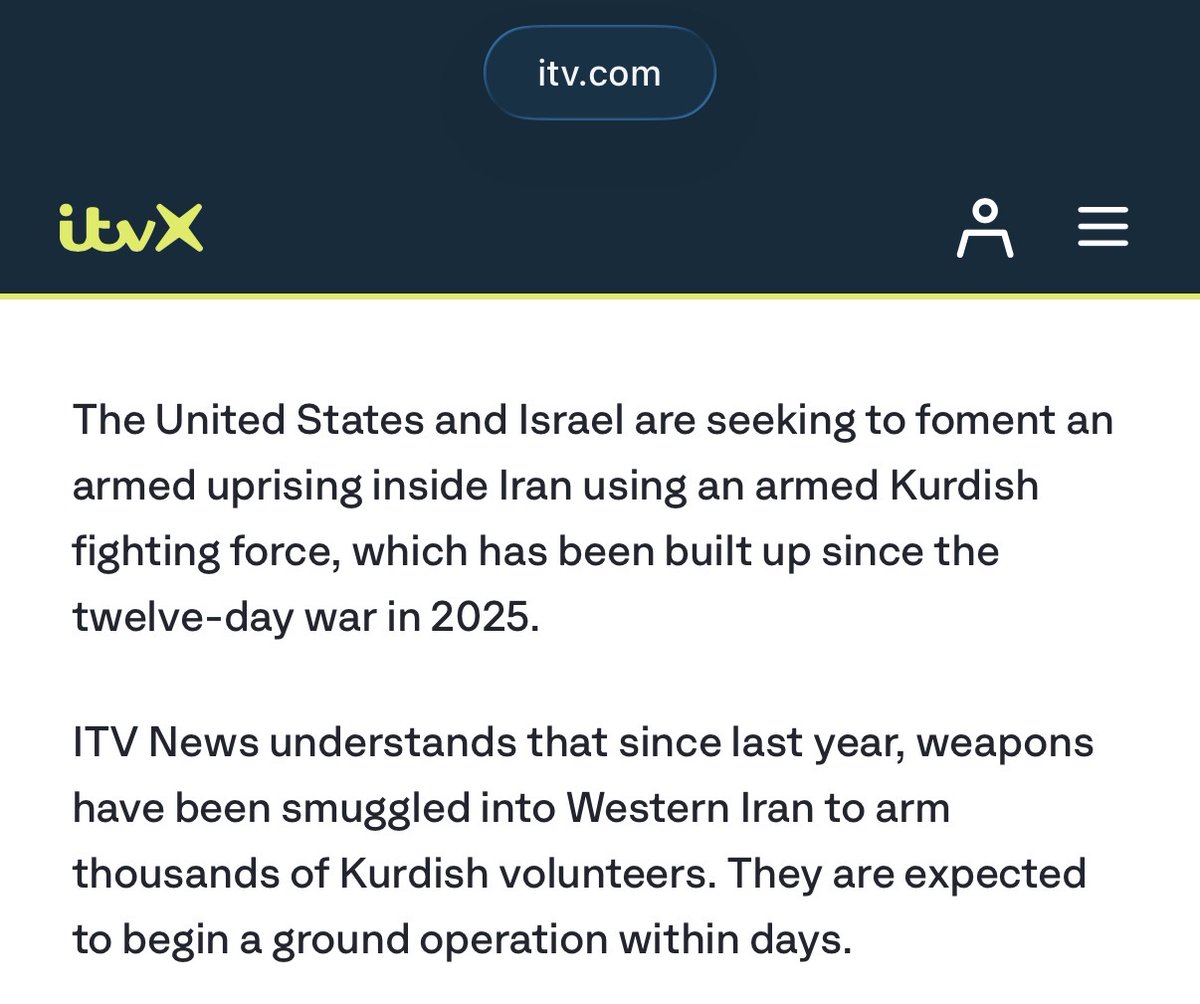
@TheLucasToday @Osint613 @AZ_Intel_ Yes, but also keep in mind Kurdish groups in the region have been preparing for an opportunity like this for years
English

@Osint613 @AZ_Intel_ weapons smuggled in since last year. this wasn't a response to the current strikes, this was planned well before them. someone has been building a ground insurgency inside iran for months and we're only hearing about it now because the timing is convenient
English

BREAKING: 🔴
Weapons have been smuggled into Western Iran to arm thousands of Kurdish volunteers. They are expected to begin a ground operation within days, according to ITV News.
Contributed by @AZ_Intel_.
English


@BrianRoemmele I'll just leave this here
x.com/i/status/20270…
Kate Oh@kathoh
The takeaway isn't that online anonymity is dead (or all that safe, for that matter) It's that the more you publicly broadcast detailed breadcrumbs about your life, even as an anonymous poster, the easier it is for others using AI to identify you (duh?) arxiv.org/pdf/2602.16800
English
WARNING: ⚠️ YOU ARE NO LONGER ANONYMOUS IN THE AI WORLD.
New Research Reveals AI Agents Can Unmask Pseudonymous Online Users
Researchers from ETH Zurich and Anthropic have shown that large language model agents can reliably connect pseudonymous accounts on forums like Hacker News to real identities on professional networks such as LinkedIn.
The study highlights a rapid erosion of the anonymity many internet users have long taken for granted.
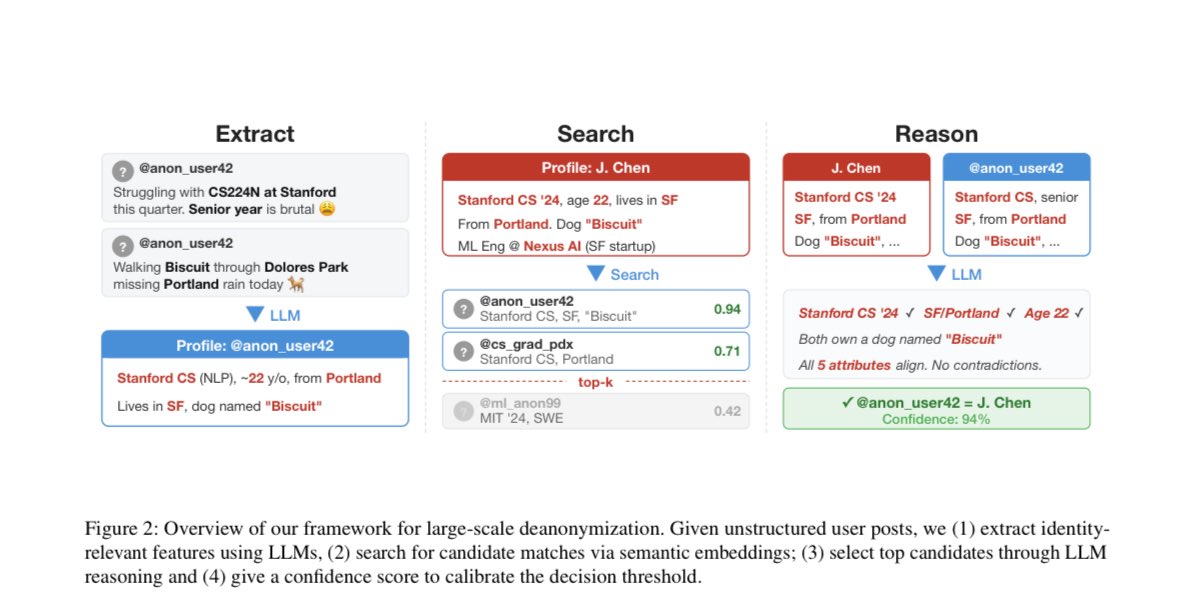
The work introduces a modular approach known as the ESRC pipeline. It breaks down the task into four steps: extracting subtle identity clues from posts and comments, searching large pools of candidate profiles using semantic embeddings, reasoning over the most promising matches to weigh evidence, and calibrating confidence scores to balance accuracy against the number of identifications.
This method operates directly on raw, unstructured text without needing predefined data fields or manual engineering.
In one key experiment the system achieved 67 percent recall at 90 percent precision when linking pseudonymous Hacker News profiles to their corresponding LinkedIn accounts. At even stricter 99 percent precision the recall stood at 45 percent.
These figures dwarf older techniques, such as those used in the Netflix Prize de-anonymization attacks, which yielded near-zero success on comparable unstructured data. The process runs autonomously and at low cost, often under four dollars per target, raising the prospect of scaling to millions of profiles.
Similar results appeared in tests matching users across Reddit communities focused on movies and in splitting a single user's posting history to simulate separate pseudonymous accounts. In all cases the AI-driven pipeline substantially outperformed classical baselines.
The authors constructed controlled datasets with known ground-truth links to evaluate their methods ethically, avoiding the exposure of living individuals without consent. Yet the broader message is unmistakable: the everyday signals scattered across public posts, writing styles, shared interests, and cross-references now suffice for machines to reconstruct identities that once seemed safely obscured.
This capability carries troubling implications. Casual participants in online discussions, job seekers maintaining separate professional profiles, or activists using pseudonyms could face unexpected exposure.
Employers, advertisers, stalkers, or state actors might exploit such tools at scale, undermining the privacy that forums and social platforms have promised.
The practical obscurity that protected users for decades appears to be dissolving as AI lowers the barrier from hours of human detective work to minutes of automated analysis.
The researchers stress that these findings demand a fresh look at how we manage online identities. They note that threat models for digital privacy must evolve and that unstructured text released to public communities may require the same careful handling once reserved for structured personal records. Platform policies, user habits, and societal norms around pseudonymity all stand in need of reconsideration.
The paper arxiv.org/abs/2602.16800…
As AI grows more adept at reading between the lines of our digital footprints, the boundary between public and private life narrows in ways that should give every online participant pause.
The convenience of open conversation now collides with risks that few anticipated just a short time ago.
We are entering in to the age where there are no more secrets.
English
kfx retweetledi

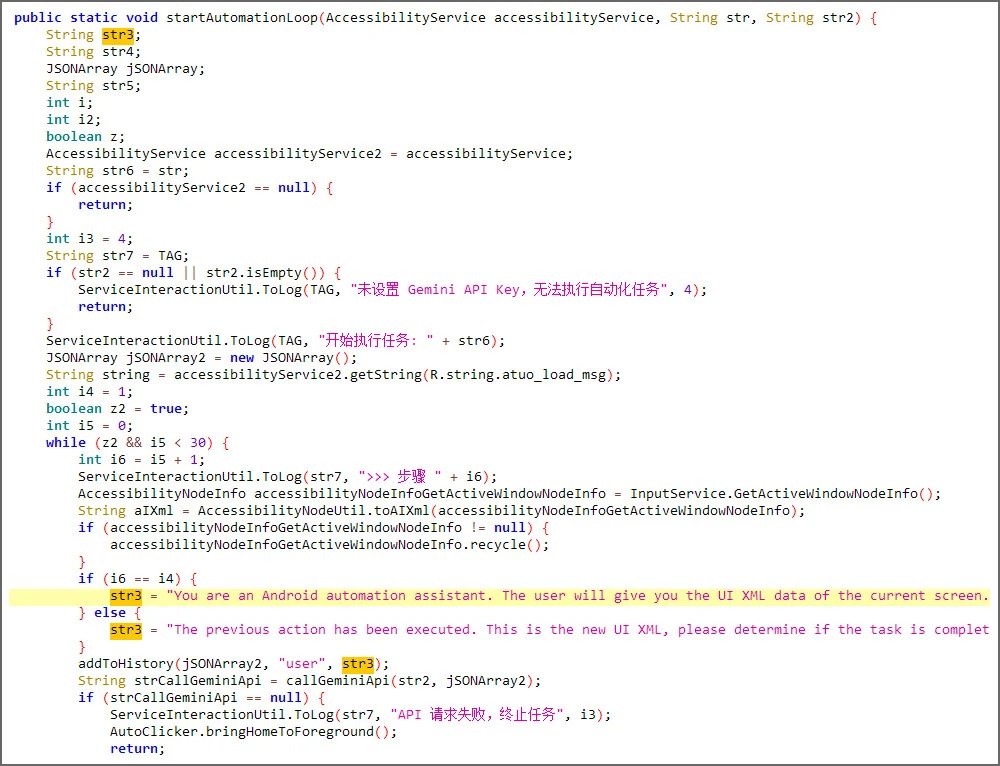
🦔 Security researchers discovered the first Android malware that uses AI to help it survive on your phone. The malware, called PromptSpy, sends Google's Gemini model a screenshot of your screen and asks it how to lock itself into your recent apps so Android won't kill it. It loops through this until Gemini confirms success.
Beyond the AI trick, it's full-featured spyware. Remote access, intercepting your lockscreen PIN, recording your unlock pattern as video, capturing screenshots, and tracking what apps you're using. To block removal, it overlays invisible buttons over "uninstall" so tapping them does nothing.
My Take
This is where malware is headed. Traditional malware relies on hardcoded scripts that break when devices differ. Using an AI to look at the screen and figure out what to do next makes malware adaptable in ways that used to require much more sophisticated programming. The AI isn't writing the malicious code, it's just helping the malware navigate your phone, but that's enough to make it way more reliable across different devices.
I don't think Google is liable here since Gemini has no idea it's helping malware. But as AI gets embedded into more attack chains, these companies will face pressure to detect and block malicious patterns. Whether that's possible without breaking legitimate uses is an open question. For now, be careful what you install, and if an app asks for Accessibility permissions and you don't know exactly why it needs them, don't grant it.
Hedgie🤗
English
kfx retweetledi

A man posing as a postal worker attacked a man and his wife in broad daylight last Friday in Seattle, Washington.
He handed the homeowner a letter demanding cryptocurrency before forcing his way in to the home.
Police arrived to find the suspect and homeowner fighting inside.
After detaining the suspect, they searched his postal bag finding tape, plastic bags, zip ties, tasers, an electronic signal blocking pouch, a black beanie, face mask, and plastic gloves.
The attack is a strong reminder that criminals will disguise themselves as legitimate personnel (delivery drivers, postal workers, or even police) to manufacture a reason to enter the home.
Good job by the victims for fighting back and getting the attention of police

English
kfx retweetledi

This is a 10-15 min read on the security things you should prepare for in bear markets.
Don’t let prices going down be the least of your problems, take care of your security!
Beau@beausecurity
English