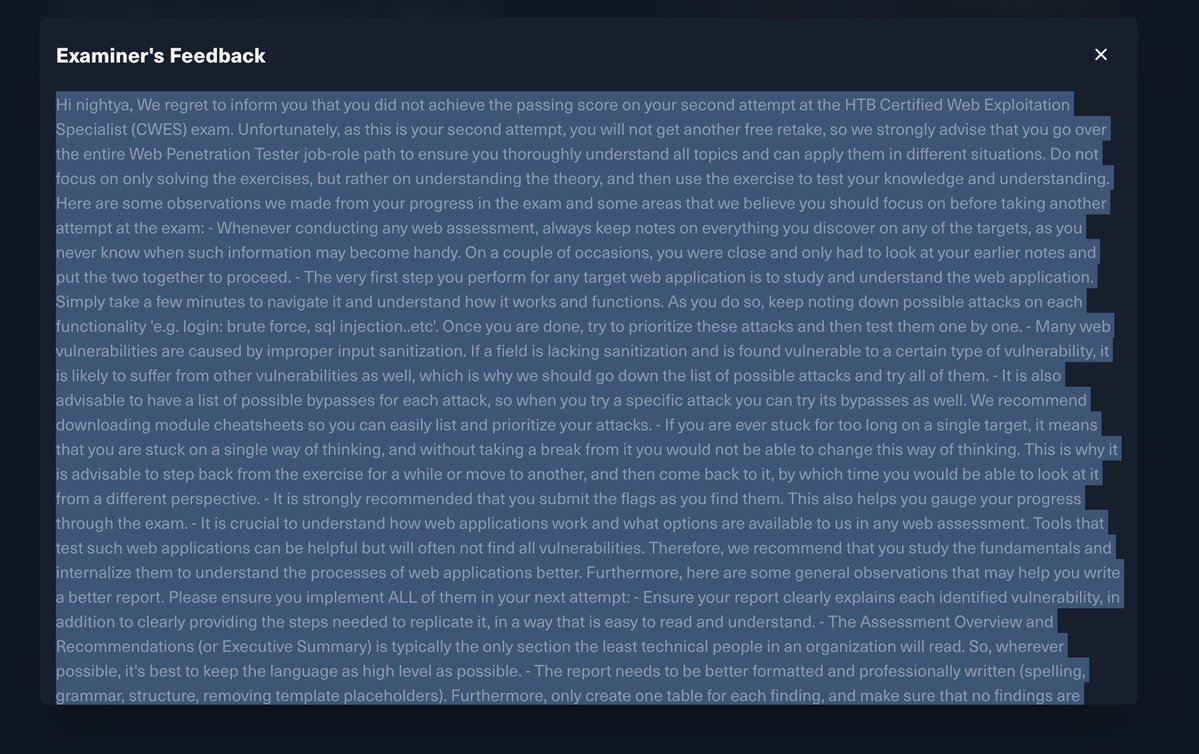
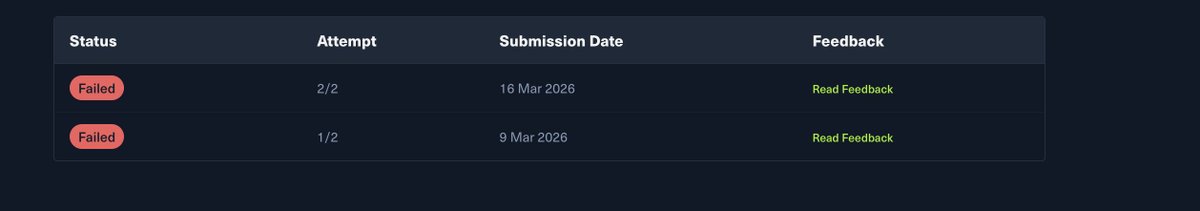
@Tur24Tur @hackthebox_eu Gratz, I'm also going to do it within 2 weeks. I completed the modules. Need to do some things first to prepare better for the exam
English
Beucalt
2K posts








We’re expanding Trusted Access for Cyber with additional tiers for authenticated cybersecurity defenders. Customers in the highest tiers can request access to GPT-5.4-Cyber, a version of GPT-5.4 fine-tuned for cybersecurity use cases, enabling more advanced defensive workflows. openai.com/index/scaling-…