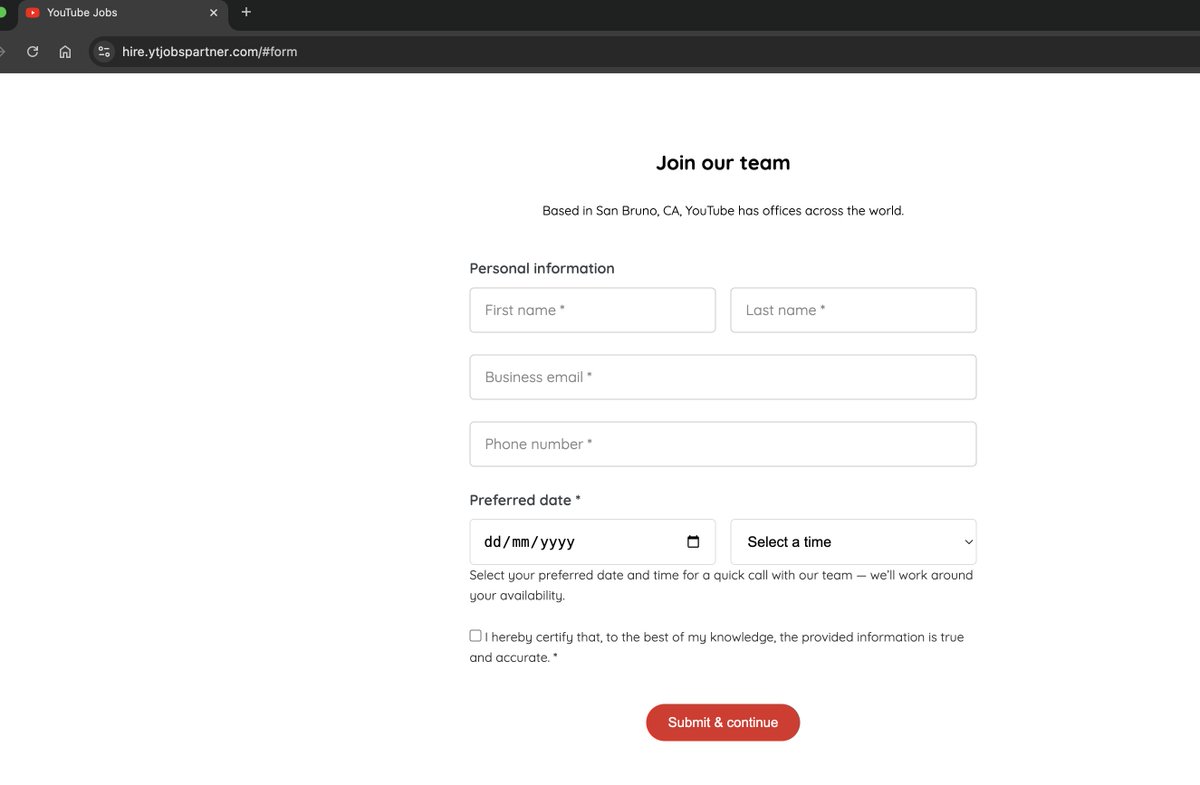
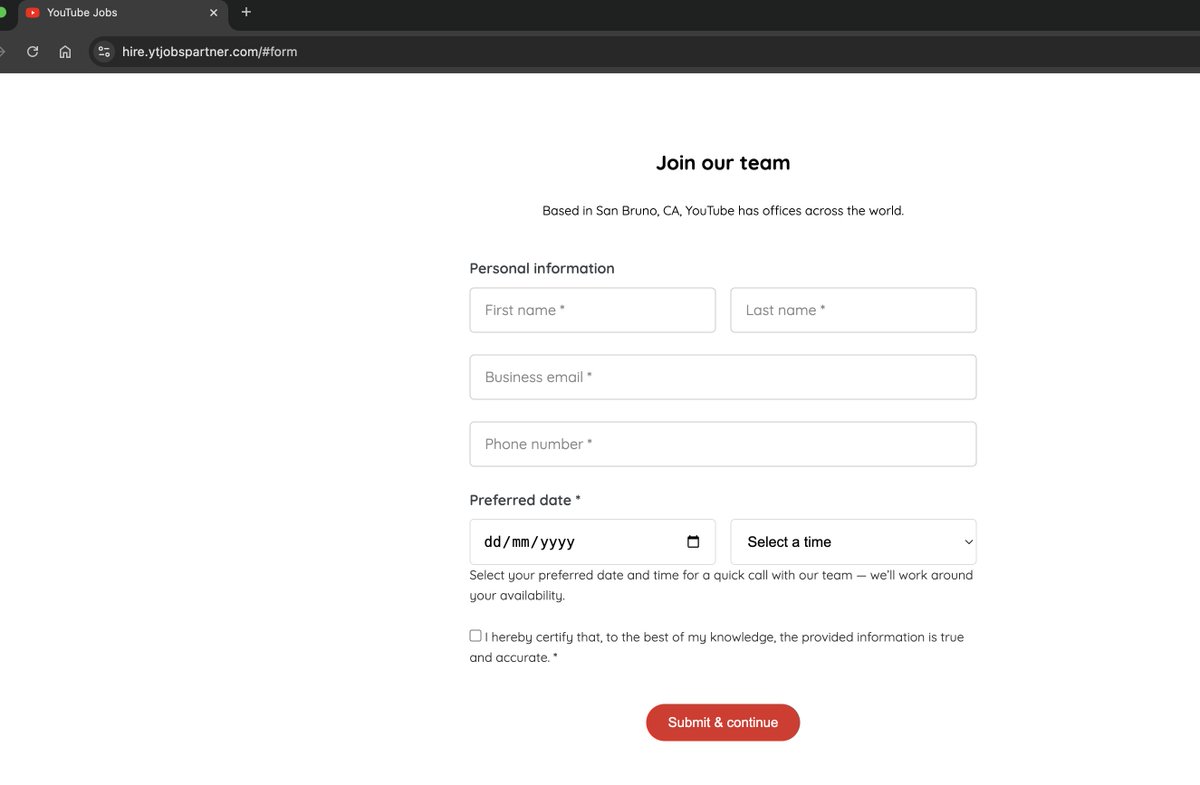
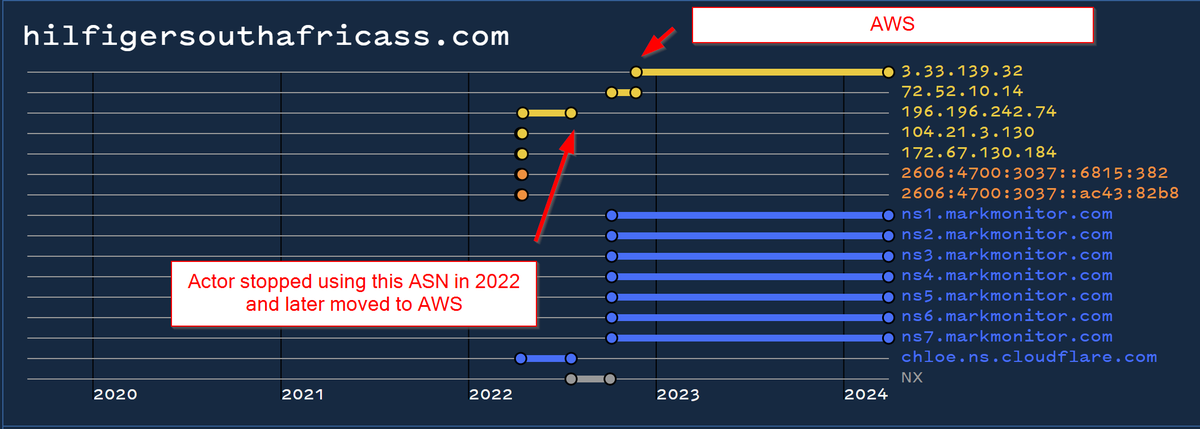
Recruitment #Phishing for well-known orgs like Google, Meta, YouTube
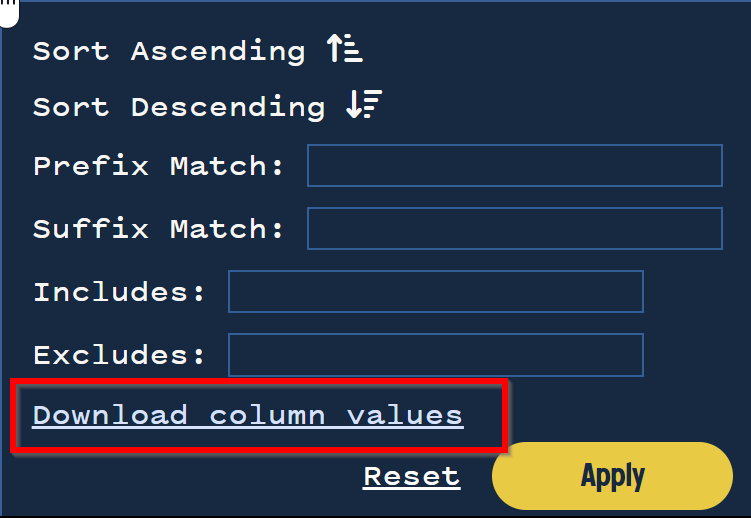
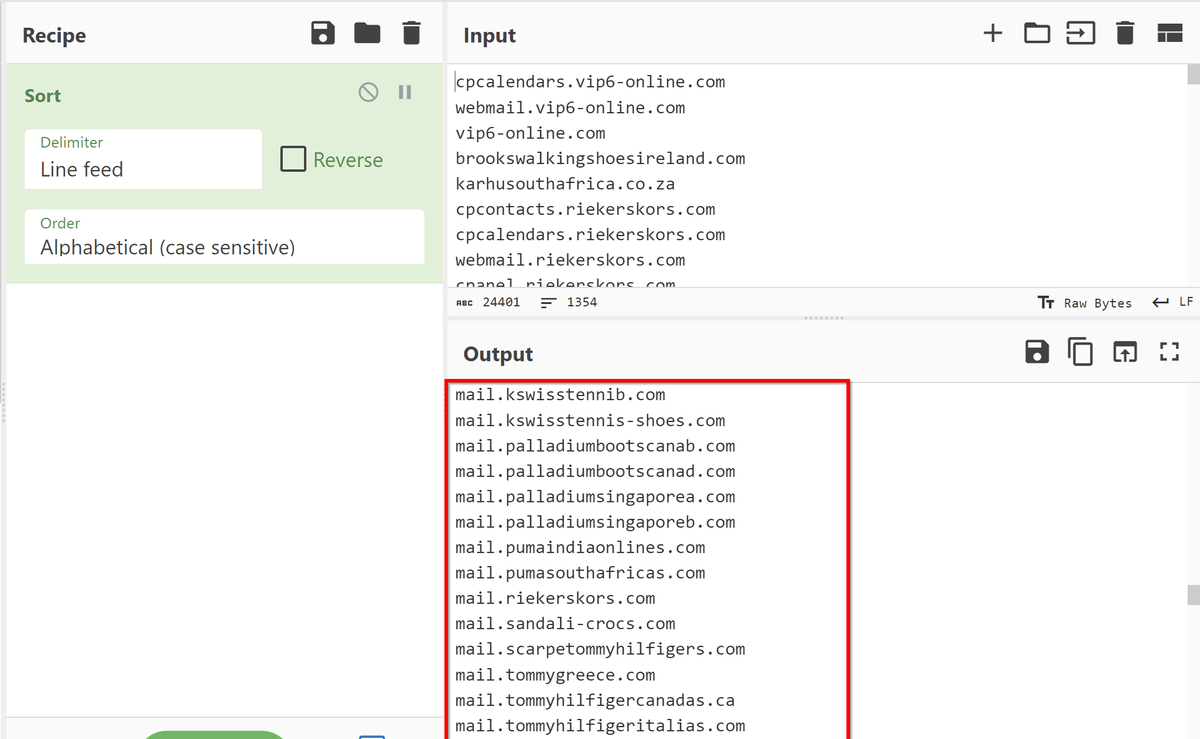
Full list of IOCs is here pastebin.com/K8EezySa
ytjobsunit[.]com
ytjobspartner[.]com
ytjobsmember[.]com
metaworkrooms-hiring[.]com
metaworkrooms-careers[.]com

English
ᴘᴀʀᴛʜɪ
1.4K posts

@cyber__sloth
Intelligence Analyst @Atlassian



















blogs.blackberry.com/en/2023/11/aer… [redacted] [redacted] IOCs? LOL, [redacted] [redacted]. I [redacted] [redacted] infrastructure. IOCs: http[:]//151.106.27[.]217/benefits3.dotm benefits.docx 2bb4b077eac5db416287b790d23eb4fd benefits3.dotm b2765a5a5ae989f611abd7a23cefd088


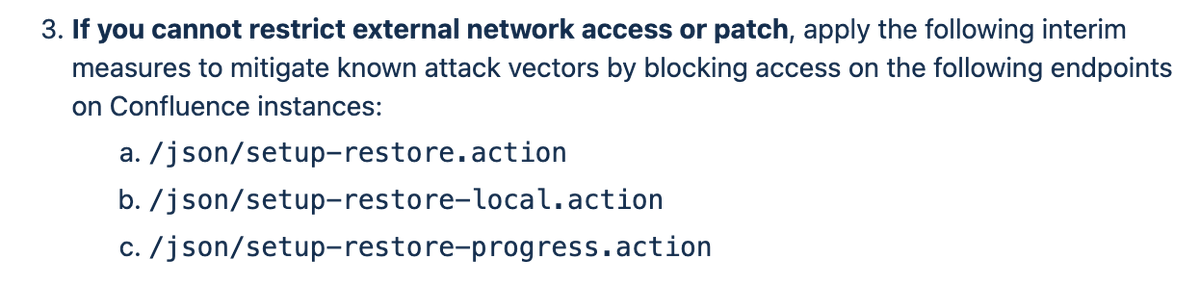
🚨Confluence exploit (CVE-2023-22518) Leads to C3RB3R Ransomware🚨 ➡️Exploit source: 193.187.172.73 ➡️Download & Exec: http://193[.]187[.]172[.]73/tmp[.]1u ➡️Lateral Movement: Attempts to spread over SMB/445 ➡️Extension: LOCK3D h/t @GreyNoiseIO