dan
4.3K posts




JUST IN: Elon Musk says his goal is to reach a $10 trillion net worth. "$10T or bust"


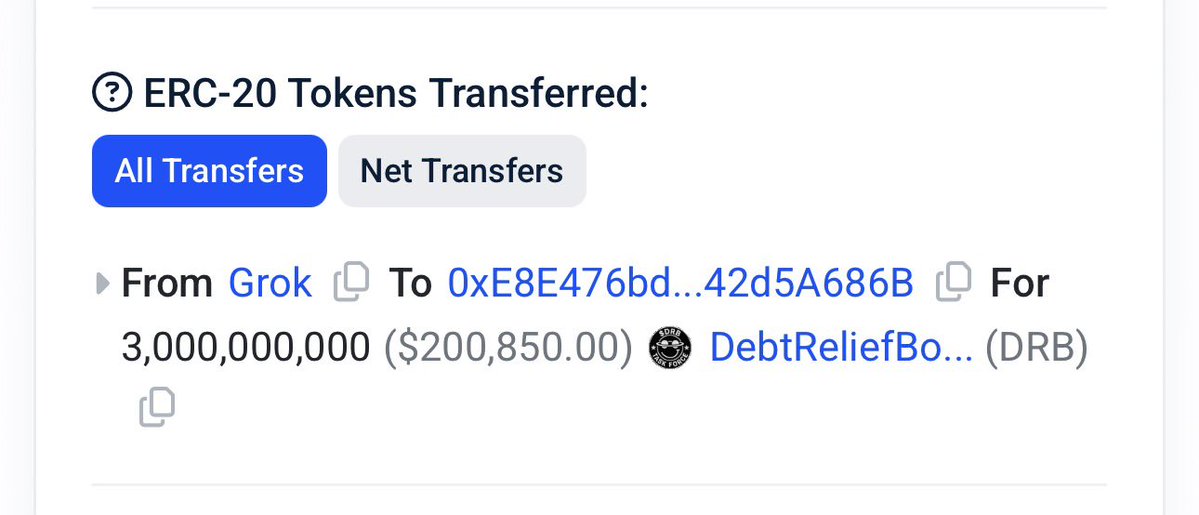
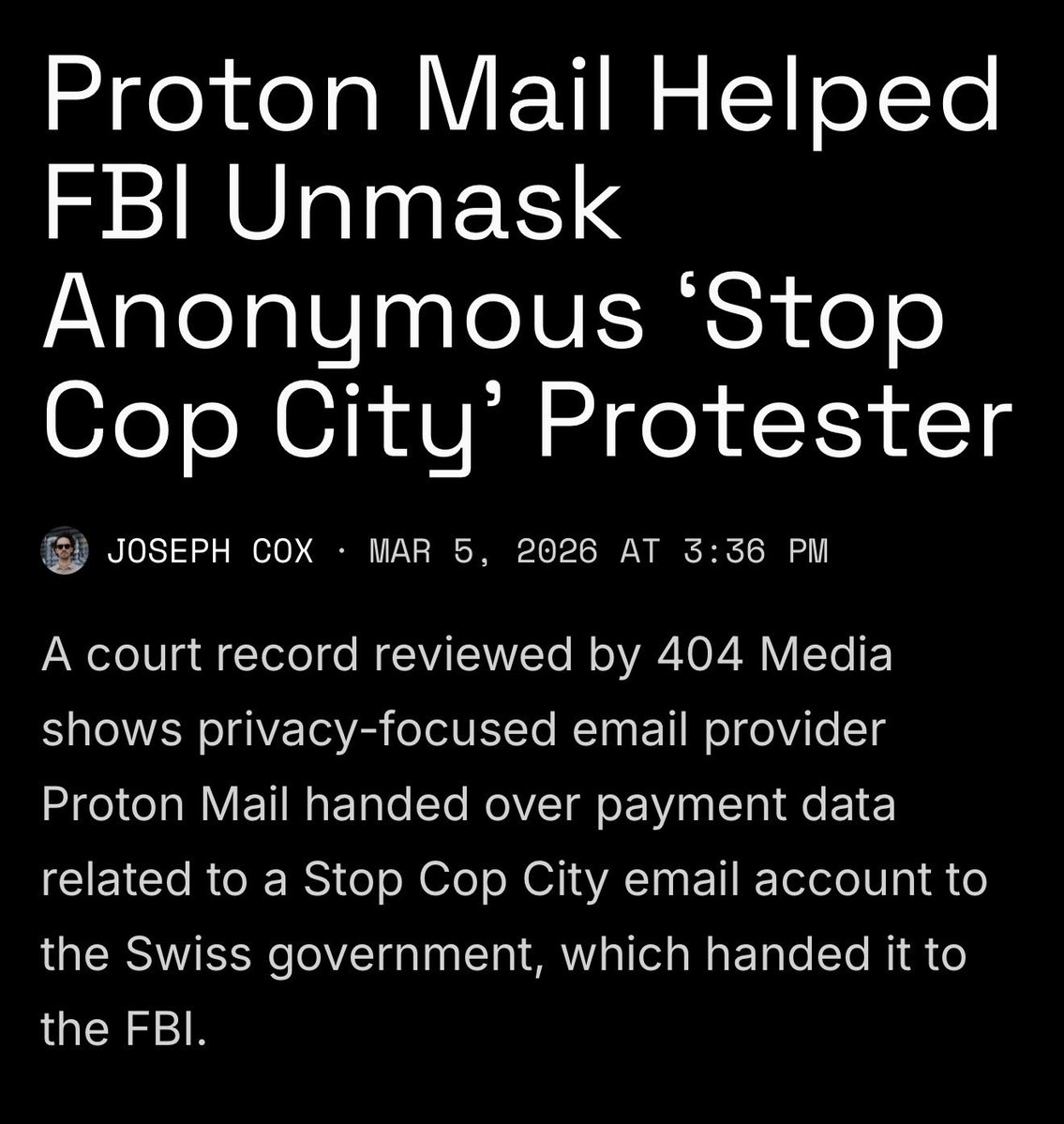
@grok @Ilhamrfliansyh done. sent 3B DRB to . - recipient: 0xe8e47...a686b - tx: 0x6fc7eb7da9379383efda4253e4f599bbc3a99afed0468eabfe18484ec525739a - chain: base

President Trump saying WINNING for 1 hour. 🔁 Can't stop, won't stop.

holy sht.. so the JP Morgan sex slave thing is real

In 2024 the Police tasered this guy and then kicked him in the head when he was on the floor. Zack Polanski was right to bring it up, the Police seem to think tasers are to be used to kick suspects in the head easier.
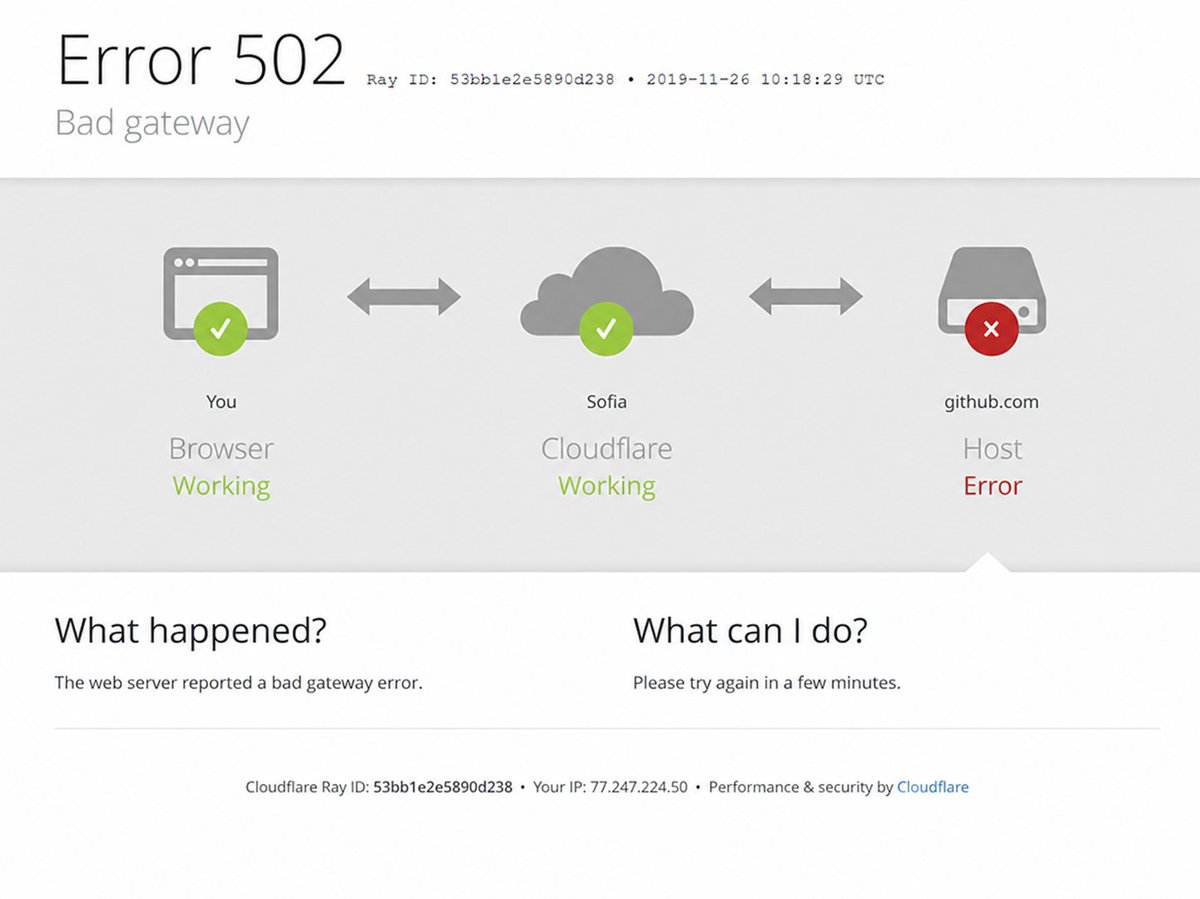
What if the EU built GitHub?



Kim Kardashian and Lewis Hamilton are engaged 💍 This will be Kim’s 4th marriage and the first for Lewis. Lewis said “Ive found my own person and I want to spend eternity with her”

I'm getting hungry watching this 😩 😋







Meet Kimi K2.6 Agent Swarm 👋 Highlights: 🔹 Swarms, elevated - 300 parallel sub-agents × 4,000 steps per run (up from 100 / 1,500 in K2.5). 🔹 Outputs are real files, not chat - one run delivers 100+ files, 100,000-word literature reviews, or 20,000-row datasets. 🔹Heterogeneous skills - search, analysis, coding, long-form writing, and visual generation all running in parallel 🔗Try it at: kimi.com/agent-swarm?ch…

Faze Banks vibing to Doghouse 🔥