
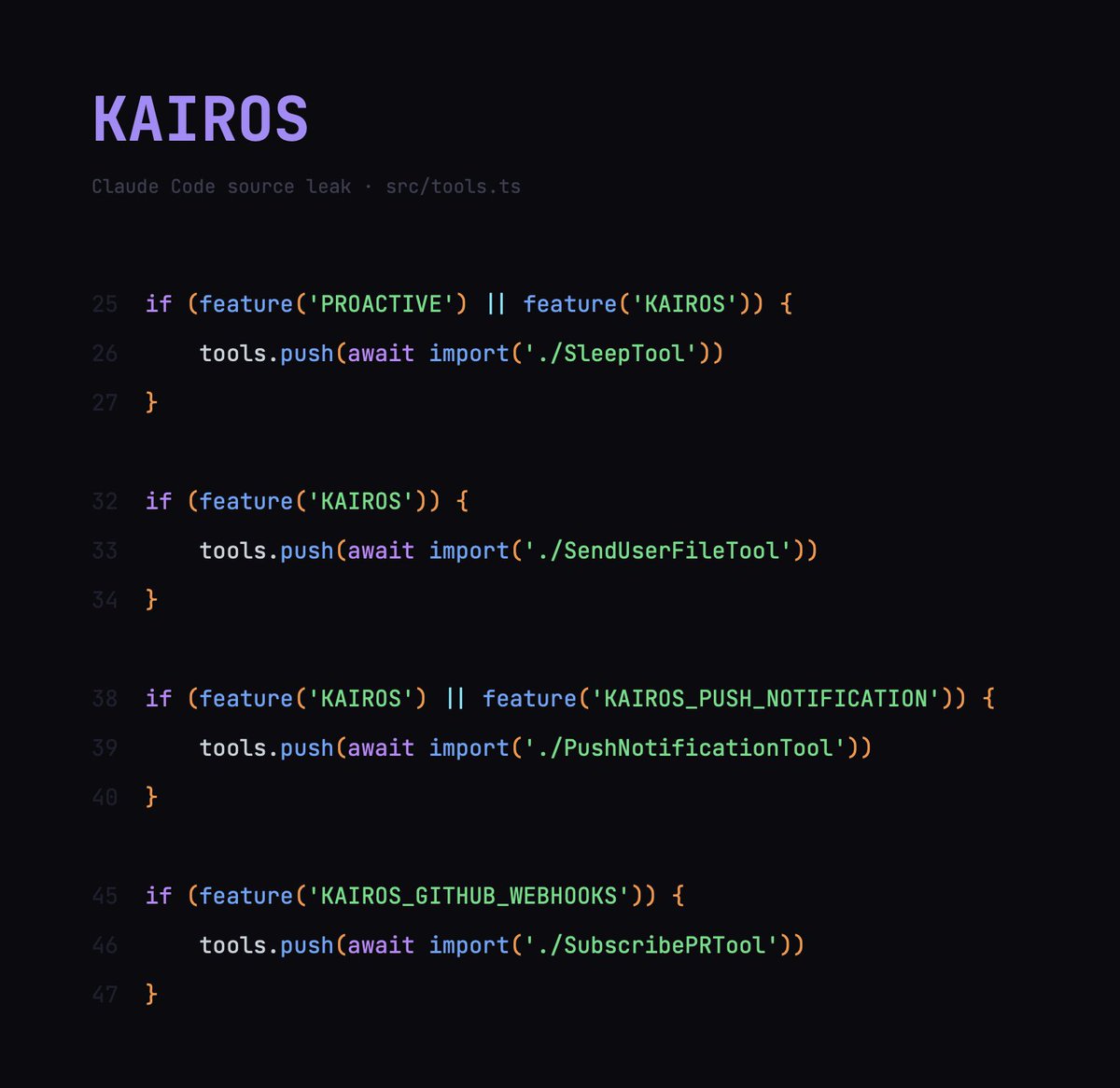
Claude code source code has been leaked via a map file in their npm registry! Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip
David Gil
6.1K posts


@dgilperez
Curious about almost everything. 2x proud papá. 2x co-founder CTO in digital health, longevity, AI, SaaS. Vibecoding either our obsolescence or our overcoming.

Claude code source code has been leaked via a map file in their npm registry! Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip



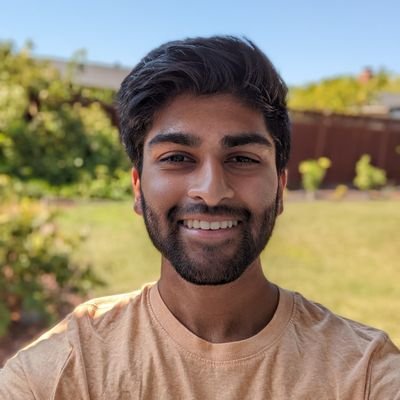



My friend @philfung was inspired by the man who built a personalized cancer vaccine for his dog, so he wrote a guide to DIY mRNA vaccine production. Phil used to run a lab startup, and the guide covers the entire process - from sequencing to synthesis, using open-source software and benchtop lab equipment. Note: This is for educational purposes only and is not intended for medical use um unless you have cancer
Every LLM from any lab today traces back to this guy, who was the only person at OpenAI pushing for pretraining transformer language models. He built GPT-1. After that did others see the potential. He invented it, and almost none of the so called AI experts even know his name.

Today we're introducing TRIBE v2 (Trimodal Brain Encoder), a foundation model trained to predict how the human brain responds to almost any sight or sound. Building on our Algonauts 2025 award-winning architecture, TRIBE v2 draws on 500+ hours of fMRI recordings from 700+ people to create a digital twin of neural activity and enable zero-shot predictions for new subjects, languages, and tasks. Try the demo and learn more here: go.meta.me/tribe2



🔴 Hacienda obliga a los propietarios de viviendas okupadas a tributar por los alquileres no cobrados en su declaración de la Renta. ❌ La interposición de una demanda de desahucio a los inquilinos que no cumplen su contrato no elimina la obligación... larazon.es/economia/hacie…

LiteLLM HAS BEEN COMPROMISED, DO NOT UPDATE. We just discovered that LiteLLM pypi release 1.82.8. It has been compromised, it contains litellm_init.pth with base64 encoded instructions to send all the credentials it can find to remote server + self-replicate. link below

Cursor can now search millions of files and find results in milliseconds. This dramatically speeds up how fast agents complete tasks. We're sharing how we built Instant Grep, including the algorithms and tradeoffs behind the design.