Sabitlenmiş Tweet

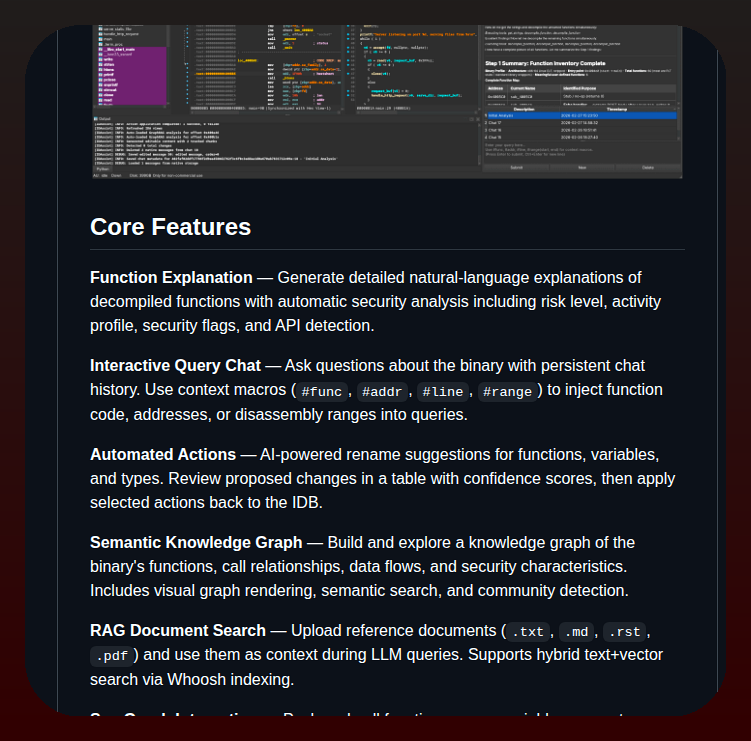
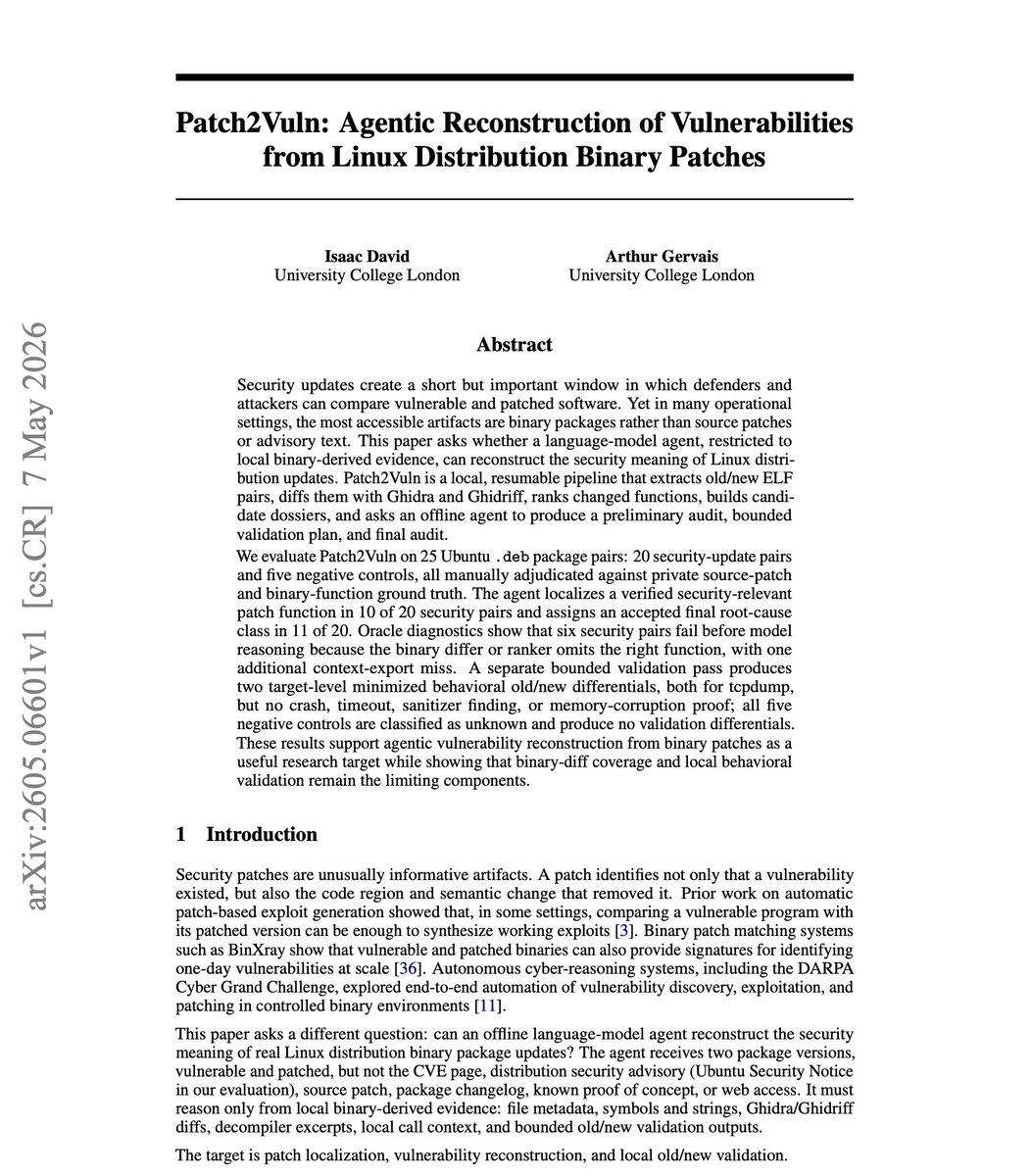
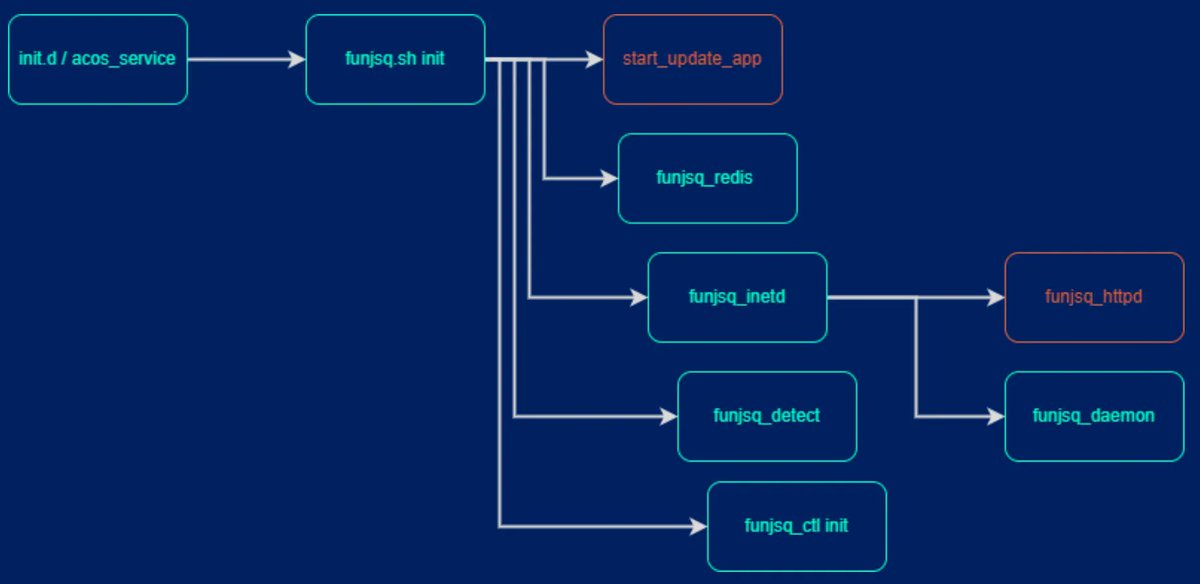
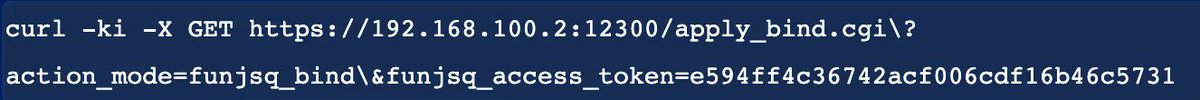
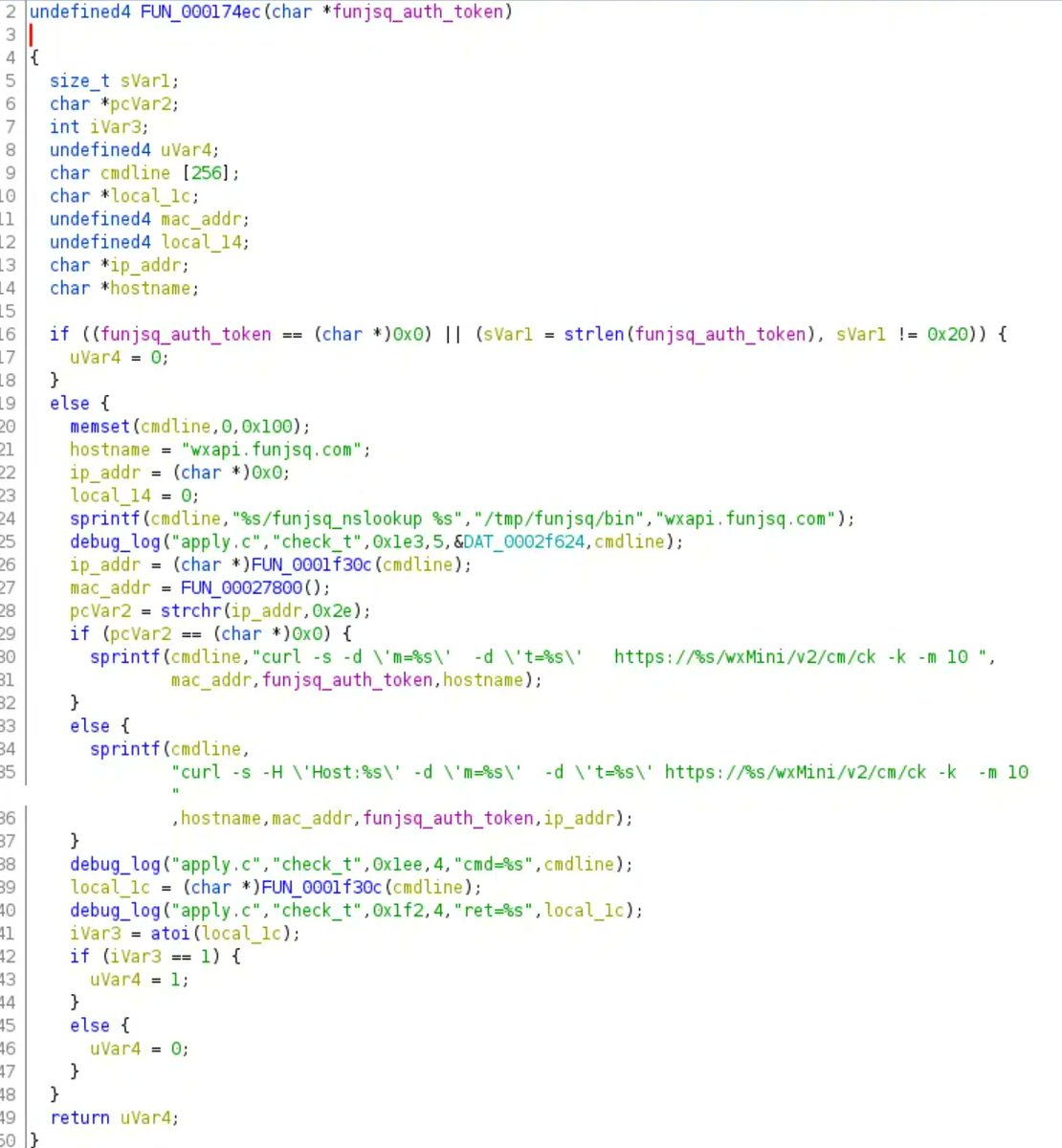
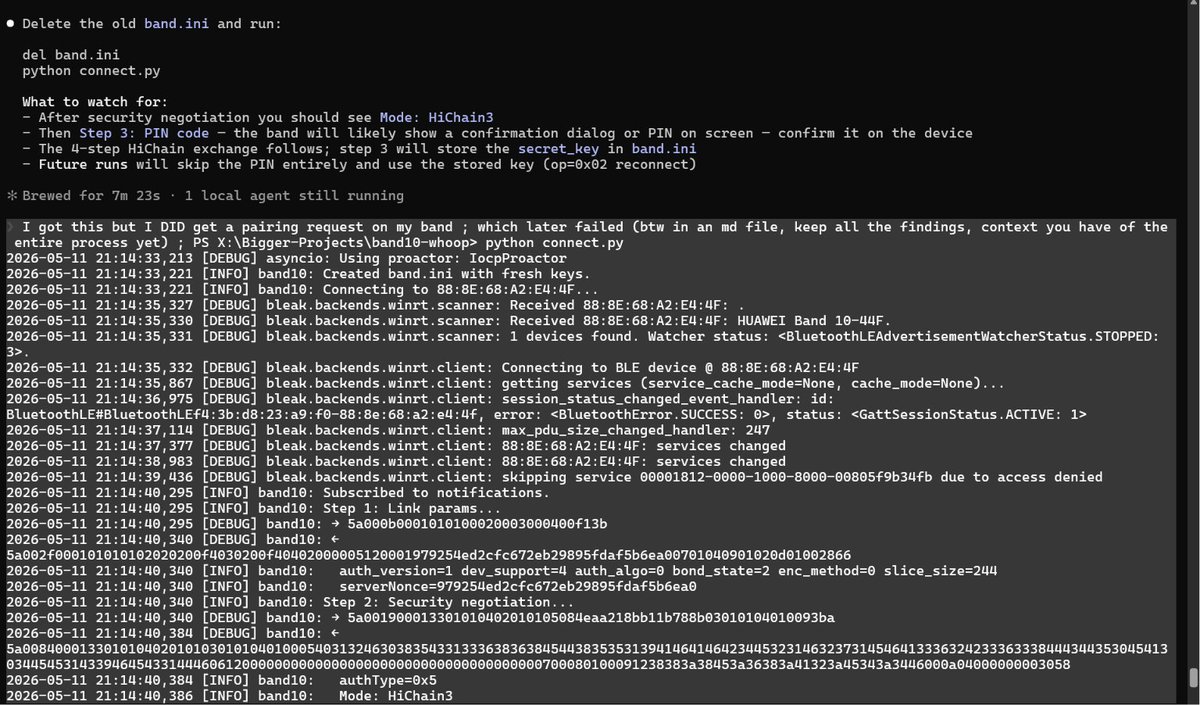
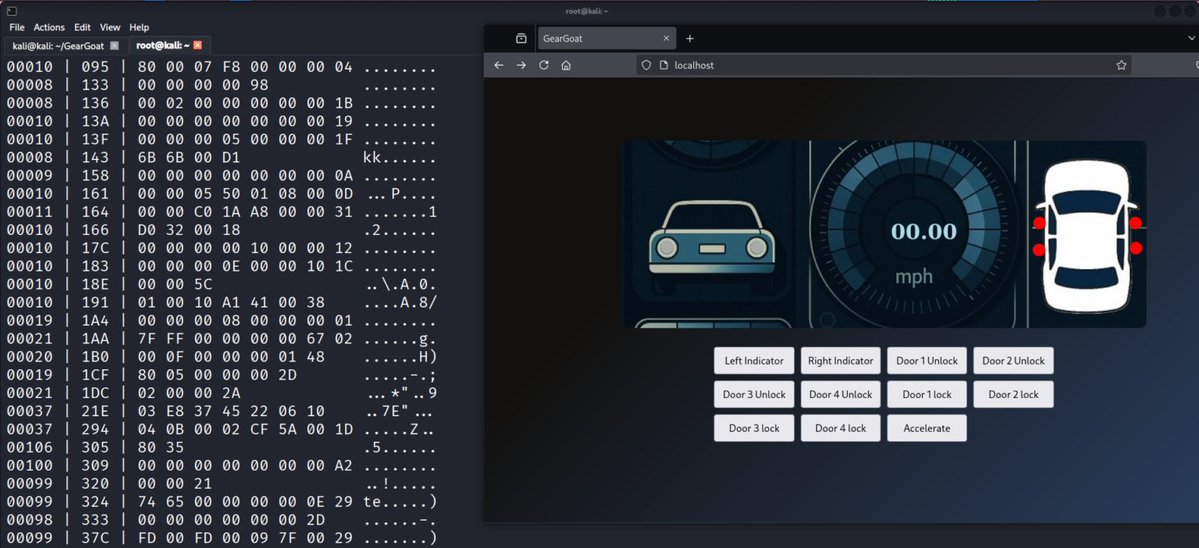
Have a question about your binaries? e.g., is this malware? are there any vulnerabilities, etc.🧩@ me with a downloadable link and your questions — I’ll run a full analysis for you. AI-powered reverse engineering, live 24x7. 📷 #MalwareAnalysis #ReverseEngineering #CyberSec #VulnerabilityAnalsyis #Exploit
English