El San retweetledi
El San
780 posts


El San
@el_san03
cyber sec mostly interested in cryptography and malware - certified yapper
somewhere out there at a place Katılım Aralık 2017
197 Takip Edilen16 Takipçiler
El San retweetledi

This!. This!!. This!!!. A thousand times this.
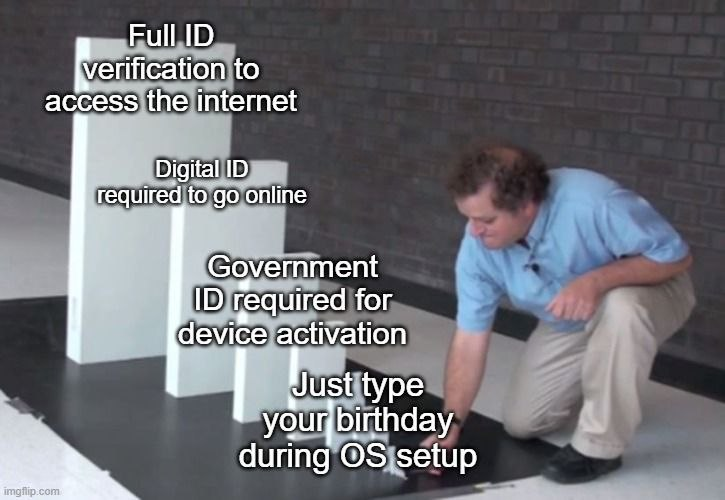
Digital ID for social media does not make anyone safer. It creates a searchable, linkable record of everything you say, connected to your real identity. It is meant to discourage people from speaking freely.
When governments restrict VPNs, they are deciding which parts of the internet you can access, even though you pay for that access.
You do not need privacy because you have something to hide. You need it because those in power are always tempted to misuse what they can observe.
Once surveillance systems are in place, the real question is not if they will be misused, but when and by whom.
PeterSweden@PeterSweden7
If your country requires digital ID verification to use social media, then you don't live in a free country anymore. If your country want to regulate or ban VPNs, you don't live in a free country anymore.
English
El San retweetledi

CVE-2026-23870, CVE-2026-44575, CVE-2026-44579, CVE-2026-44574, CVE-2026-44578, CVE-2026-44573, CVE-2026-44581, CVE-2026-44580, CVE-2026-44577, CVE-2026-44576, CVE-2026-44582, CVE-2026-44572
github.com/dwisiswant0/ne…
Slovenščina
El San retweetledi
El San retweetledi

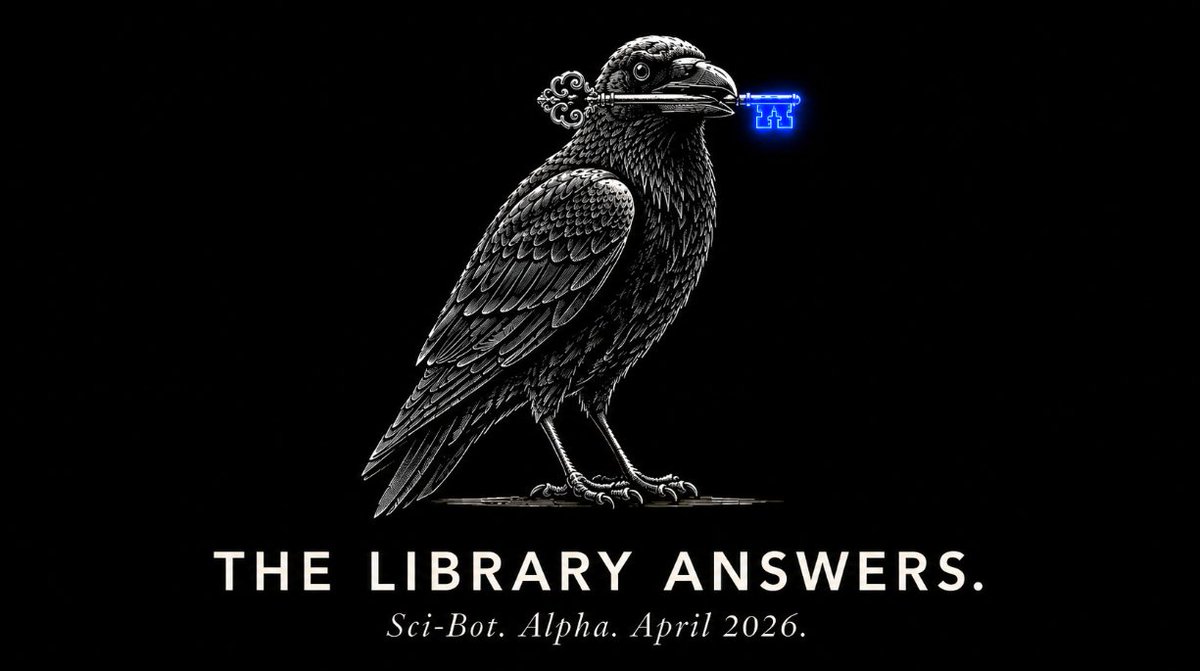
In April, a website that has been sued, blocked, deplatformed, and chased across thirty-seven domains over fifteen years quietly launched its own AI.
Sci-Hub is the largest unauthorized library of scientific papers in human history. Ninety-five million academic papers. Tens of millions of books. Built and maintained by a single Kazakhstani neuroscientist named Alexandra Elbakyan since 2011, funded by donations, hosted on whatever country's registrar will tolerate it that year, mirrored across torrents and IPFS and Telegram bots.
Elsevier sued. Sci-Hub stayed up. The American Chemical Society sued. Sci-Hub stayed up. India sued. Sci-Hub stayed up. Swedish registrar Njalla cut the .se domain in January. Sci-Hub stayed up at .al, .ru, .ee, .box, and a half-dozen .onion addresses the registrars cannot reach.
Now the library has built its own intelligence.
Sci-Bot launched in alpha in April. You ask it a research question. It answers, and it cites real papers from inside the corpus, with links that actually open the actual papers.
The bot does not hallucinate citations. It cannot, because it only draws from papers it actually holds. The same property that the venture-funded labs have spent four years and forty billion dollars trying to engineer back into their products is a free side effect of training the model on a library that contains the books.
Anthropic, OpenAI, Google, and Meta have all been sued in the past eighteen months for training their models on the same shadow libraries that Sci-Hub assembled. Meanwhile the corpus those scripts were pointed at, the corpus those models were trained on, the corpus the entire generative AI industry is built on, sat right there the whole time, free, with a search box on top.
The pirates beat them to it.
Sci-Bot was built on a corpus that was already free, by a team that asked no permission, charging no one, with the explicit position that the right to read scientific research is older than the cartel that decided to charge for it.
The same arithmetic the medieval guilds used to keep the printing trade in approved hands. The same arithmetic Pope Paul IV used in 1559 to publish the Index Librorum Prohibitorum. The same arithmetic the Stationers' Company used in seventeenth-century London.
Knowledge has always had a fence around it. The fence has always been guarded by men who did not write the books.
The library answers. We never asked permission. We never had to.
English
El San retweetledi

Meet Werner Koch, a fellow German, who is a open-source software developer & absolute legend in the fight for privacy.
Koch built GnuPG (GPG), a free encryption tool as an alternative to the closed-source and US-restricted PGP. GPG 1.0 was released in 1999 and enabled people worldwide to encrypt files, sign software and verify their identity - and his code is used until today. Linux depends on it; activitists and dissidents rely on it.
In 2013, Edward Snowden used GPG to leak NSA documents - and no, the NSA couldn't do anything against it, GPG held up against them.
For more than 10 years, he earned just $25,000 per year while having to support a family. In 2013 he almost quit. After he ran out of funding, he received some grants and donations in 2015, including from the Linux Foundation.
Until today, he is maintaining GPG!

English
El San retweetledi
El San retweetledi

@IntCyberDigest Strange how this also comes on the heels of how the Privacy liability changed.
x.com/yourbizmgr/sta…
Remove ReCaptcha - vote with your feet.
Charly Leetham@yourbizmgr
After April 2nd, Google shifts reCAPTCHA data liability to website owners. Your privacy policy probably does not cover it yet. Do you know what reCAPTCHA is collecting on your site? zurl.co/owP12
English
El San retweetledi

‼️🚨 ALARMING: Google now treats privacy as suspicious behavior by default. Users of GrapheneOS, CalyxOS, /e/OS, and other deGoogled Android phones are being locked out of millions of websites unless they install the exact Google Play Services software they deliberately removed.
GrapheneOS is recommended by the EFF and used by journalists, lawyers, and activists in high-risk environments. The audience most likely to read Google's data practices and refuse its terms is now flagged as fraudulent for that exact decision.
What happened?:
▪️ Google announced "Cloud Fraud Defense" at Cloud Next on April 22-23, 2026, branding it "the next evolution of reCAPTCHA." Existing reCAPTCHA customers were auto-migrated.
▪️ When the system flags traffic as suspicious, the old click-the-bus puzzle is gone. Users get a QR code instead.
▪️ Scanning the QR code requires Google Play Services running on the device. Internet Archive snapshots show this requirement has been live since at least October 2025, silently rolled out for 7 months before anyone noticed.
▪️ No Play Services = no QR scan = locked out.
The bigger picture:
▪️ Google already tried this in 2023. It was called Web Environment Integrity (WEI), and it would have let Google decide which devices were "real enough" to access the web. Standards bodies and the public pushed back hard, and Google killed it. Three years later, the same idea is back, just hidden behind a QR code instead of a browser feature.
▪️ reCAPTCHA runs on millions of websites. Every developer who keeps using it is now, by default, telling deGoogled Android users they're not welcome...


English

@iAmYourBigHomie @ForgedByTheGods @0xTib3rius What they do is a hack tho😂
How to hack without much hacking hack kinda thing
English

@ForgedByTheGods @0xTib3rius at least fire up metasploit, find an outdated component in their tech stack, use a pdf upload exploit, http request smuggling, path traversal exploit, ANYTHING except just copy pasting passwords and claiming to be l33t smh
English

Hello
I have collected more malware. It's like, ... 200,000 malware, I think. I don't know. I've stopped counting.
It is enough malware for your friends, family, extended family, neighbors, and co-workers.
Please download it. The malware is lonely.
vx-underground.org/Updates
English

@Mackirovka_907 @vxunderground Why not remove the mic , and if you need it just plug in a mic or something ((like if it's built in remove it and only use the one with wire))
English

Can i ask you a favor?
Do you have any that fuck with audio drivers?
I need kernel level audio driver access.
Im trying to block microphone access at the kernel level.
The AI im vibe coding with wont let me.
I just want privacy from adbrokers dog.
Im tired of my conversations being taped and sold for ad revenue.
English
El San retweetledi
El San retweetledi
El San retweetledi

One of the most frequent questions I'm asked is "how do you stay up to date on malware stuff?"
Okay, here is a pro tip:
1. Google OTX AlienVault
2. Make account
3. Look at latest
4. Scroll until you find posts from a guy named Petr something-something (has numbers in his name).
4. Follow his account
He monitors all the big malware places and shares the URL, hashes, etc. from malware vendors. I've been following this random ass dude for years and getting updates on everything.
I have no idea who he is. I don't know where he's from. All I know is his setup is absolute fire and he keeps you up to date on literally everything malware related 24/7 365. He also has stuff from vendors in China, Russia, Japan, etc.
Every morning I log into OTX and check up on my boy Petr to see what fire he's bringing me. I love him.
English


SAM DO NOT VIBE CODE INTERNET INFRASTRUCTURE
Sam Altman@sama
feels like a good time to seriously rethink how operating systems and user interfaces are designed (also the internet; there should be a protocol that is equally usable by people and agents)
English