Emily Stark
3.4K posts


Emily Stark
@estark37
Trustworthy 🔑 transport 🚆 for Chrome. HTTPS, certs, encryption, security UX, software eng & mgmt. @estark.bsky.social. Opinions are my own. she/her
San Francisco Bay Area Katılım Kasım 2010
888 Takip Edilen10.2K Takipçiler
Emily Stark retweetledi
Emily Stark retweetledi
A proposed CA/Browser Forum ballot would radically shorten the max validity period of #TLS certificates over the next few years github.com/cabforum/serve…
English

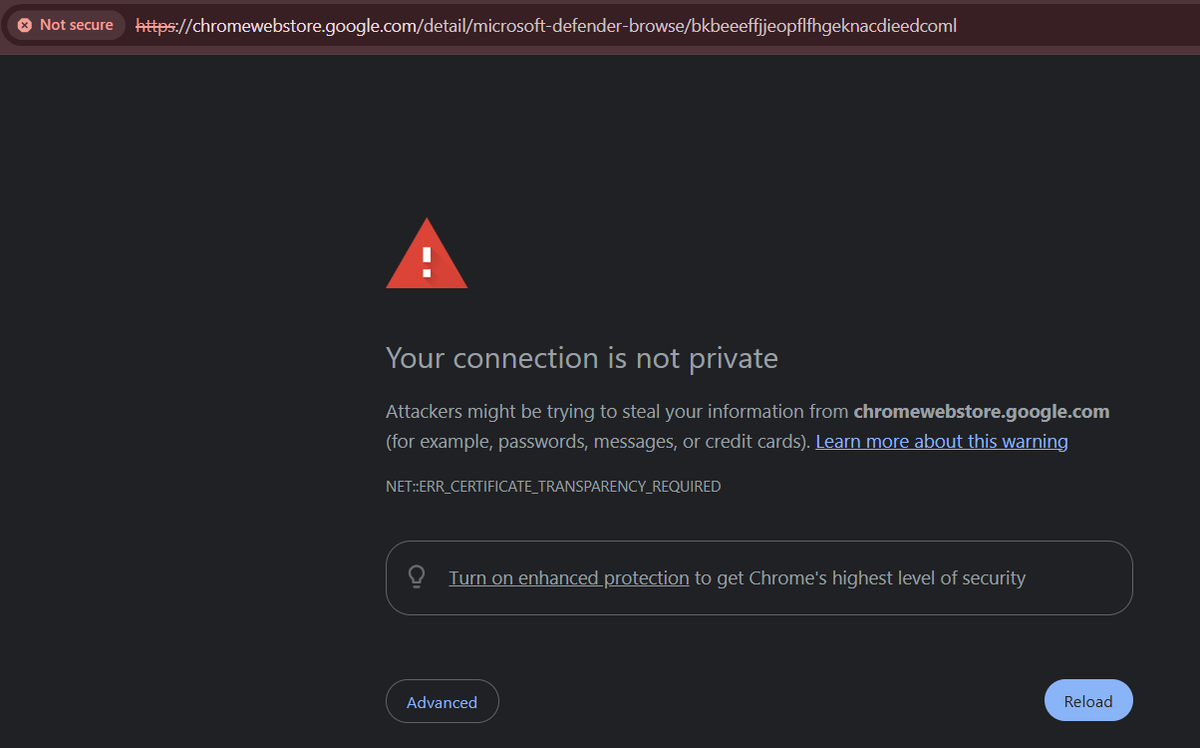
@musalbas @distractedm1nd @ekr____ @taoeffect This was how the initial deployment of CT worked, but is no longer true for Chrome. SCTs are audited probabilistically.
English

@distractedm1nd @ekr____ @taoeffect And the way Chrome has implemented SCT auditing means that all Chrome clients "see" the same tree head; in other words, a log can't target individual Chrome clients with a split-view.
English

@distractedm1nd @ekr____ @taoeffect I'm not going to dispute that CT has nuanced security guarantees (emilymstark.com/2022/08/23/cer…), but the tweet you quoted is pointing out that there are, in fact, deployed forms of gossip in the wild. Also doesn't seem fair to ignore that Chrome does do (probabilistic) SCT auditing.
English

@prdonahue @thedanigrant @GrantSlatton @ptrschmdtnlsn It's sometimes more trouble than it's worth for us to do non-deterministic behavior like this because it can be confusing/hard to debug. (user reports cert error, site operator can't reproduce)
English

@prdonahue @thedanigrant @GrantSlatton @ptrschmdtnlsn I don't think we (on Chrome at least) have considered this for upcoming expired certs, but I think Google has done it for some server-side cert changes.
English

@benadida The DRM angle is that it creates an ecosystem in which users are limited in the software and hardware they can use to create/edit content. You can strip off the metadata, sure, but then your content is no longer "legitimate". It's not literally DRM, but spiritually similar IMO.
English

@benadida ... contains much less fraught solutions if the goal is for skilled analysts (rather than the mass consumer user base) to be able to distinguish. Like even just having the metadata in the image but not displaying it to end users would be preferable IMO.
English
We need affirmative sourcing of images online. Some thoughts. We can do this in a privacy protecting way.
benlog.com/2024/09/27/aff…
English

@benadida ... resources should go into flagging mis/disinformation, and/or giving nuanced context around questionable content, rather than affirmative indicators.
English

@benadida I really try not to shoot things down without presenting an alternative, which I don't have. But I vaguely feel that technology is putting the cart way before the horse, solutions must be customized to the UI and user base of each social media platform, and the bulk of the...
English
Emily Stark retweetledi
It's a common misconception that we need to move from AES-128 to AES-256 to counter quantum attack. In this great talk @sejaques explains why, and shows a few new arguments why Grover's algorithm is even less practical than we already understood it to be. youtube.com/watch?v=eB4po9…

YouTube
English