Mr. FE
2.7K posts









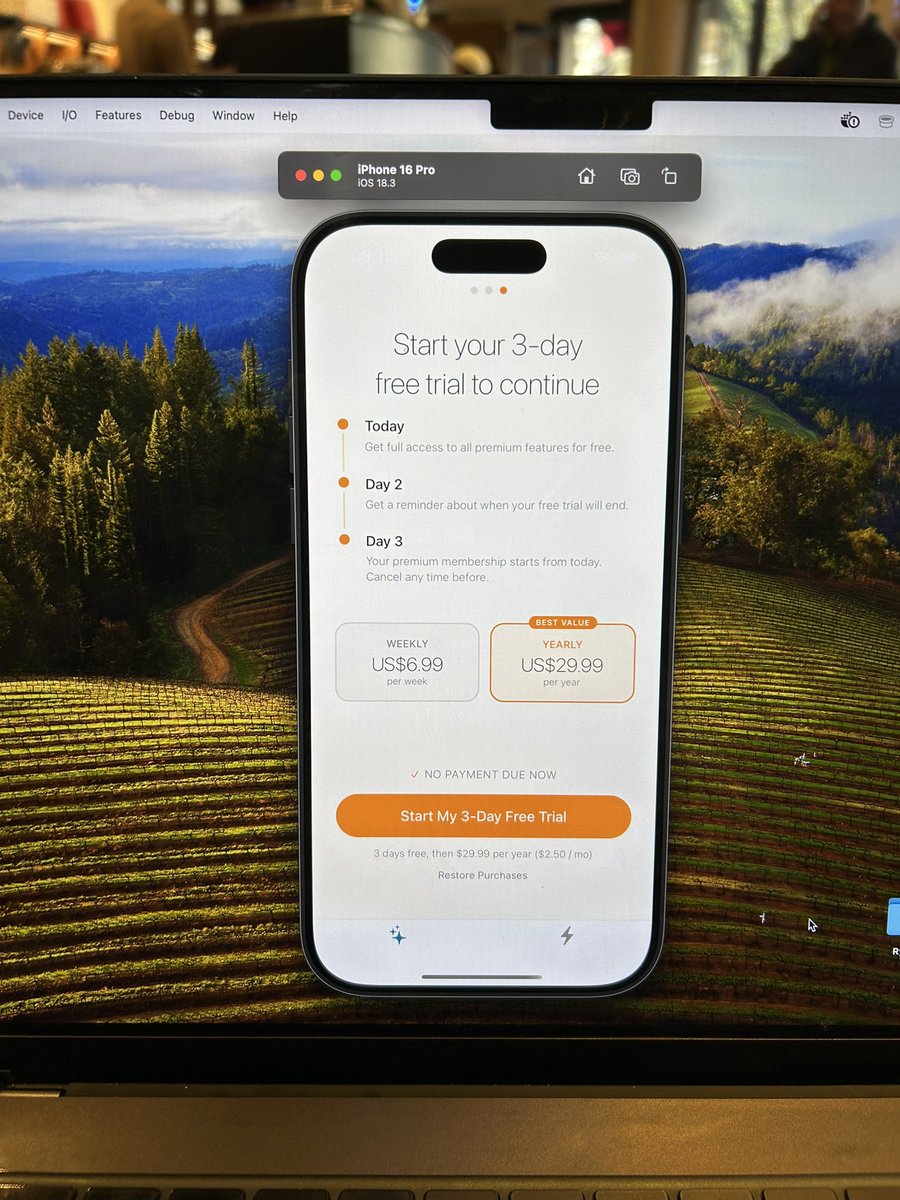
A Nigerian fintech just lost ₦20 million to a fake webhook. Attacker didn’t hack anything. They just POSTed this to the endpoint: { "event": "transfer.success", "amount": 500000, "status": "success" } Backend credited the user. Zero money moved. This is happening more in crypto payments too. What every backend dev must do in 2026: 1. Verify webhook signature + IP + timestamp (not just event name). 2. Never credit on webhook alone always confirm on-chain + NIBSS. 3. Add rate limiting and replay attack protection. 4. Reconcile every stablecoin inflow against blockchain truth. Crypto rails move fast. One lazy endpoint and you’re done. Save this like your production depends on it. Drop your worst webhook horror story 👇
















I challenged 3 strangers to make $1 with AI. They had: > 6 weeks > $100 budget > to build from scratch 1 burned out. 1 pivoted. 1 printed $$$. Full episode in REPLIES 👇


Everyone got excited when they saw Peter Obi at the airport today.