
Is the era of ugly AI sites over? @Lovable Aesthetics says YES. ‼️ I built this whole site with one prompt ‼️ Check the comments for the exact wording). This is the missing link vibecoding needed. Proud to be an ambassador. ❤️
Aleš
1.2K posts

@fxckdev_
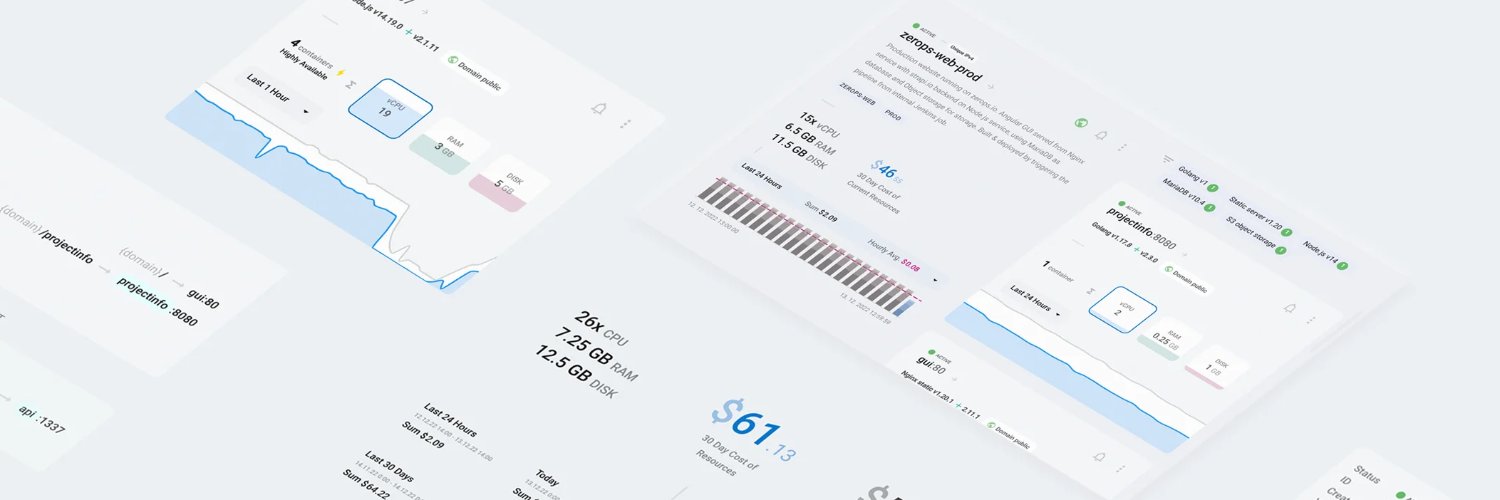
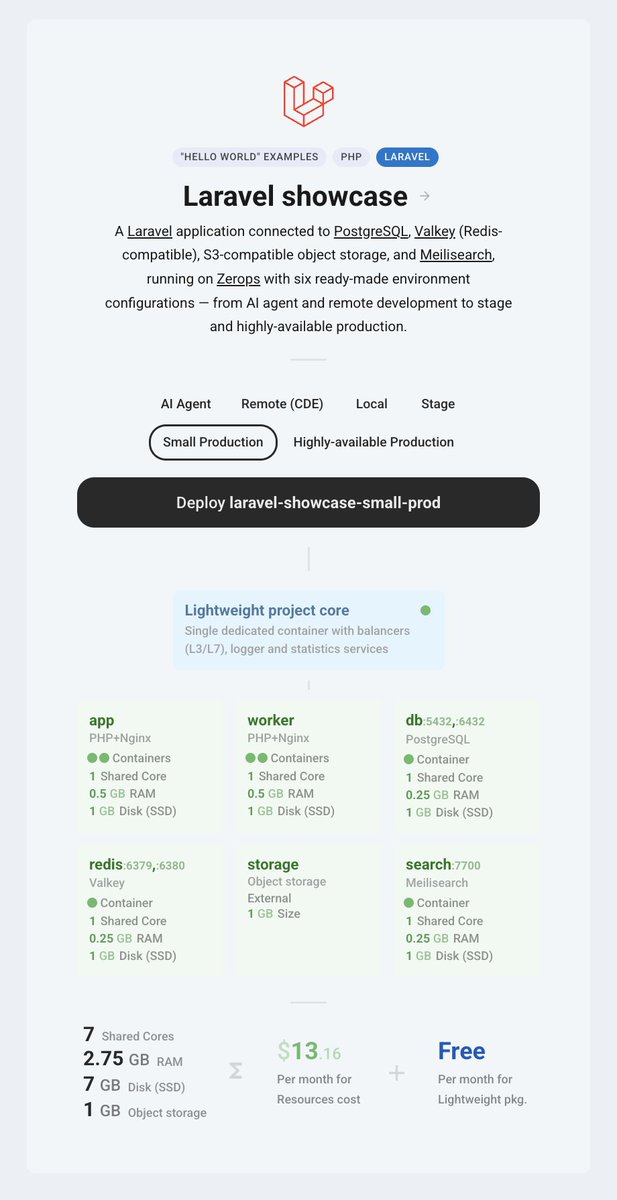
CEO / Co-founder @zeropsio - a developer-first PaaS. 15+ years of experience with development, UX and stuff. Angular enjoyer.

Is the era of ugly AI sites over? @Lovable Aesthetics says YES. ‼️ I built this whole site with one prompt ‼️ Check the comments for the exact wording). This is the missing link vibecoding needed. Proud to be an ambassador. ❤️











With news that the “Dirty Frag” Linux exploit embargo had been broken early — leading to all major Linux distros being unprotected from the exploit when it became public — many people are asking: “What is an embargo?” Along with, “How is it possible to have an embargo on an Open Source vulnerability?” Here’s the short-short version: An embargo is, in essence, an agreement to not disclose something publicly until a set time (or until conditions are met). Embargos are incredibly common among news outlets, and press relations teams. “Don’t publish the story until next Monday, after an announcement,” etc.. And they are a key part of how Open Source development handles exploit mitigation (for better or worse). The process is roughly like this: 1) Someone discovers an exploit. 2) Once sufficient information about the exploit is gathered, a core group of developers (working at a range of companies, including Red Hat, SUSE, and others) are then notified. 3) An agreement on an embargo timeline is reached. This is usually simple: X days (or X weeks) until the details of the exploit are published for the public to see. How long the embargo lasts is typically decided by how long it will take the relevant teams to fix the issue, test the fix, and publish the fix… while taking the seriousness of the exploit into consideration. The idea here is to keep details, on how to take advantage of the vulnerability, under wraps… until a fix is available. In other words: minimize the damage an exploit might cause. In the case of “Dirty Frag”, an embargo was decided upon… and that embargo was “broken” (meaning someone published the details) almost immediately.

💥 Introducing "Dirty Frag" A universal Linux LPE chaining two vulns in xfrm-ESP and RxRPC. A successor class to Dirty Pipe & Copy Fail. No race, no panic on failure, fully deterministic. ~9 years latent. Ubuntu / RHEL / Fedora / openSUSE / CentOS / AlmaLinux, and more. Even if you've applied the "Copy Fail" mitigation, your Linux is still vulnerable to "Dirty Frag". Apply the Dirty Frag mitigation. Details: dirtyfrag.io






The dedicated logger service inside every Zerops project is now using VictoriaLogs. - 100x more log retention - 3x faster queries - VictoriaLogs UI embedded into Zerops - Already rolled out to every existing project Full story below.