Holme
238 posts

Holme
@holme_sec
Love to learn https://t.co/RQQsvW1WcL https://t.co/3mOunfH5fM
Denmark Katılım Mayıs 2020
214 Takip Edilen1.1K Takipçiler

Secret Manager is live! 💥
And this isn’t just any Dojo chall - it was crafted by the community. Thanks @zerodaygym for bringing this one to life!
Somewhere in the code, a vuln is hiding. The question is: can you turn it into RCE?
🚩 Capture the flag: dojo-yeswehack.com/challenge-of-t…

English

Hey hackers! We're running a beta for Hai for Hackers, our AI security agent. If you're interested, please reply with your HackerOne username (we will probably limit to ~100 hackers for now). After it's been enabled, you can start using it by clicking the Hai button in the top right corner of the app. It’s free to use (with a limited daily budget for now). It is like any other AI you’ve interacted with, with the added benefit that it has access to a whole bunch of HackerOne data, like reports and programs. We’re shipping improvements to Hai almost every day. Here are some neat use cases:
- “take all the learnings from STÖK, jhaddix, and nahamsec's recon strategy and build one for me!”
- “write a python script for a typical recon process”
- “i need an XSS payload that doesn’t use single or double quotes”
- “my XXE payload doesn't call back to my server, what could go wrong?”
- “write a response for report #133337”
The beta also comes with Hai Plays for you, which allows you to build your own security agents in HackerOne. You can create them at hackerone.com/settings/hai_p…. Some of the cool use cases we’ve seen so far are:
- write reports with minimal input from you (efficiency++!)
- convert reports into blogposts with a single prompt
- AI mentor to give feedback about your communication and increase the likelihood of a reward
In the background we’ve been working on agentic behavior, which we expect will soon come to Hai for Hackers as well. These AI agents can act like your hacking buddy and hack alongside you. We’ll keep you in the loop on our progress.

English

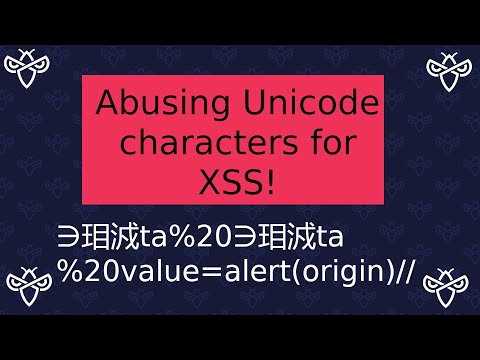
I was pinged by @GoatSniff who referred me to another past CTF example from @intigriti where there seemed to be unicode truncation/overflows -
youtu.be/aUsAHb0E7Cg?si…
YouTube
Gareth Heyes \u2028@garethheyes
Discover blocklist bypasses via unicode overflows using the latest updates to ActiveScan++, Hackvertor & Shazzer! Thanks to @ryancbarnett and @thecyberneh for sharing this technique. Writeup 👇
English

Today marks the start of the first live-hack event of the year for @Hacker0x01 : H1-305!
I'm going to sunny Miami to hack on @CapitalOne and hang out with some of the smartest hackers around.
It will hopefully be an epic adventure!
#h1305 #TogetherWeHitHarder

English
Holme retweetledi

Did you see this cool web challenge by @holme_sec, featured in the #1337UPLIVE CTF? 😎
Find out how to solve it, in our latest video from @_CryptoCat 😺
youtu.be/JetPydd3ud4

YouTube
English

Soon leaving for my first trip to Tokyo for the live hacking event with @Hacker0x01 and @PayPal .
Everyone at H1: Thanks for making this happen!
#H1803
HackerOne@Hacker0x01
Hacking for #H1803 kicks off today! This time we’re partnering with @PayPal, a leader in the space who is dedicated to protecting their users and customers 24/7. Join us in cheering on these amazing hackers as they #hackforgood! 🎉
English

Abusing Yelps Cookie bridge to turn self XSS into plain XSS and leak HttpOnly cookies of the victim. I'm a little dissapointed with their CVSS scoring here. Another case of setting PR:L on a self signup service...
publiclyDisclosed@disclosedh1
Yelp disclosed a bug submitted by @lil_endian: hackerone.com/reports/2089042 #hackerone #bugbounty
English
@marcolivermunz @intigriti Yay, congratulations! It looks really great🔥
English

🎉 Achieved a thrilling milestone - just received a personalized portrait from @intigriti! Grateful for the chance to hack on such an awesome platform while being rewarded with unique creations. 🚀 Thank you, for turning me into art 🤩 #hackwithintigriti

English

Here's a write-up on a Browser-Powered Desync bug that I discovered in the Azure CDN service known as Front Door. The entire concept is built upon the excellent research by @albinowax. Initially identified within the @intigriti program.
blog.jeti.pw/posts/knocking…
#bugbounty
English
@StanFaas @intigriti Thanks! Was really nice seeing you again as well:)
English
I had a lot of fun at the @intigriti #1337UP0623 LHE. Was really nice seeing everyone (again)! Also very happy I got the award for the best PoC


English
@MattiBijnens @honoki @arneswinnen @intigriti Huge congratulations @MattiBijnens🎉 Very well deserved👏 Was nice seeing you again!
English

Just got back from an amazing live hacking event and brought home 4 incredible trophies and a 40k bonus! Massive shoutout to my exceptional team @honoki and @arneswinnen for their skills and teamwork. Special thanks to @intigriti for organizing this unforgettable experience!

English
@leo__rac @intigriti Thanks Leo, was nice getting to know you better as well!
English
@intigriti Thanks a lot! And thanks for a wonderful event! I think I found a nice spot for it😏

English

@holme_sec Well deserved award Holme! Hope you can give it a nice place back in Denmark!
English
@marcolivermunz @intigriti Thanks! And thanks for teaming up with me, was a pleasure as always;)
English

@holme_sec @intigriti You did great 👏👏! Well deserved 🎉
English