InfoSecDragon retweetledi

This is one of my fave current strats by malware delivery systems:
They are not targeting end victims first. They’re targeting the trust layer.
Attackers compromise legitimate advertisers or small ad agencies. There are thousands of these entities, typically small teams (1–10 people) with weak IAM, poor MFA enforcement, and minimal audit visibility.
Once inside, they gain control of accounts connected to Google Ads or other trusted advertising pipelines. That access is the asset.
They then monetize it in two ways:
Direct use: run malicious ad campaigns (malware, phishing, fake installers) under a legitimate, reputation-backed account.
Access brokering: resell campaign access to other operators who want distribution without building trust themselves.
Persistence is maintained deliberately:
Malicious ads are embedded within existing campaigns to avoid obvious anomalies.
Additional users are provisioned to maintain redundancy and prevent lockout.
UI-layer manipulation is used to reduce visibility (buried campaigns, naming collisions, low-visibility configurations).
Dwell time can extend for months because detection relies on owner-side observation, not platform enforcement.
In many cases, attackers inject their own funding into the account. This stabilizes spend patterns and avoids triggering billing or budget anomalies that would alert the legitimate owner. The objective is to preserve the integrity of the trust relationship for as long as possible.
The entire model hinges on one factor: once an account is trusted by the ad platform, that trust can be operationalized and resold.
☯️
solst/ICE of Astarte@IceSolst
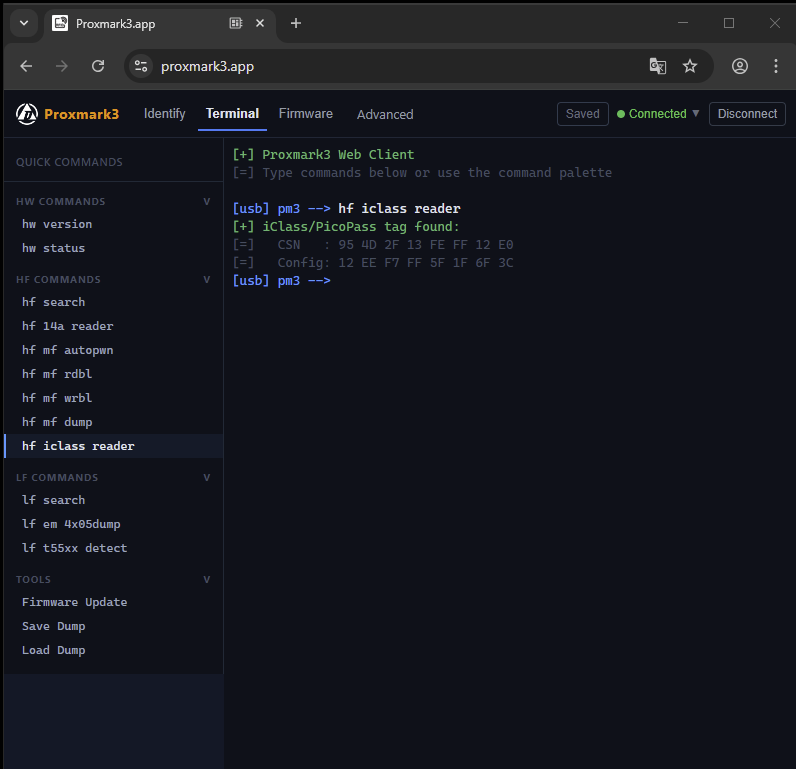
You can just advertise your malware on Google search results. It’s that easy.
English