Init1Security
181 posts
Init1Security
@init1security
Elevating security with expert offensive strategies

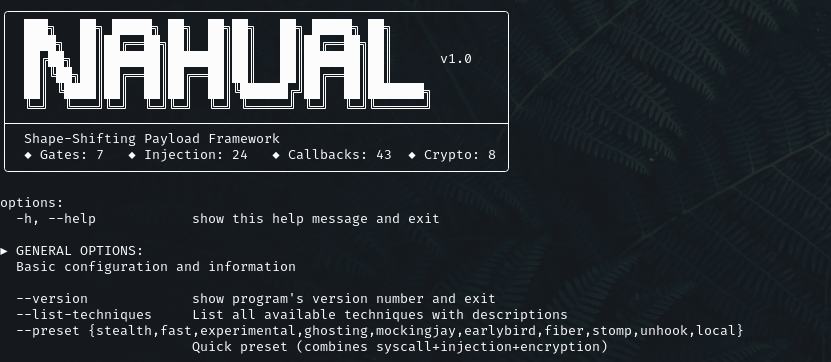
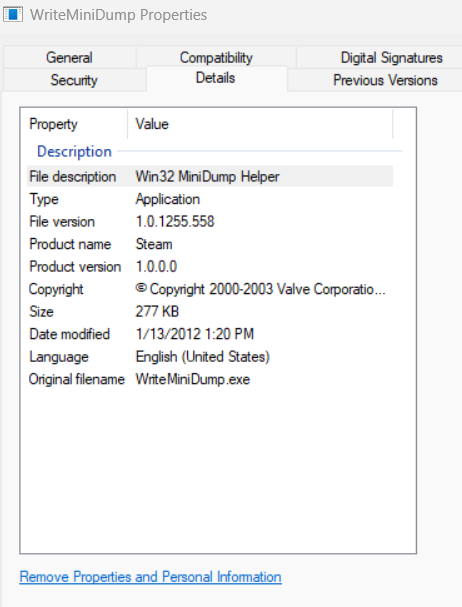
I am back in beautiful Mexico, and with some down time here and there (when my son sleeps). I get the chance to work on a cool project that reminded me of Veil-Evasion a framework that was the big on payload generation and evasion our internal tooling for @init1security and to give some reference to Mexico I named it Nahual. Utilizing different "Gates" techniques, syscalls methods, encryption and evasion methods they can be activated with a simple flag: '--key-username "demo" --encryption aes, etc, etc.' it's a really big project that I've been wanting to tackle to solve and automate my evasion issues, has been with great success (sometimes), I can use full meterpreter (highly signatured) shells and metasploit as my C2. #redteam



🚨 Speaker Announcement – #BSidesPrague2026 🎤 Marco Balzarin Abusing the Ordinary: New COM-Based Windows Attack Vectors Explore Windows COM from an offensive angle—new hunting methods and undocumented techniques for stealthy code execution via legitimate components. #Bsides