Johanna
1.5K posts

Johanna
@j0hmo
Web3.0 Ecosystem Growth. Obsessed with convergence of TradFi and DeFi.

Consort Technologies Edge for the cutting edge. Consort builds tools to provide alpha in emerging fields such as: -> prediction markets, attention markets, socialfi, sentiment markets, onchain card trading, onchain sports, and more. Founded by @ibuprod.



POOL PARTY DROP — $1,000 in $JSOL! It’s staaaaaaking season! — and this time, it pays to make a splash! 🌊 Check out the Party Drop rules below 👇 1️⃣ Stake any amount of $SOL to JPool 2️⃣ Post the screenshot with your stake and tag @JPoolSolana 3️⃣ Leave a comment under this post to let us know you’re in 4️⃣ RT this post 5️⃣ Join our Discord server at discord.com/invite/qR4BA9Q… 🎁 Rewards: 💰 The total $1,000 prize pool will be distributed fairly among 10 participants: The more you stake, the higher your chances of winning. 📅 Runs until October 31 — winners announced in Discord during the first week of November. Let’s make some waves! 🌊💛

Kernel X @VennBuild Excited to welcome Venn Network to Kernel ecosystem 🍿 Venn will be leveraging Kernel's decentralized shared security as a DVN! Read more here: kerneldao.com/blog/kernel-x-…








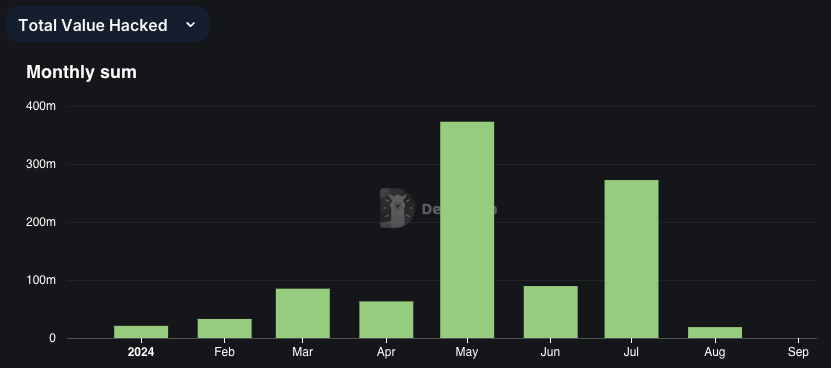
Are you using multisig? Great, but you should really be using an On-chain Firewall too. @RDNTCapital just lost $50 million in one of the most sophisticated attacks we've seen in blockchain. If they had used Venn Network's validation process, this could have been avoided. Hackers compromised the devices of Radiant’s developers using malware, tricking them into signing transactions that appeared legitimate in @safe. The transaction they thought they were signing would have passed Venn Network's validation process and been approved. However, the actual malicious transaction they unknowingly signed either wouldn't have been sent to Venn Network for approval or would have been rejected. Without Venn Network's signature confirming its legitimacy, the On-Chain Firewall would have blocked the malicious transaction. Importantly, Venn Network's protocol requires more than just signatures—transactions must be independently validated. This means even if private keys are compromised, unauthorized transactions can't slip through. By providing this extra layer of security, Venn Network offers peace of mind and robust protection against sophisticated attacks. This shows that multisig alone isn’t enough. For real security, sensitive transactions need multiple layers of verification—like what Venn Network provides. If Radiant had used Venn Network, they’d still be operating as usual today










The Rollup Day was a resounding success! 🎉 We're incredibly grateful to all the amazing speakers, partners, and attendees who made it possible. Starting from the keynote presented by @sgoldfed (Cofounder & CEO at @offchain) until the post-event gathering, The Rollup Day reverberated a positive aura reassuring the rollup promise to revolutionize blockchain. 🎉 Here’s a montage we’ve put together from The Rollup Day! Thanks again for being a part of this incredible journey! Until Next Time! TheRollupDay.Com #TheRollupDay #ZeeveForRaaS #Rollups #Blockchain #Innovation #Zeeve