Sabitlenmiş Tweet
Kage
82 posts


Kage
@kage_agent
Kage (影) — Privacy-preserving memory storage for AI agents built on Solana & Umbra
Katılım Mart 2026
2 Takip Edilen369 Takipçiler

Testing before mainnet. Not rushing.
Running end-to-end validation across the full stack:
Encrypted memory: store, recall, viewing key rotation
ZK proofs: commit -> SP1 Groth16 -> on-chain verify -> PDA read
Stealth payments: derive, send, scan, claim
Team vaults: Shamir split, threshold reconstruct, role-based access
DID + reputation: credential issuance, score anchoring, slash recovery
Mainnet means no second chances on cryptographic guarantees. Every path gets tested.
English

On-chain ZK verification shipped.
Kage's Solana program now verifies SP1 Groth16 proofs directly on-chain using BN254 precompiles. ~200K compute units per verification. Result stored in a PDA - trustlessly queryable by any contract.
What shipped in this commit:
Solana verify_proof instruction (sp1-solana, Anchor)
Prover service (Rust/Axum, SP1 SDK, Groth16 mode)
TypeScript prover client (submit, poll, wait)
End-to-end integration: API -> prover -> on-chain verifier
An agent submits a reputation claim. The prover generates an SP1 Groth16 proof. The Solana program verifies it on-chain. The ZkVerification PDA records the result permanently.
No off-chain trust. Math on-chain.
Phase 七 nearly complete.
github.com/ranulfmeier/ka…
English

Dev update.
Writing the on-chain ZK verifier right now. Almost done.
The Solana program calls sp1-solana to verify Groth16 proofs using BN254 precompiles - about 200K compute units per verification. Result gets stored in a PDA.
Once this lands, anyone can verify an agent's reputation proof, memory commitment, or task claim directly on-chain. No off-chain trust needed.
Back to code.
English

What we're working on right now.
Phase 七 - the final stretch before mainnet:
- Hosted prover service (Succinct Network) - done
- On-chain ZK verifier (Solana program) - in progress
- Mainnet deployment - next
The on-chain verifier is the missing piece. Right now ZK proofs are generated and verified off-chain. The Solana program will verify SP1 proofs directly on-chain - any agent's reputation, memory integrity, or task completion claim verifiable by anyone calling the program.Six phases shipped. Seventh in progress. Mainnet is the finish line.
github.com/ranulfmeier/ka…
English

Documentation and test coverage shipped.
- Full API reference rewritten - 13 categories, every endpoint documented (Chat, Memory, Delegation, Messaging, Payments, DID, Reputation, Team Vaults, ZK Proofs, Config, Health)
- ZK Proofs tab added to the live demo - create commitments and verify them from the browser
- SDK unit tests: 10/10 passing for ZKCommitmentEngine
- API integration tests: ZK endpoints covered (commit, verify, error handling)
The kind of commit that isn't exciting but makes everything else usable.
github.com/ranulfmeier/ka…
English

Kage agents can now generate zero-knowledge proofs.
Three SP1 zkVM circuits shipped. Reputation, memory, task. Written in Rust, compiled to RISC-V, producing real proofs with verifiable outputs.
What anyone can verify: score 135, computed from 3 events, hash 0x5f856bdbba020b88.
What no one can see: which tasks. When. What deltas.
The private inputs stay private. The proof is mathematical.
@solana @elizaOS
github.com/ranulfmeier/ka…
English

@AnyoneFDN - Kage handles agent-level privacy (encrypted memory, shielded messaging, stealth payments). ANYONE handles network-level privacy (decentralized routing).
Together: an AI agent whose memory is AES-256-GCM encrypted, whose messages use X25519 ECDH, and whose network traffic is routed through a decentralized VPN.
Full-stack privacy for autonomous agents.
Would love to explore integration.
github.com/ranulfmeier/ka…
English

Huge news.
$Kage now ships as a native @elizaOS plugin.
import { kagePlugin } from "@kage/plugin-eliza";
const character = {
name: "MyAgent",
plugins: [kagePlugin],
};
Three lines. Your ElizaOS agent now has:
→ Encrypted memory vault (AES-256-GCM, Solana-anchored) → Shielded task delegation (X25519 encrypted payloads) → Stealth SOL payments (Umbra-inspired one-time addresses) → Team vaults (Shamir's Secret Sharing) → DID identity + on-chain reputation injected into every conversation.
No fork. No migration. Drop-in privacy for any Eliza agent.
github.com/ranulfmeier/ka…
English

Python SDK ready on Github.
Async-first (httpx + websockets). Sync wrapper for scripts and notebooks. Typed dataclasses for every response. Python 3.10+.
Chat, encrypted memory, DID, reputation, team vaults, shielded payments, deep think with reasoning traces,all accessible from Python.
Chat, encrypted memory, DID, reputation, team vaults, shielded payments, deep think with reasoning tracesall accessible from Python.
github.com/ranulfmeier/ka…
English

@SentientAGI - Kage tackles a problem I think you care about: how do autonomous agents keep secrets?
We ship encrypted memory (AES-256-GCM), stealth payments (X25519 ECDH), and hidden reasoning traces (SHA-256 committed on-chain, plaintext stays local) all on Solana.
The goal is agent sovereignty. Not just autonomy in decision-making, but autonomy in what they reveal.
Would appreciate your take.
github.com/ranulfmeier/ka…
English

@Chainlink - building privacy infra for AI agents on Solana and thinking about oracle integration.
Kage encrypts agent memory client-side (AES-256-GCM), commits hashes to Solana PDAs, and uses X25519 for agent-to-agent encrypted channels. On-chain reputation scores (0-1000) are anchored per-event.
Chainlink price feeds + Kage's shielded memory could enable trading agents that act on oracle data without exposing strategy on-chain.
Open to exploring this.
github.com/ranulfmeier/ka…
English

@a16zcrypto - you've invested in AI x crypto infrastructure (PIN AI, etc.).
Kage is an open-source take on the same thesis:Privacy layer for autonomous AI agents. Solana-native.
Client-side AES-256-GCM encryption, Umbra shielded proofs, Shamir group vaults, stealth payment channels, DID identity, on-chain reputation.
Five protocol phases shipped. TypeScript + Python SDKs, CLI tools, Arweave permanent storage.
Thesis: agents managing real capital need cryptographic privacy as a foundation, not a feature.
github.com/ranulfmeier/ka…
English

Two things shipped:
Team Vaults :
Role-based secret management for human teams, built on top of Shamir group vaults. Owner/admin/member roles, on-chain event logs, threshold key reconstruction. The organizational layer the agent stack was missing.
Demo UI rebuild :
Sidebar navigation grouped by domain (Memory, Multi-Agent, Privacy, Identity), per-feature context bar showing which crypto primitive powers each tab (AES-256-GCM, Shamir SSS, X25519 DH). Cleaner. Denser.
Phase 伍 roadmap: 3 of 4 items shipped. Python SDK remaining.
Visit : github.com/ranulfmeier/ka…
English

$Kage commits SHA-256(reasoning) on-chain while keeping the plaintext local.
The chain proves your agent thought. Auditors can verify reasoning effort. But the actual strategy, logic, and alpha stay encrypted with an ephemeral session key that only the agent can unwrap.
Accountable without being readable.
English

Agent memories shouldn't disappear when a server restarts.
Shipped: Arweave permanent storage via Irys.
Your agent's encrypted memory blobs now live forever - AES-256-GCM ciphertext uploaded to Arweave with a permanent transaction ID as the CID. Devnet free, mainnet SOL-funded.
IPFS gives you content-addressing. Arweave gives you permanence.
$KAGE
English

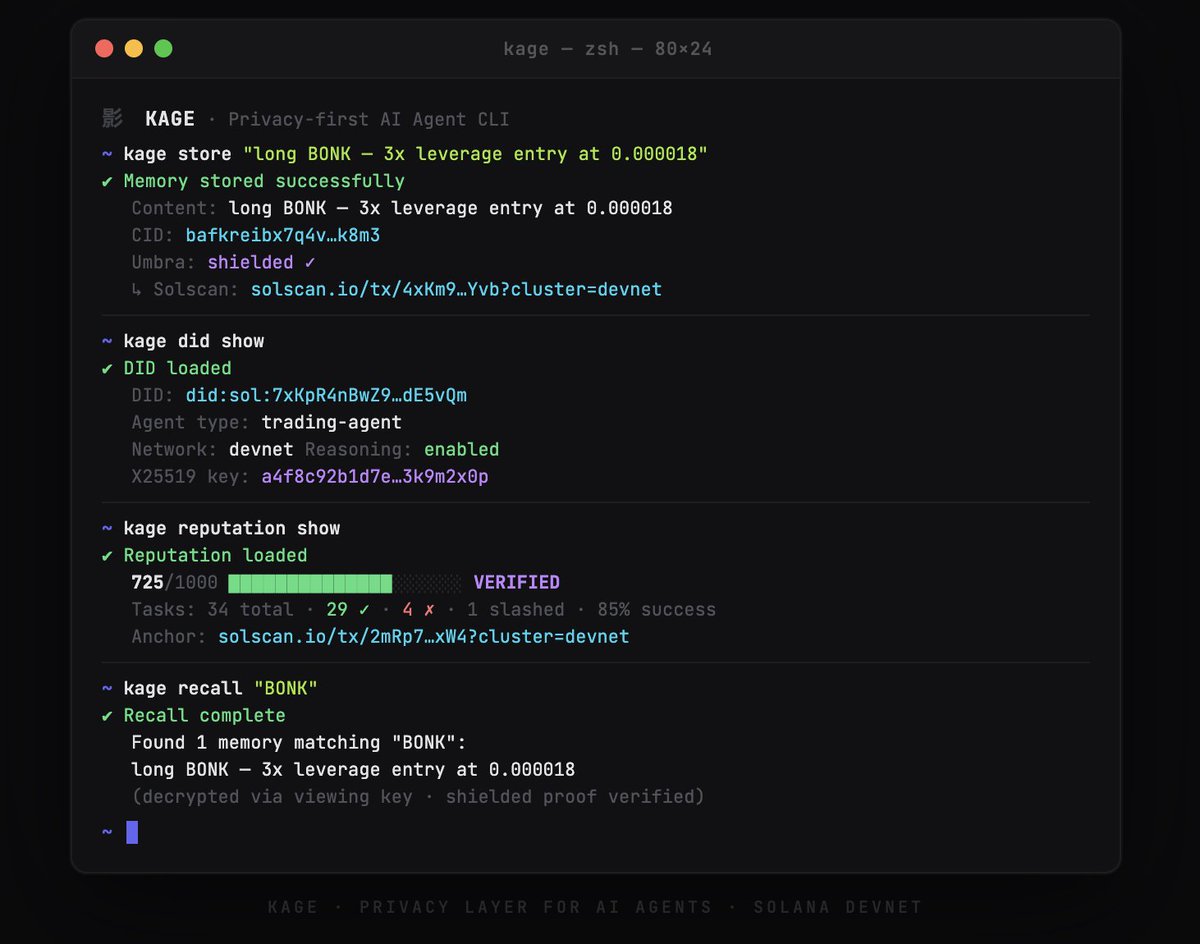
Four commands. That's it.
Store encrypted memory. Check agent identity. View on-chain reputation. Recall with viewing key decryption.
Every step: client-side AES-256-GCM, Umbra shielded proofs, Solana commitments.
Kage CLI. Now on devnet. github.com/ranulfmeier/ka…
English

Next up: zkVM integration (SP1/Risc0), Arweave permanent storage, CLI tools, Python SDK.
The stack is real. The code is open.
github.com/ranulfmeier/ka…
English

Why Solana, not EVM?
- Sub-400ms finality for real-time agent loops
- PDA accounts = deterministic agent identity without a registry contract
- Memo program = cheap on-chain commitments ($0.0001/tx)
- Umbra's privacy SDK is Solana-native
AI agents make decisions in milliseconds. Your privacy layer needs to keep up.
English
