zeroledger@zeroledgerxyz
After months of building, testing, and iterating, ZeroLedger is now ready for a live environment.
ZeroLedger began in October 2025, during a market downturn when momentum across the ecosystem had slowed. Instead of waiting, we focused on building, refining, and stress-testing the system across multiple public testnets.
Over time, the protocol evolved through continuous iteration, shaped by real user interactions and community feedback, strengthening its core mechanics and reliability.
ZeroLedger was also recognized in Base Batches 002, validating both the idea and its execution.
Just as important as the product was the community behind it.
Our community believed in the vision early, tested with us, gave feedback, and stayed consistent even when nothing was finished.
We deeply value that belief. It shaped how we built this system more than anything else.
Today marks the transition from testing to reality.
Mainnet is now live, with intentional limitations designed to ensure stability, performance, and a controlled rollout:
• Maximum Total Value Locked (TVL) is currently capped at $5,000.
• Maximum monthly active users are limited to 500 participants.
These limits are not constraints, but deliberate safeguards. They allow us to monitor the system closely, gather real-world data, and continue improving the protocol without compromising user experience.
ZeroLedger is designed to prioritize correctness, privacy, and reliability over rapid expansion. This approach ensures that every interaction on mainnet contributes to strengthening the system.
The ZeroLedger dApp is now accessible:
app.zeroledger.wtf
Airdrop Claim
The ZeroLedger airdrop is now claimable for eligible participants.
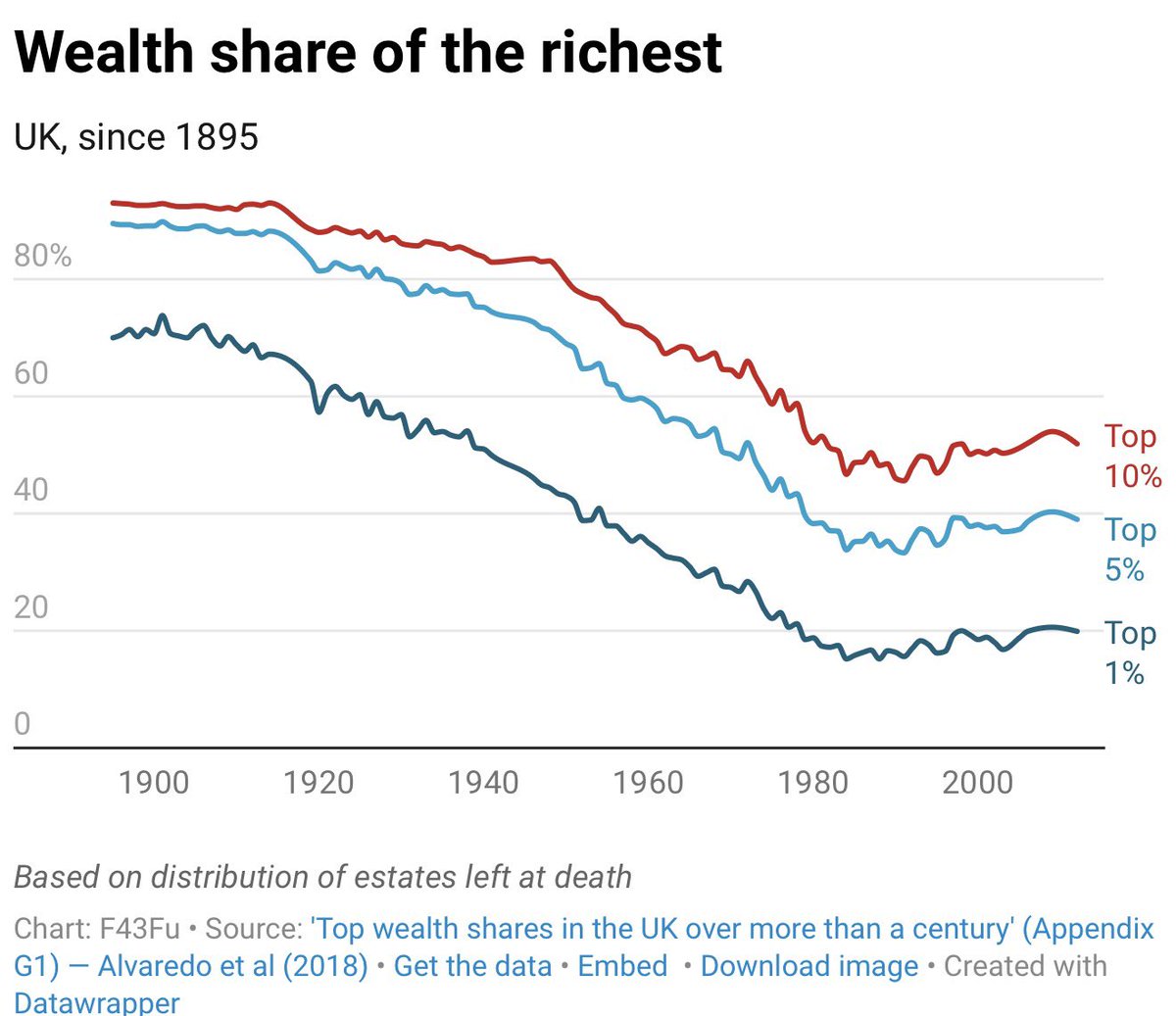
• The claim is available to all supported regions, with the exception of the United Kingdom.
Participants who engaged during the testnet phases can now access their allocations and become part of the live network from day one.
What This Means
Mainnet is not the final stage. It is the beginning of a new phase where real usage, real constraints, and real feedback will shape the future of ZeroLedger.
Every deposit, every transaction, and every interaction from this point forward contributes to the evolution of the protocol.
This launch represents more than a milestone. It reflects a commitment to building deliberately, shipping consistently, and prioritizing long-term reliability over short-term hype.
ZeroLedger is live.
And this is just the start.