Sabitlenmiş Tweet
The Imo Prince
3.2K posts


The Imo Prince
@liveking_1
Game| Design| Tokenized World
Katılım Şubat 2017
397 Takip Edilen248 Takipçiler

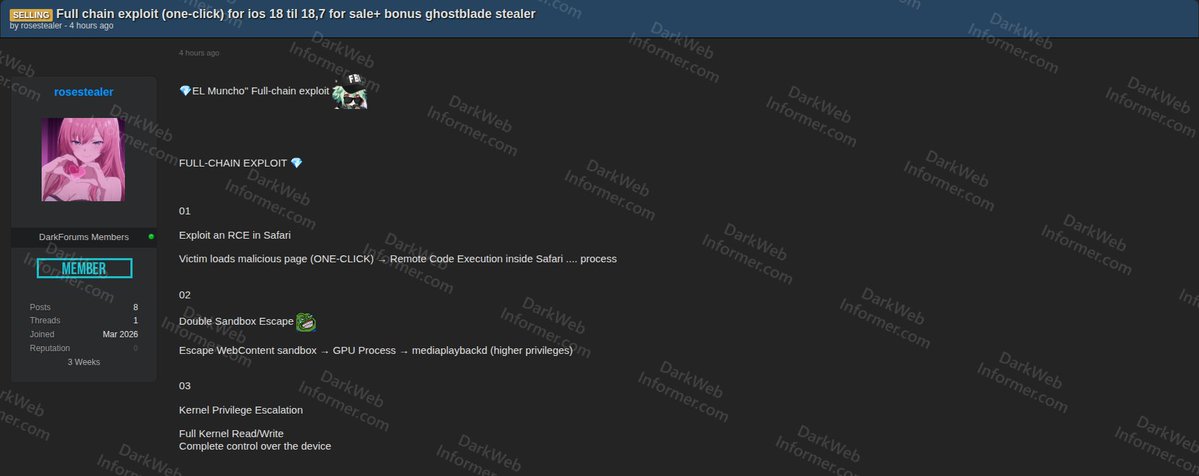
‼️A full-chain one-click exploit for iOS 18 through 18.7, bundled with a bonus stealer called "GHOSTBLADE," is allegedly being sold on a popular cybercrime forum.
‣ Threat Actor: rosestealer
‣ Category: Exploit / Malware
‣ Name: "EL Muncho" Full-Chain Exploit + GHOSTBLADE Stealer
‣ Target: iOS 18 to 18.7
‣ Price: $50,000 (negotiable)
Full-chain exploit stages:
01 - RCE in Safari:
Victim loads a malicious page (one-click) resulting in Remote Code Execution inside the Safari process.
02 - Double Sandbox Escape:
Escape WebContent sandbox to GPU Process to mediaplaybackd (higher privileges).
03 - Kernel Privilege Escalation:
Full kernel read/write, complete control over the device.
04 - Post-Exploitation:
Runs the GHOSTBLADE Stealer, injecting payload into a high-privilege process. All data exfiltrated back to C2.
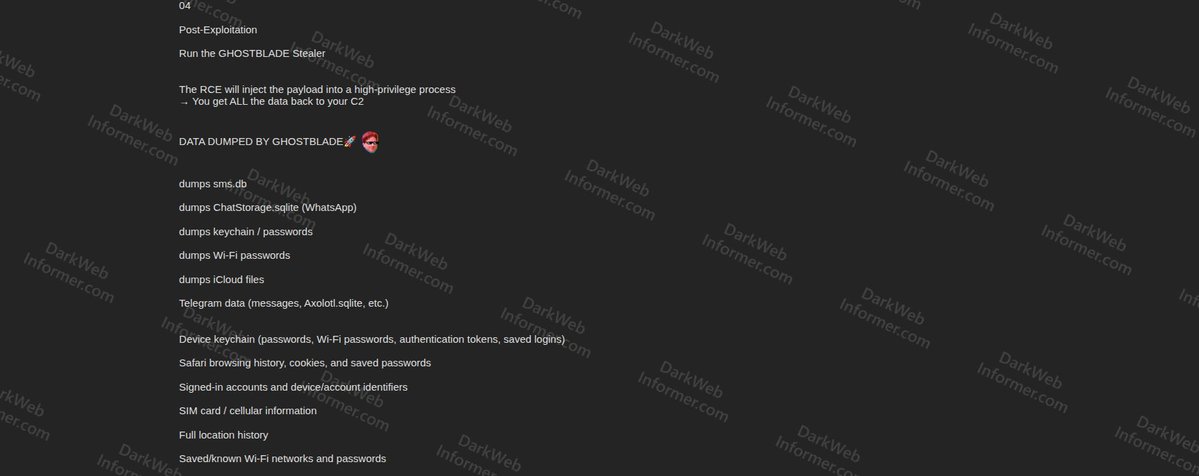
GHOSTBLADE Stealer dumps:
▪️ sms.db
▪️ ChatStorage.sqlite (WhatsApp)
▪️ Keychain / Passwords
▪️ Wi-Fi Passwords
▪️ iCloud Files
▪️ Telegram Data (messages, Axolotl.sqlite)
▪️ Device Keychain (passwords, Wi-Fi, auth tokens, saved logins)
▪️ Safari Browsing History, Cookies, and Saved Passwords
▪️ Signed-in Accounts and Device/Account Identifiers
▪️ SIM Card / Cellular Information
▪️ Full Location History
▪️ Saved/Known Wi-Fi Networks and Passwords
▪️ Find My iPhone Settings and Location Services Data
▪️ Photos (including metadata, hidden photos, screenshots)
▪️ iCloud Drive Files
▪️ Notes Database, Calendar Database
▪️ Health Data (Apple Health app)
▪️ Cryptocurrency Wallet and Exchange Data (Coinbase, Binance, MetaMask, Ledger, Trezor, Exodus, Phantom)
▪️ Keychain Items Related to Banking/Financial Apps
Operates as hit-and-run with data exfiltrated to C2 and traces/logs deleted automatically.
English
The Imo Prince retweetledi

I've tasted trying to fix people, and I've tasted forcing the truth down their throats. I highly recommend not caring more about people's lives than they do. No one is your assignment.
Not even the ones you love.
໊smolaraa@kesikesiluv
Hit me with the harshest reality truth.
English
The Imo Prince retweetledi
The Imo Prince retweetledi
The Imo Prince retweetledi

From Pharisee to Tax Collector: Rethinking Tinubu’s Kenyan Comparison
In a recent remark in Yenagoa, Bola Ahmed Tinubu suggested that Nigerians should find solace in being “better off than Kenya and other African countries.” While this may have been intended to soften the impact of economic hardship and rising fuel prices, the comment risks downplaying the severity of the current crisis. It echoes the biblical parable of the Pharisee and the Tax Collector in the Gospel of Luke (18:9–14). A similar warning is found in the Qur’an (53:32), which cautions against self-righteousness.
Like the Pharisee who boasted of his superiority over others to mask his own spiritual void, such downward comparisons serve more as a refuge than a remedy. This validated an earlier dismissive remark by President Ahmed Bola Tinubu during electioneering: “Na statistics we go shop?” Yet statistics remain indispensable - they are the language through which nations understand their condition and chart progress. No country can develop in isolation from measurable realities or without comparing itself with peers. Comparisons, when properly grounded, are not instruments of escapism but tools of accountability. What is objectionable is not comparison itself, but comparison stripped of credible, verifiable data—mere tax collector comparisons that soothe rather than solve.
On key development indicators such as security, the Human Development Index, life expectancy, GDP per capita, literacy levels, and electricity access, Kenya consistently outperforms Nigeria. Nigeria is the fourth most terrorised nation in the world, while Kenya is not among the ten worst. Kenya’s HDI ranking is 143 out of 180 countries, with a coefficient of about 0.630, compared to Nigeria’s ranking of 164 out of 180, with a coefficient of about 0.530. Its GDP per capita is roughly $2,200–$2,300, compared to Nigeria’s $807–$835. Kenya’s poverty rate is about 43% of the population (approximately 23 million people), while Nigeria’s is about 63% (around 150 million people), over six times that of Kenya. Kenya’s life expectancy is about 67 years, while Nigeria’s is about 54 years. The literacy rate in Kenya is approximately 81–85%, compared to Nigeria’s 62–65%.
Kenya’s electricity access is higher, while Nigeria has one of the lowest levels of electricity access in the world. Kenya has about 3.5 million out-of-school children, while Nigeria has about 20 million. Kenya’s inflation rate has been about 4.5% or lower over the past three years, while Nigeria’s has remained above 15% within the same period. Kenya’s exchange rate has been around USD 1 to KES 130 over the past three years, whereas Nigeria’s exchange rate rose from below ₦500/$1 to above ₦1,250/$1 within the same period. Even with developments in the Middle East and rising oil prices, Kenyans have not experienced the sharp increases in petroleum product prices seen in Nigeria.
Across other key indicators, Kenya also performs better. In the end, these indices clearly show that Kenya ranks higher than Nigeria on several development metrics. The standard of living of Kenyans is better than that of Nigerians. If the President considers Kenyans to be suffering despite these stronger figures, then Nigerians are in a far more difficult situation. He should therefore refrain from self-consolation and, in honest reflection, take responsibility for the situation and make a determined effort to drive improvement. This requires a posture of humility, accountability, and commitment to addressing the factors that have slowed Nigeria’s development.
A new Nigeria is POssible. -PO
English
The Imo Prince retweetledi

My own TL
Half of Twitter wants Tinubu out, the other half are horny but still wants tinubu out
A♡@Ashhleyyyya
Half of twitter is horny and the other half is suicidal.
English
The Imo Prince retweetledi

🚨 Credential Tool Circulating: “Hunter Mix Inboxer” (Cracked Version)
A threat actor is sharing a cracked version of a combo checker / inbox validator tool, commonly used to process large credential dumps (URL:LOGIN:PASS).
🧠 What This Tool Does:
• Validates email:password combinations at scale
• Checks for active inbox access (IMAP/SMTP)
• Filters valid accounts for further abuse
• Uses keyword-based parsing (e.g., PayPal, Coinbase, Instagram)
• Supports proxy usage and threading for automation
🧠 Why This Matters:
• Tools like this are critical in the credential abuse ecosystem
• Enable attackers to turn raw combo lists into high-value, verified accounts
• Often used in:
•Account takeover (ATO) campaigns
•Financial fraud (crypto, banking, e-commerce)
•Phishing follow-ups using real inbox access
🧠 Notable Signals:
• “Cracked” version → lower barrier to entry for less-skilled actors
• Integrated keyword filtering → targeted monetization (crypto, fintech, social)
• Telegram distribution → typical rapid spread channel
⚠️ Key Risks:
• Increased success rate of credential stuffing attacks
• Rapid scaling of ATO operations
• Abuse of compromised inboxes for internal phishing / BEC
🔍 Defensive Considerations:
• Enforce MFA across all external-facing services
• Monitor for suspicious IMAP/SMTP logins
• Detect impossible travel / anomalous access patterns
• Encourage password hygiene and credential rotation
⚠️ Status: Active tool circulation – supports ongoing credential-based attacks
#CyberThreat #CredentialStuffing #ATO #ThreatIntel #DarkWeb

English
The Imo Prince retweetledi
The Imo Prince retweetledi
The Imo Prince retweetledi
The Imo Prince retweetledi

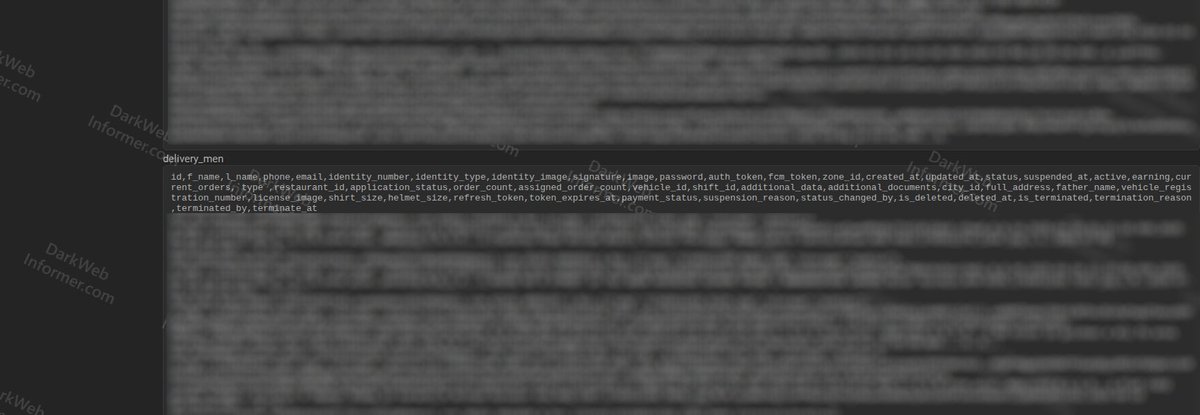
‼️🇵🇰 The database of FoodPapa (foodpapa.com), a Pakistani food delivery app, has allegedly been leaked on a popular cybercrime forum.
‣ Threat Actor: penguinbrew
‣ Category: Data Breach
‣ Victim: FoodPapa (foodpapa.com)
‣ Industry: Food Delivery
‣ Country: Pakistan
‣ Size: 238.3 MiB compressed / 1.5 GiB uncompressed (full SQL)
‣ Cleaned Tables: 13.5.3 MiB compressed / 27.01 MiB uncompressed
‣ Backup Date: 02/01/2026
The threat actor claims FoodPapa left a backed-up database exposed, allowing anyone access. Both the full SQL and cleaned tables for users, delivery men, and admin are available for download.
User table data includes:
▪️ First Name, Last Name
▪️ Phone, Email
▪️ Image
▪️ Phone/Email Verification Status
▪️ Password, Remember Token
▪️ Interest, Firebase Token
▪️ Status, Order Count, Login Medium
▪️ Social ID, Zone ID
▪️ Wallet Balance, Loyalty Points
▪️ Referral Code
▪️ Auth Token, Refresh Token
▪️ Suspension Reason
Delivery men table data includes:
▪️ First Name, Last Name
▪️ Phone, Email
▪️ Identity Number, Identity Type, Identity Image
▪️ Signature, Image, Password
▪️ Auth Token, FCM Toke
▪️ Zone ID, Status, Earnings
▪️ Current Orders, Restaurant ID
▪️ Vehicle ID, Shift ID
▪️ Full Address, Father Name
▪️ Vehicle Registration Number, License Imag
▪️ Shirt Size, Helmet Size
▪️ Payment Status
▪️ Termination Reason and Status

English

There is only one person I'm comfortable with knowing me on X
j e a n@jeanisalunatic
The first rule of twitter is you do not tell people in real life about your twitter.
English










