No Name
1.9K posts


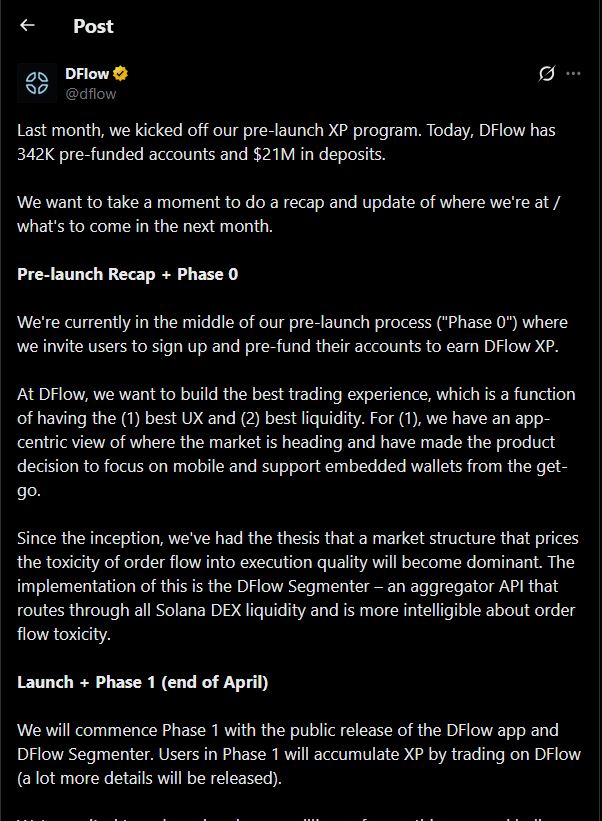
No Name
@macrealer_
God first Web3 Arsenal COYG Kendrick Lamar J. Cole Slim shady


Not only is he doing that but.. @SolanaFndn will not do anything because they are backing Dflow to take over JUP @italoacasas But were NOT supposed to know that because @solana will get upset BUT there has been bragging in the dflow office. but we can provide the receipts to JUP









in under 48 hours, @OpenWallet has received 250+ applications to join the first OWS Hackathon! thank you to @solana, @base, @dflow, @MyriadMarkets, @circle, @pacifica_fi, @virtuals_io, @Ripple, @SuiNetwork, @xmtp_, X402, @AlliumLabs, and @nansen_ai for making it possible!

@A_La_nd @dflow @MetaDAOProject Wym rug?You need to fill out the form to get the reward And also l still waiting next info from them

E be like say na Victor Osimhen be the new update. Dear @victorosimhen9 I don’t need much from you and neither am I interested in coming to Turkey bcos the plane is full already. In conclusion: instead of going to Turkey, I’ll prefer the currency to buy Turkey here in Nigeria.



It's literally never been easier to build on @Solana. DFlow is now live in Poof. @Poofnew is the fastest way to build and deploy Solana apps. Describe what you want to build in natural language and Poof’s AI agents handle the database, smart contracts, actions, and UI. From prompt to production in minutes.