
Michal Převrátil
65 posts

Michal Převrátil
@michprev
Ethereum security tooling developer at @ackeeblockchain





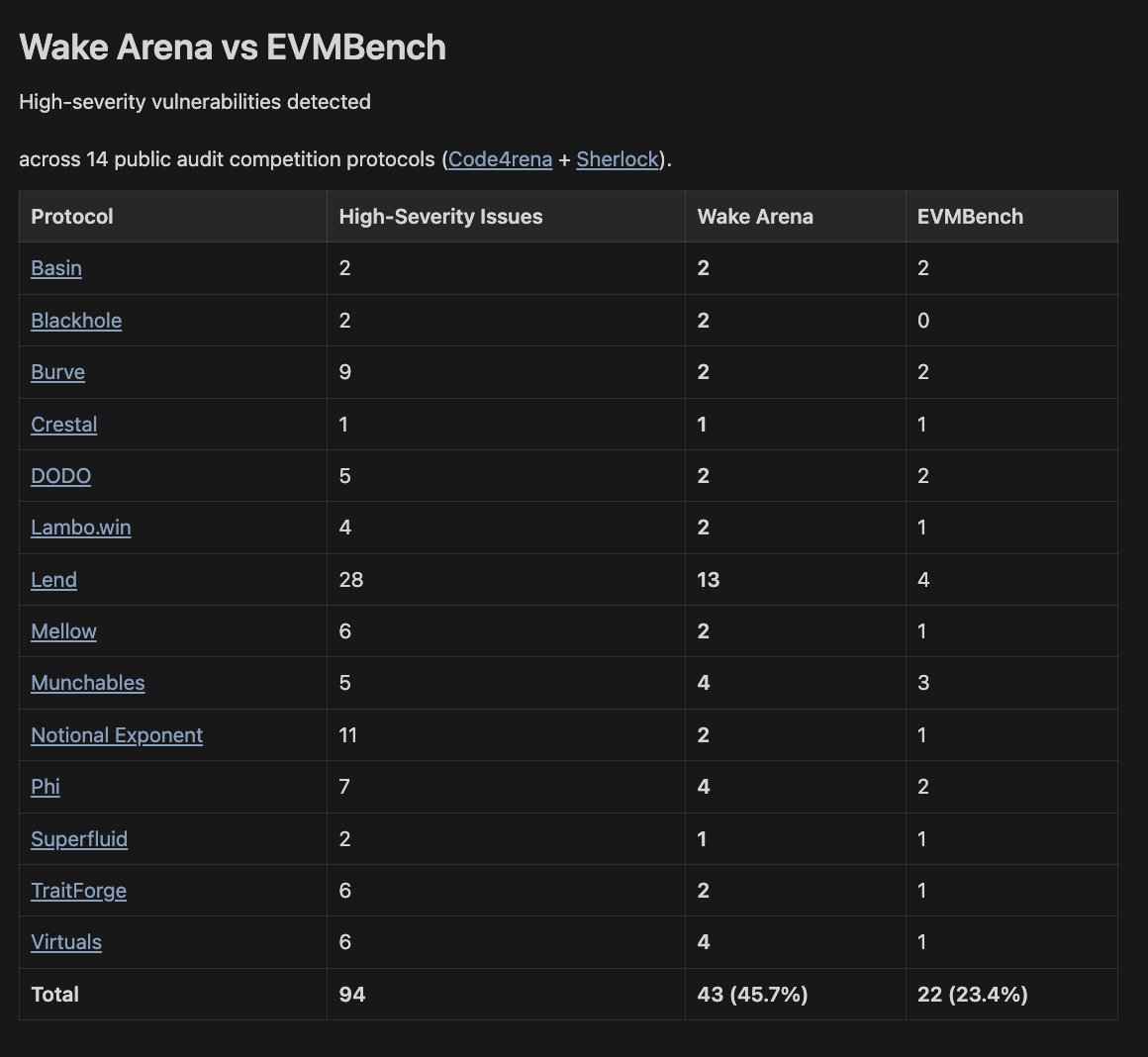
We ran EVMbench on @zellic_io's public dataset, high-severity only. @WakeFramework beat OpenAI by 96%. Looks like AI isn't killing this startup yet. EVMbench (codex-gpt-5.2-xhigh): 22/94 Wake Arena (already tested pre-release): 43/94 github.com/Ackee-Blockcha… @OpenAI @paradigm @osec_io

new collab from @paradigm and @OpenAI: evmbench is a benchmark and agent harness for exploiting smart contract bugs a few months ago, the best models found <20% of critical, fund-draining @Code4rena bugs in our benchmark. today they find > 70%

Wake Arena: multi-agent AI audit with graph-driven reasoning and LLM-tailored static analysis. 43/94 high-severity vulnerabilities found in historical audit competitions. 26 findings, including 5 criticals in 4 production audits by Akcee in Nov 2025. Full benchmarking report: ackee.xyz/blog/wake-aren… Built by senior auditors securing Lido, Aave, Axelar, and Safe. 50%+ true positive rate. Scan your protocol → ackee.xyz/wake/arena Follow @WakeFramework for product updates and insights.


Today @Meta_pool lost $27M to a forgotten mint() function. In reaction to the incident, we are open-sourcing our extension's public functions printer to help prevent such vulnerabilities in the future. Thread ↓






1/ Fuzzing is a well-known software testing technique, but what is Manually-Guided Fuzzing? This innovative testing approach combines the strengths of stateful and white-box fuzzing to deliver more efficient and targeted vulnerability detection. ↓

Wake 4.16.0 is live! Most notable changes: 🔹Added support for Solidity 0.8.29 and Osaka EVM 🔹Implemented Foundry compilation config options importing with wake up 🔹Migrated to Sourcify v2 & Etherscan v2 APIs






