wang
20 posts


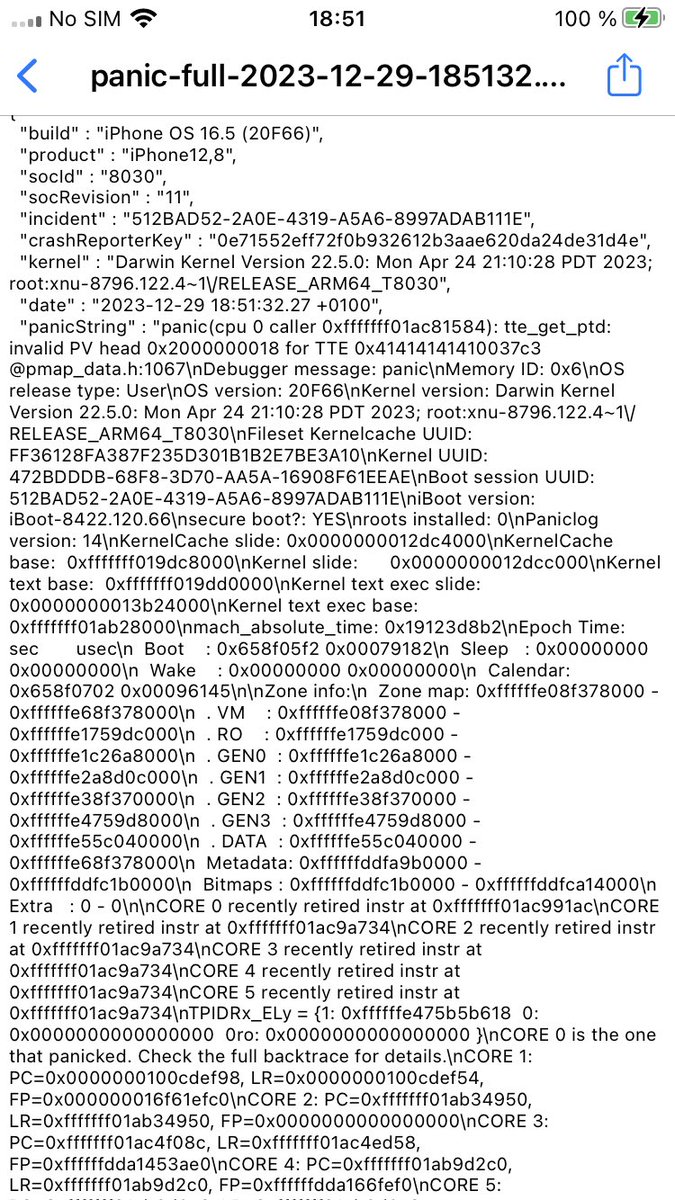
For the first time in over two years, there is set to be a new kernel exploit for up to iOS/iPadOS 18.7.1 and 26.0.1 - including the latest EoL versions for 15.x (presumed)/16.x/17.x. [Note: Just like the Coruna kit chain a few weeks ago, stuff here is subject to change/revision.] This is - as you may or may not already be aware of - the result of another 1-click malware chain, known as DarkSword. You can read more about this chain from Google at cloud.google.com/blog/topics/th… (see reply though for a note on a previous Google inaccuracy with Coruna). I'm not going to into depths on how stuff is coming from this chain because: - We do not need a repeat of how certain things about Coruna were handled - Linking to anything directly would legitimately result in this account probably being nuked... which I am not inclined to deal with thank you very much But, suffice to say, the whole chain is public to a degree, and stuff is absolutely coming from this chain. Now, that raises the obvious question - What is the state of anything new for jailbreaking? It's worth noting that the DarkSword chain does not utilize any PPL/SPTM Bypass (needed for arm64e jailbreaks on 15.x and later), which means that we aren't getting any new exploits from that side of the coin. But, we still have the PPL/SPTM Bypasses from the Coruna exploit kit. Even better, two of them (Sparrow and Rocket) were not patched until iOS/iPadOS 17.4, which is actually one minor version later than when the last kernel exploit in the kit (Gruber) was patched (17.3). So, assuming everything goes as optimistically as reasonably possible: - arm64 could get a semi-untethered jailbreak up to iOS/iPadOS 18.7.1 (including EoL 15.x/16.x/17.x) - arm64e could get a proper jailbreak up to iOS/iPadOS 17.3.1

@duongduong0908 I've already turned on the VPN and connected to the WiFi, but it still says it can't connect.



Sorry for the delay with EnsWilde 2.0. I’m currently testing the zPatch Custom feature before releasing it. #EnsWilde


Okay for transparency there is a pretty big problem with TrollStore 2 left: All apps seem to get the same data container 🫤, the one of GTA Car Tracker, because that's the code directory used for every app Not sure if this is fixable, but I will look into it soon