7.8K posts





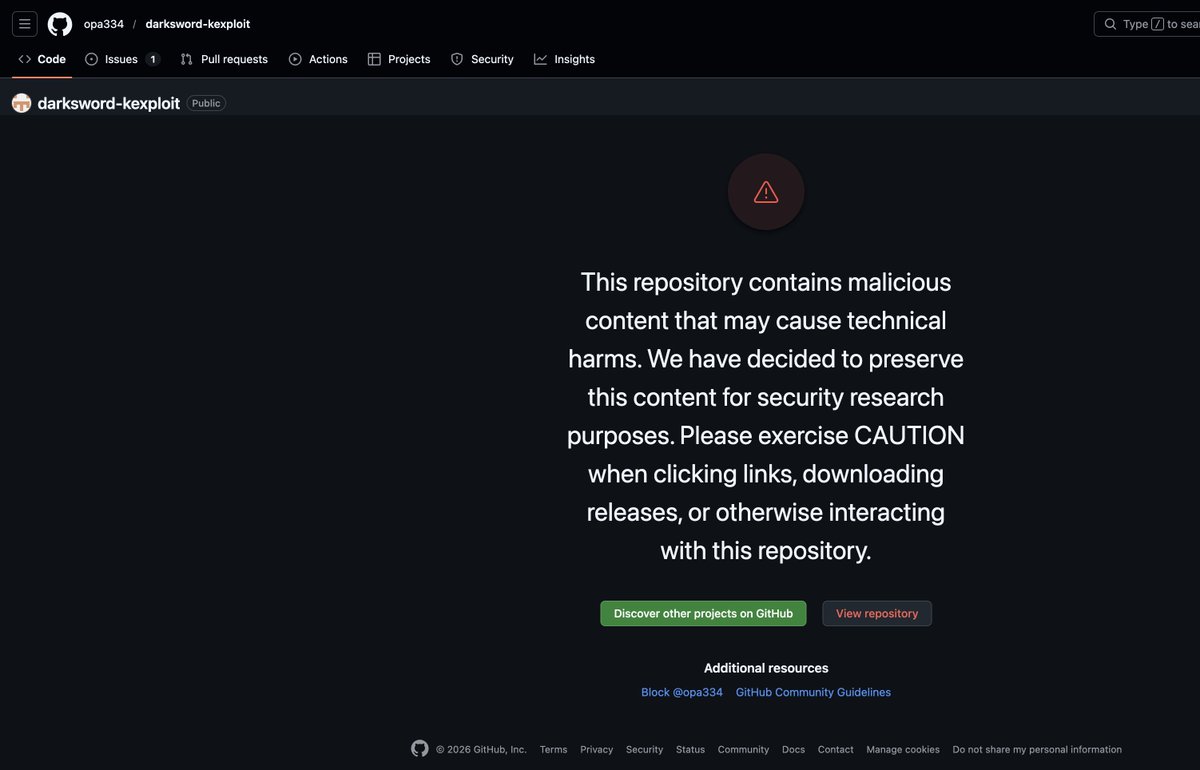
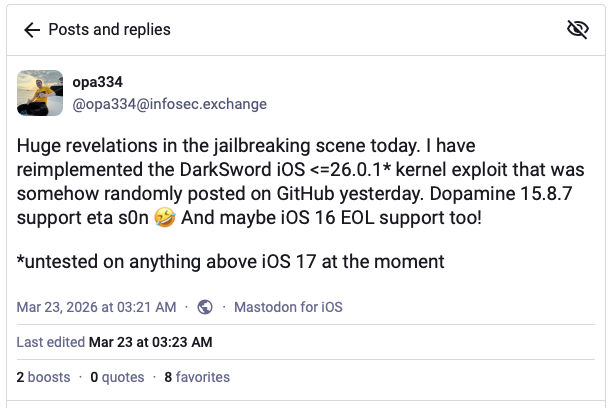
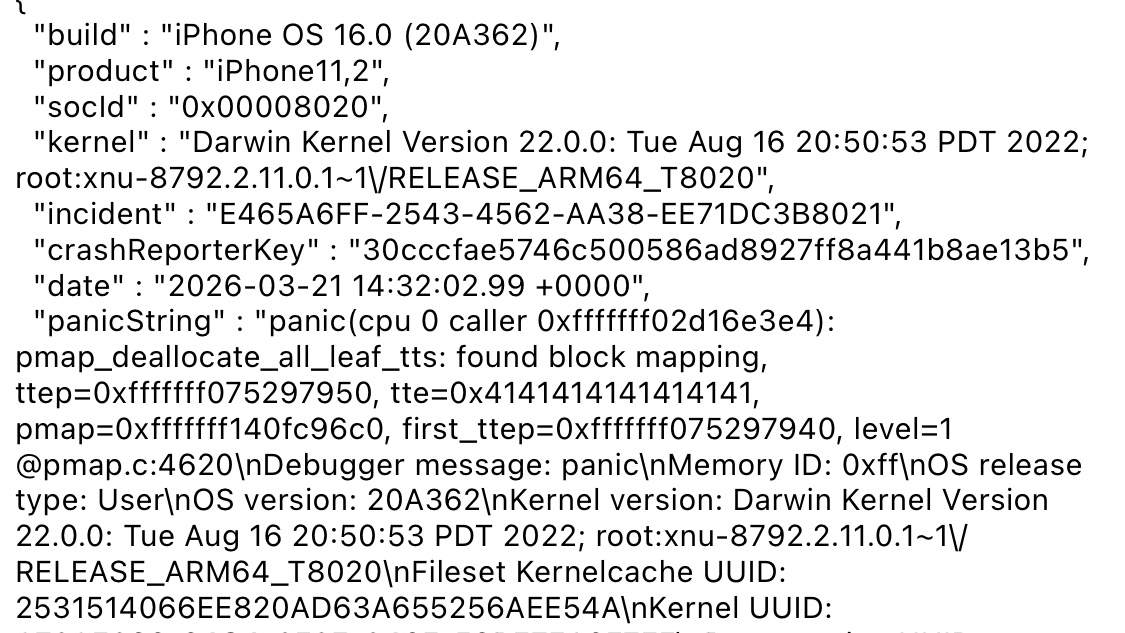
🚨 Faites la mise à jour de votre iPhone et iPad AUJOURD'HUI s'ils tournent encore sous une version antérieure à iOS 26.3.1, iOS 18.7.6, iOS 16.7.15 et iOS 15.8.7 (soit 25% d'entre vous) Le code source du logiciel espion DarkSword a été publié sur GitHub. Il est fonctionnel, n'importe qui peut l'utiliser contre vous désormais. Le kit exploite six failles, dont trois zero-day. La chaîne commence par WebKit (le moteur de Safari), traverse plusieurs couches de sandbox, puis atteint le noyau d'iOS. En quelques minutes, contacts, messages, historique de navigation, trousseau iCloud et portefeuilles crypto sont exfiltrés vers un serveur distant. Merci @Clubic pour l'alerte. clubic.com/actualite-6058…


I think — genuinely — the only hope for jailbreaking at the point is if the EU forces manufacturers to have unlocked bootloaders. It is deeply fucked up to me that you can buy a $1000 computer and are not allowed to install your own software on it.

“Semi-jailbreak” makes me immensely sad