
Xavier Bellekens
10.5K posts


@noktec
Founder of Lupovis


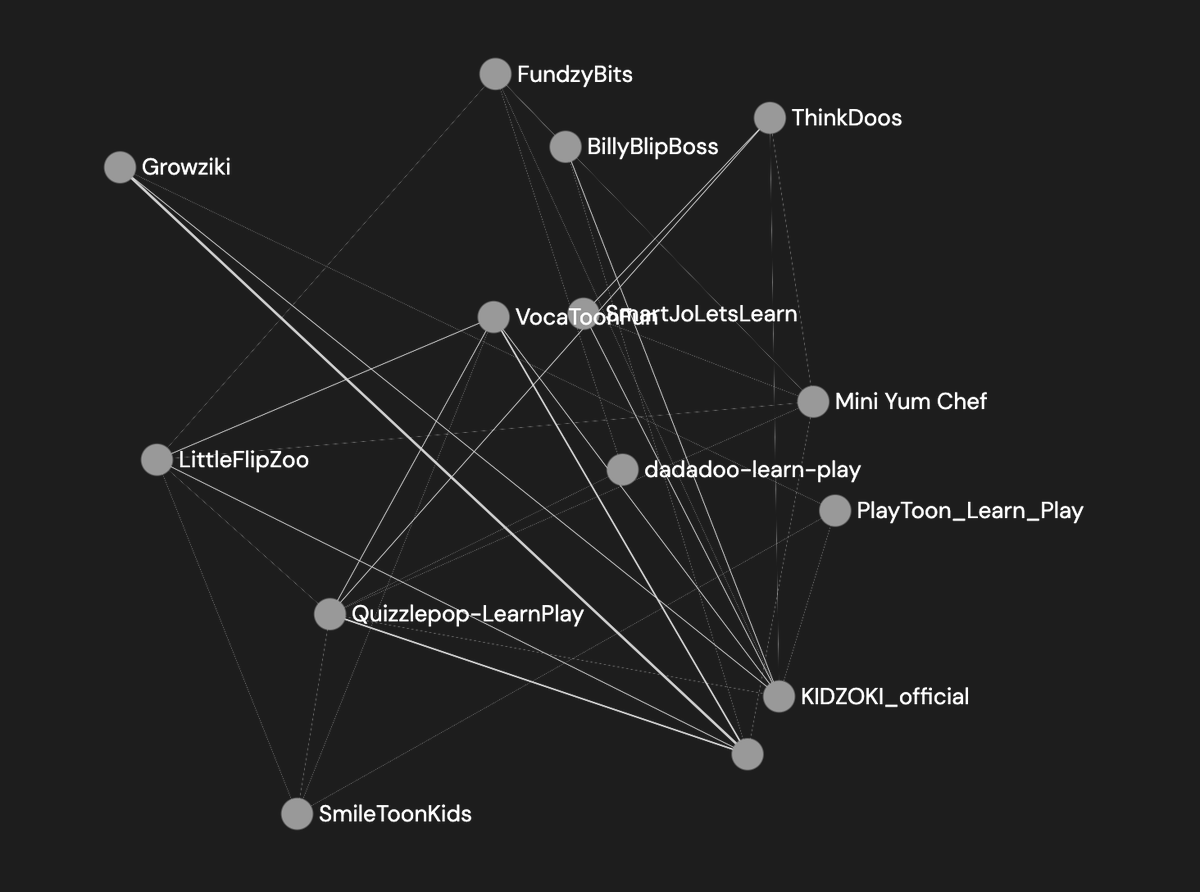




Introducing Project Swarm: a research initiative to defend the network edge and we're inviting you to join. Deploy a sensor on your infrastructure, capture real attacker traffic + compare what's hitting you to the GreyNoise global baseline. Join today! 🐝





We’re seeing CVE-2026-27944 hit our telemetry. Currently without a KEV inclusion. Unauthenticated access to /api/backup in Nginx UI versions lets an attacker download a full system bkp, and the response discloses the material needed to decrypt it via X-Backup-Security. Patch now








So @CiscoSecure went around all the rooms of the @Hilton at @OneRSAC at night to place one time use - small lcd video of their CEO delivering a message … loads of waste - let’s look what’s inside
