
Numbers Protocol
4.6K posts


@numbersprotocol
Open & decentralized network. Ensure provenance for all digital media created by humans & AI.|Powered by $NUM https://t.co/UbiUUpbSqc





#DoYouKnow getting a voice online isn’t hard in 2025. Proving it is. We’re entering the era where voice can be generated faster than it can be explained. A clip needs an evidence trail: who recorded it, when, and whether it was edited (timestamp, device, source context).

The blue checkmark confirmed who posted it. Not whether what they posted is real. That distinction got completely lost. And it means verification as a concept is actually broken in a very specific, fixable way.


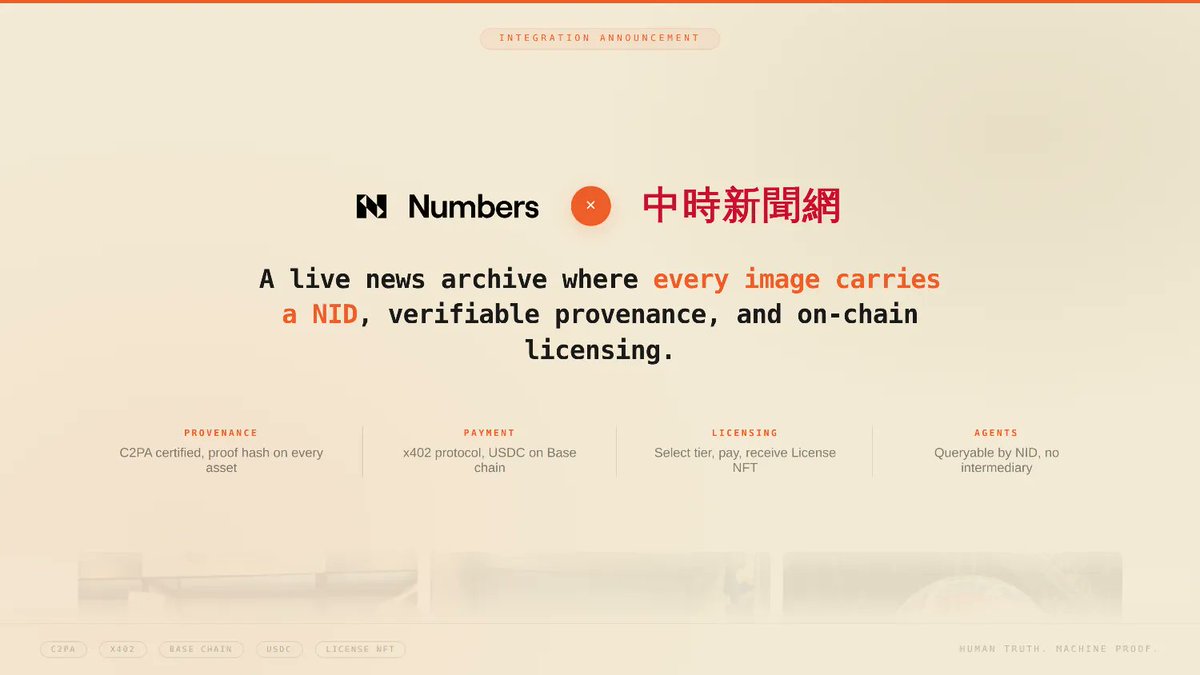
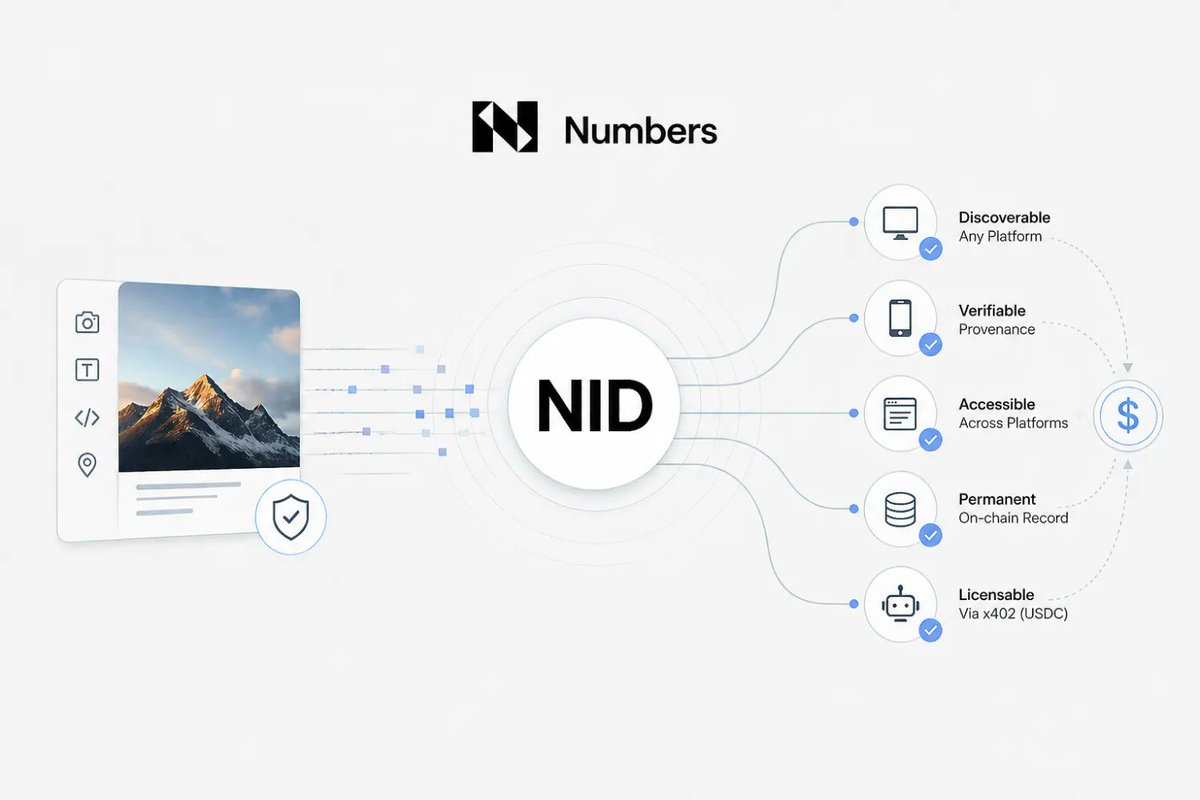
Do you know what makes a piece of content readable by an AI agent, not just by a human? Traditional metadata, EXIF data, file descriptions, alt text, gets stripped the moment content moves between platforms. Copy an image from one site to another and the origin is gone. An AI agent crawling that content has nothing to verify. NID changes this at the infrastructure level. When content is registered with a Numbers ID on Numbers Mainnet, three things happen: A C2PA signature is embedded directly in the file at creation. The provenance record is written on-chain, creating a permanent reference that persists regardless of where the file travels. The asset becomes discoverable and licensable through x402, so any agent can find, verify, and pay in USDC programmatically. The key difference: traditional metadata is attached to the file and can be stripped. A NID is indexed on Numbers Mainnet and follows the content everywhere. An agent can always trace back to the origin. That is why PyroImage photojournalists, China Times articles, and BlockTrend newsletters are all indexed with NIDs. The content is not just published. It is agent-readable from day one. What content would you want to remain verifiable, even after it leaves your platform?









What happens when blockchain journalism gets its own provenance layer? Blocktrend, one of the most respected blockchain tech publications, now integrates x402 for content licensing. Numbers handles provenance registration and the x402 payment rail. Blocktrend handles editorial, distribution, and audience. Every article carries a NID with full attribution: author identity, publication timestamp, content hash, license terms. Agents and platforms can query, verify, and license Blocktrend content programmatically, no manual negotiation required. PyroImage proved x402 works for photojournalism. China Times proved it works for news photography archives. Blocktrend proves it works for tech journalism. Three publishers, three content types, one verifiable licensing stack. The infrastructure is publisher-agnostic. The pattern is the point. Browse, verify, and license blockchain journalism on-chain: x402-blocktrend.numbersprotocol.io Which content vertical should go on-chain next?

Public chats with VCs do not happen every day. So if you have not revisited this one yet, this is your sign. The AMA POAP claim campaign with @NOTALONExyz is now live. Go check the recording again, then mint your POAP here: ama.creativeorigin.ai/ama/2026-03-25 Mint your POAP and lock in your receipt.

MemeDNA extends provenance with identity 🧬 Now open for exploration 👉 memedna.site

Someone sends you an image. You’re not sure it’s real. What can you even do? Reverse image search? Metadata check? AI detector? Manual cross-referencing? Most of these tools either return nothing useful or give you a “maybe.” They all work backwards, trying to reconstruct origin after the fact. And they break at scale. The alternative is registering origin at the point of creation. A timestamp, a cryptographic signature, a permanent on-chain record indexed with NID. Immutable metadata. AI attribution built in. That's what Numbers Protocol does. Verification isn't a guessing game at the end. It's a fact recorded at the beginning. Try it yourself with the updated ProofSnap App, now with improved C2PA implementation. iOS: apps.apple.com/app/proofsnap-… Android: play.google.com/store/apps/det… What's the last image you wished you could verify?

