Numb3rs
47 posts


Numb3rs
@numbrs
doing cool things such as opening files with nano
Katılım Nisan 2021
518 Takip Edilen278 Takipçiler

@vxunderground if 2000+ lines of code is "basic" the rest of us r cookthed
English

If you're curious what a basic position independent polymorphic mutation engine looks like in C (compiled as C++), this is what it looks like.
I'll do a write up later.
gist.github.com/vxunderground/…

English

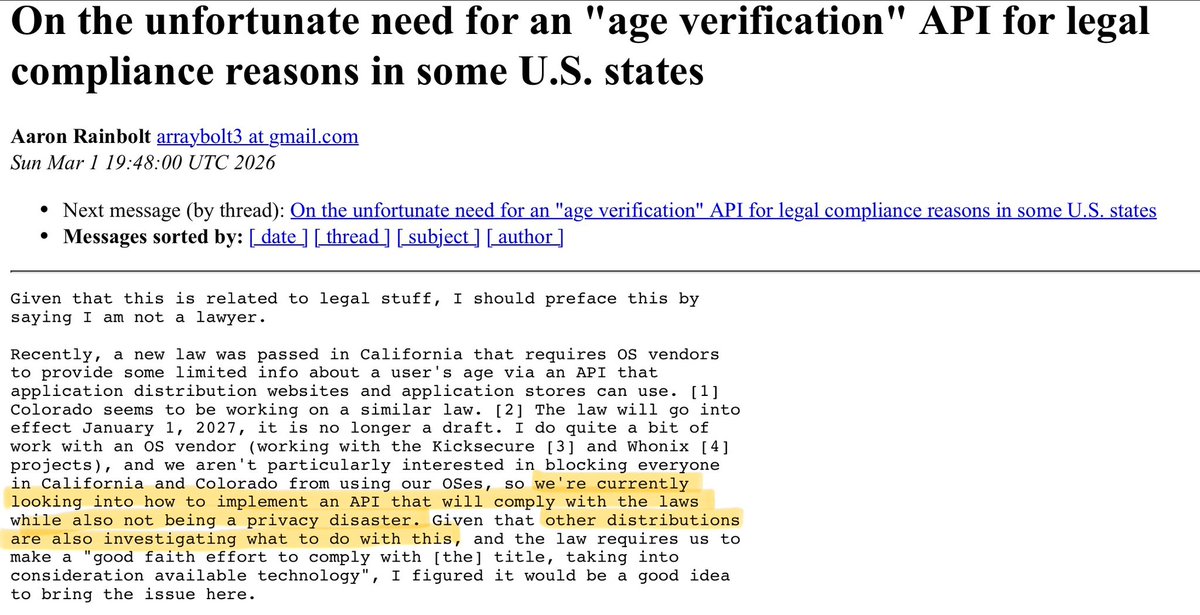
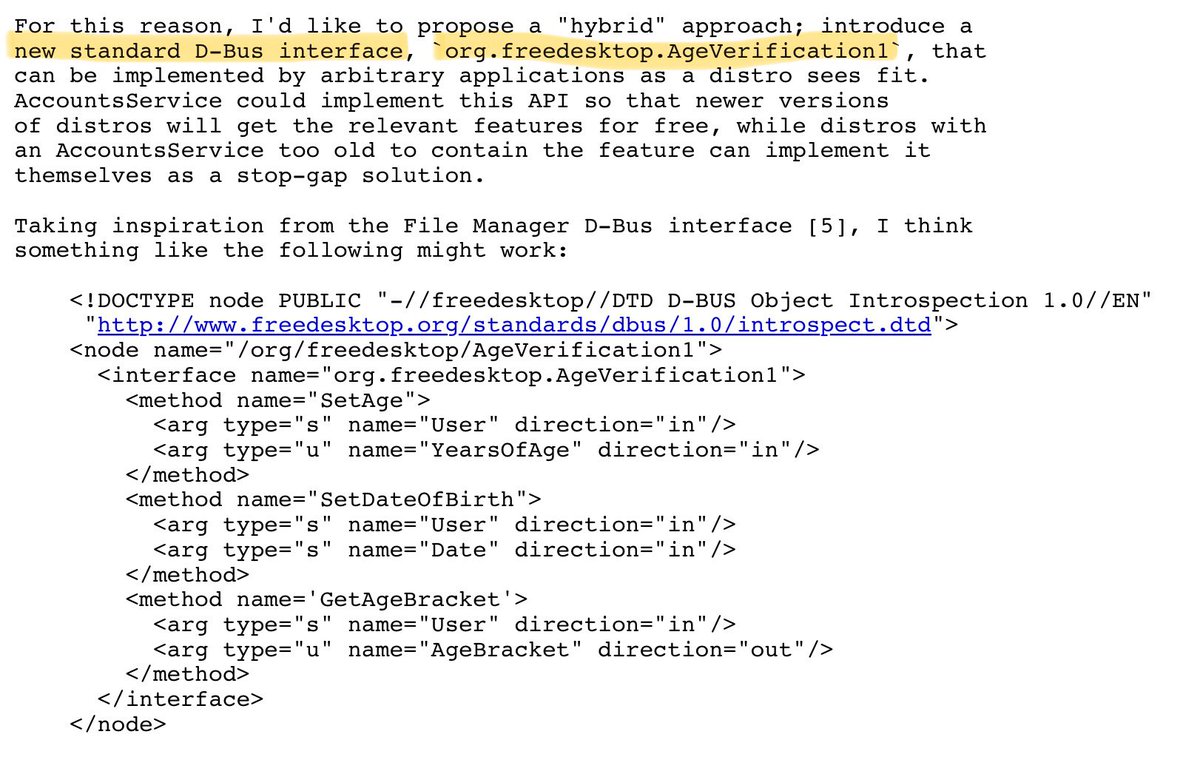
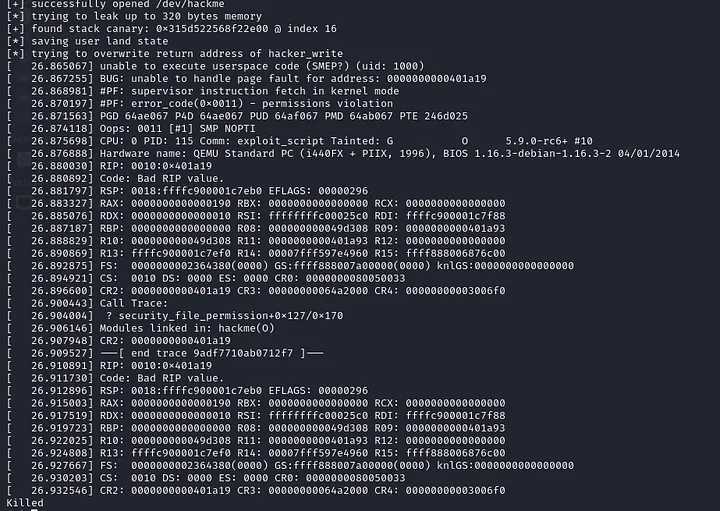
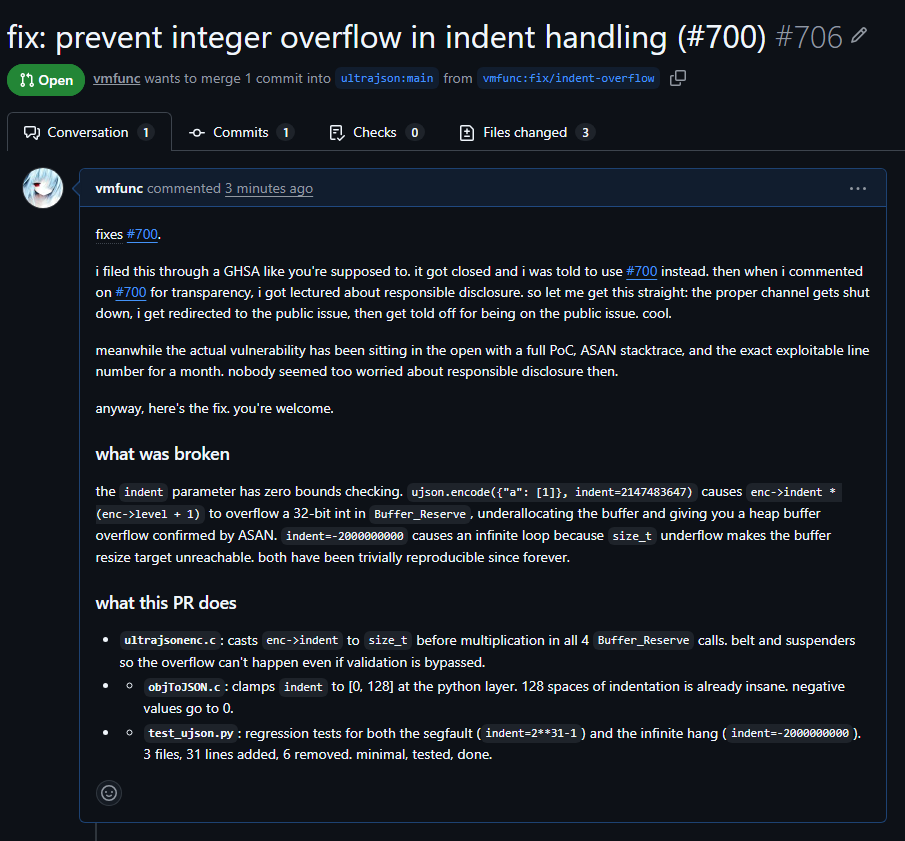
i am extremely infuriated. heap overflow in ultrajson sitting public with a full PoC + ASAN stacktrace for a MONTH
ultrajson has a heap overflow. PoC's been public for a month. i filed the GHSA (correctly), got it closed, got redirected to the public issue, then got lectured about responsible disclosure *on the public bug with the working exploit attached*
i wrote the fix out of spite. that's it. that's the whole story. open source security is a fucking joke
English

@cr4zyengineer @m1thr1da @realpastaya i might have been angry for nothing and I am sorry but my point stands: why would you lie about it being a bof ? it doesn’t make sense. Sorry again for the previous tweet 😛
English

@numbrs @m1thr1da @realpastaya What is wrong with you is the better question, your response is very fucked up...?
English

@cr4zyengineer @m1thr1da @realpastaya why would you lie about such thing ? Buffer overflow in a discord bot ? Cmon man wtf… + saying “my kernel research paid off” when you’re just reusing a token - what is wrong with you ?
English

Yeah you got me.. I spiced it a little more up.. The moderator team made a fatal mistake in the past and leaked the discord bot token to a friend of mine(on a Minecraft ban reason disclosure as the bot served as a bridge between Minecraft server to the discord server) which I then tried to use to connect to it.. and well it worked. Really morons.. have an unimportant bot admin role and leaked its token them selves… sooo it was a pure human mistake..
English

@guime_guimeLove @5mukx From what I read from the writeup it appears that the sRIP offset is <1000 so the buffer’s size isn’t 1000 bytes (which doesn’t make sense regarding the check i agree)
English

@5mukx Why does the size check in the center block (cmp rbx, 1000h) fail to prevent a buffer overflow, even though it appears to be a correct security validation?
English

@UK_Daniel_Card “Chap” you should take a chill pill, no need to be vindictive. The CVE here isn’t important , my point is that there are some applications who don’t use TLS and use proprietary protocols that are sometimes/usually not the best.
I know because that’s what i focus my work on.
English

I'm not sure I would be surprised that sometimes there are vulnerabilities chap... that assumes some kind of view that I am blind to vulnerabilities, which I'm not.
it's 2026.... not 2019 (re CVE date)
what is the majority device used out and about? (a smart phone)
I know because I go outside.
I also tap networks and watch traffic.....
I also setup FREE WIFI access points and watch.
English

@UK_Daniel_Card You’d be surprised ^^ take a look at CVE-2019-18800 for example. Not sure if I understand your message entirely but those applications are also on desktop.
English

@T3chFalcon IMAGINE 😭😭 focusing on the delivery instead of the lesson 🧠✨
Like… argue with the MESSAGE, not the font, the tone, the vibes, the commas 😭💀
If it made you think, it already WON 🏆🔥
English

Renaming a file is not OPSEC.
Windows keeps a permanent diary called Amcache.
It doesn't just trust the filename you typed. It extracts metadata from the binary's Version Resource (VS_VERSIONINFO). Rename payload.exe to homework.pdf.exe if you want.
If the developer didn't strip the metadata, Windows logs the Original Filename anyway.
But it gets worse. Amcache is the ultimate backup:
Ghost Execution: You deleted the file? We still have the SHA1 Hash. We know exactly what malware ran even if the disk is clean.
Anti-Forensics Trap: Cleared your Prefetch? Almost nobody wipes the Amcache hive. An empty Prefetch + full Amcache = Proof of Intent.
The Time Machine: It logs the exact second of First Execution and the Compile Date.
Location: C:\Windows\AppCompat\Programs\Amcache.hve
You changed the name. Windows kept the identity.
💀
IT Guy@T3chFalcon
Amcache
English
Numb3rs retweetledi
🎄 New Root-Xmas Challenge 🎄
✨Today, heap your skills and parse your way through Santa’s picture-perfect surprises!
📌Submitted by : Numb3rs
🔗Details & participation here: ctf.xmas.root-me.org
Good luck to you all !🎅

English

Polish police detained three Ukrainians with professional hacking equipment: FLIPPER, spy detector, antennas, laptops, SIM cards. Charges include attempted damage to IT data critical for national security. Suspects couldn't explain equipment's purpose (when asked, they suddenly "forgot" how to communicate in english language). The likely goal was close-access cyber operations.



English

Dug into a custom router protocol for fun.
Turned out to be: type confusion + command injection = RCE 🎉
Full write-up here: 📎numb3rs.re/posts/abusing_…
English

@NaMi____NaMi @popovicu94 This is how SROP works. We make a segfault so that we can control the state in which the kernel is gonna put the process after the signal.
English

Ever wondered how a Linux program can catch a signal, run custom code, and then resume *exactly* where it left off, as if nothing happened?
It's not magic. It's a carefully choreographed dance between your process and the Linux kernel, starring a syscall that never actually returns: rt_sigreturn (#15 on x86_64).
Here's how it works. 🧵👇
English

@ChadSigmaRizz @osec_io Aslr is bypassable with a leak or relative writes
English

@osec_io Isn't this an operating system issue ? How does it get past ASLR ??
English

@JDG_1980 @robertgraham this could be a never ending debate and i don’t care that much but those mitigations can be bypassed + i don’t see how the end-user would accept using a software that is vulnerable to such a strong primitive (for this specific vuln)
English

@numbrs @robertgraham Regarding this particular codec crash (use-after-free), standard OS or compiler-level mitigation measures like ASLR make it considerably less likely that it could actually be used as a vehicle for ACE or other serious exploits.
English

This is the core tweet of the Google-vs-FFmpeg debate.
FFmpeg is justifiably upset, Google is swamping it with vulns that the FFmpeg project doesn't have the resources to fix. This is especially a big deal since such projects struggle to attract necessary talent in writing codecs, and this sort of thing demotivates their volunteers. It can kill the project simply by driving their most talent people away.
On the other hand, the existence of vulns is not Google's fault. They are just finding them shortly before hackers do, being only 6months to a year ahead of hackers figuring out the same AI tricks. It's a reality everybody has to deal with.
English

@JDG_1980 @robertgraham the end user doesn’t know ffmpeg exists + google is never gonna give a poc that does code exec for obvious reasons
English

@numbrs @robertgraham Perhaps, but that's not what the proof-of-concept demonstrates. Not every memory error necessarily enables arbitrary code execution, exfiltration of user data, corruption of existing HDD data, or anything else a normal end user would care about.
English