Paweł Hałdrzyński
285 posts


Paweł Hałdrzyński
@phaldrzynski
Researching web applications' security at daylight - auditing smart contracts at night







Nice trick showing that the very same zip can be seen differently by two different programs. I've examined how this quirk could help us in zip path traversal attacks: blog.isec.pl/disguises-zip-…



I'm super excited that my research: "Disguises Zip Past Path Traversal" has been nominated to PortSwigger's Top 10 web hacking techniques of 2025. If you've enjoyed the read, a vote would mean a lot! Link to vote in the replay below 👇

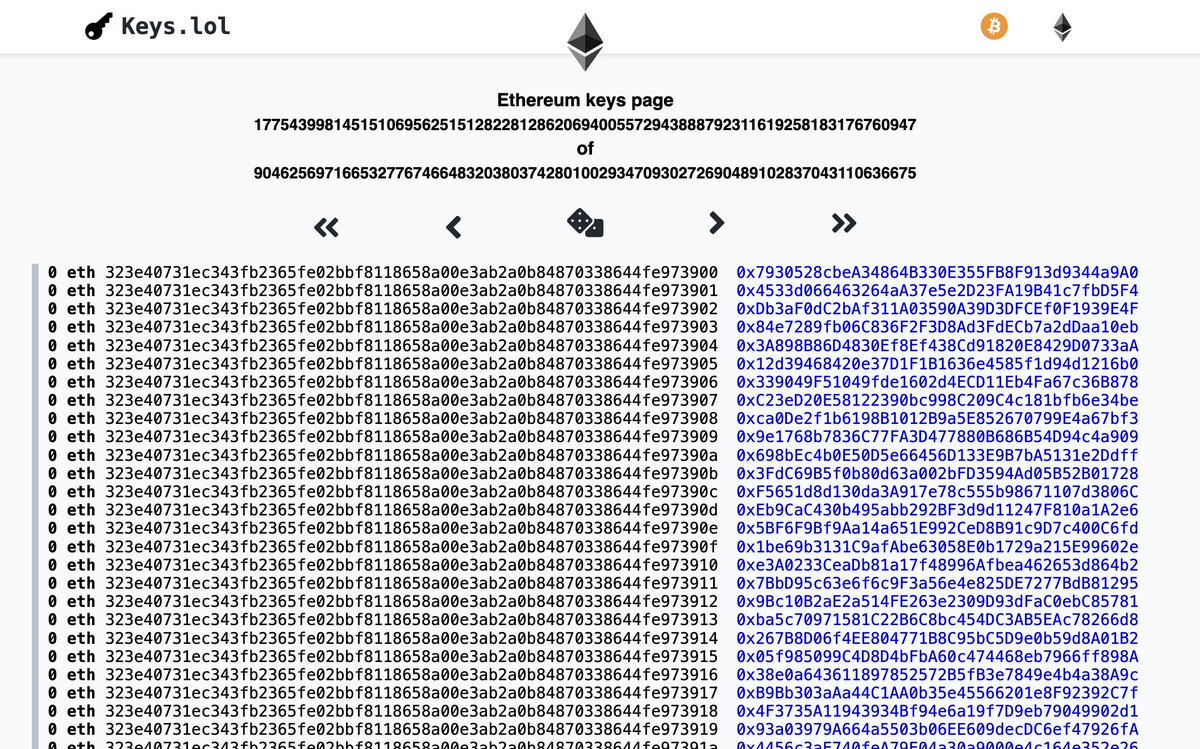
one way to solve spamming from humans and AI is to introduce a staking mechanism. If bug hunters wants to submit a vulnerability, they stake a few hundred dollars and get 5x their stake back if the vulnerability is valid. the same applies to git PR spamming, if anyone wants to open PR let them stake their dollars and pay if it gets merged.









HTML tag names must start with an ASCII letter. If they don’t… jsfiddle.net/4v6xksaf/ #xss











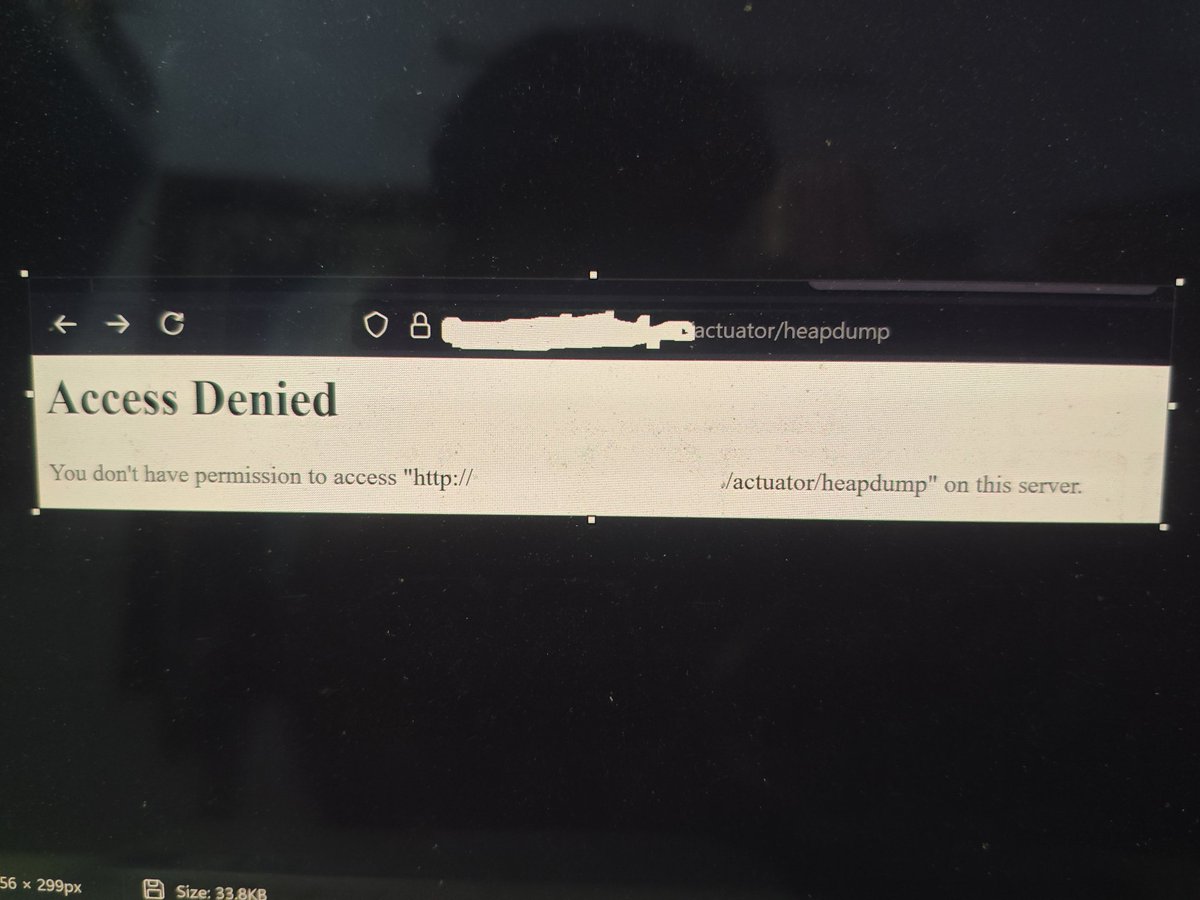
Just got my first RCE 🚀💀 #CVE-2025-55182