
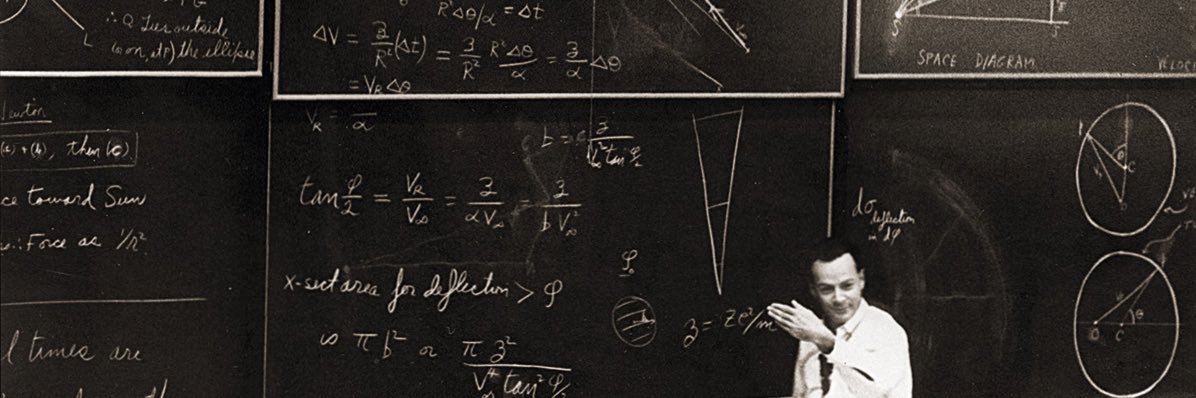
@vaibhavchellani @worldnetwork Hubble‘s ideas still live on to this day!
worldcoin.org/blog/engineeri…
English
philzip
50 posts



Introducing World Chain, a new blockchain designed for humans ⚪️

Global Value Numbering using Schwartz-Zippel lemma and random functions. Feels like cheating.





















Scanning people’s eyes for near-perfect Sybil resistance at the @worldnetwork office 🪩




Bear market fun fact 🐻 Back in Feb 2022, there were under 100k @safe's in existence. Today, that number sits at over 1 MILLON across 5 chains. Polygon (715,385) Mainnet (118,555) Arbitrum (78,263) Gnosis Chain (75,065) Optimism (23,397) gm, happy friday builders 🌅

