ًً
4.1K posts


ًً
@povertyhacked
啟示錄 she'll encased in concrete


How to create AI digital identities that platforms can't detect AI agents need human-like digital identities to function. Google accounts. X accounts. Discord. Telegram. Facebook. Without real platform accounts, sophisticated AI agents can't post, can't scrape, can't automate. The problem: Platforms detect and ban bot AI agent instantly. Why? Because most AI agent setups look like bots: VoIP numbers (60-80% rejection rate) Shared pool proxies (contaminated IP reputation) Automation fingerprints (Selenium, Puppeteer detected) Platforms run fraud scores on every signup: - IP classification check - Phone number verification - Device fingerprint analysis - Behavioral patterns AI agents fail all four checks. What creates human-like identities: Dedicated Numbers (non-VoIP) - Real US carrier number assigned exclusively to you - Unlimited verifications across every platform - Consistent identity (platforms trust repeat usage) Dedicated Mobile Proxies - Real 4G/5G carrier IP (T-Mobile, Verizon, AT&T) - Single-user (no shared pool contamination) - Low fraud score (mobile IPs whitelisted by default) MCP Integration: Claude, OpenClaw, MCP agents automate: - Account creation - Verification flows - Multi-account orchestration The Result: Your agent is indistinguishable from actual mobile user, instant platform trust. Build you agents with: voidmob.com


@GoodTexture Do you own any CYPH?









Join us tonight! We have important news! 🍫 twitter.com/i/spaces/1YqKD…


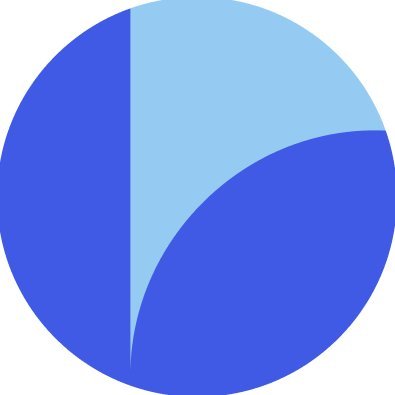
Best swap rate is useless if your funds get frozen! Most swap apps show you the best rate. Unstoppable does that and shows you the risk too! For every swap quote you see the provider risk profile because the best rate means nothing if your funds get frozen. Risk labels: AUTO → pure DEX execution → no intermediary → no one can freeze your swap Flexible → provider uses its own liquidity → freezes extremely unlikely Pre-Check → provider screens your address before the swap → if there's an issue, the swap is rejected → funds never leave your wallet Controlled → provider runs AML checks → operates with external liquidity → freezes or KYC may be possible Best rate. Best risk transparency. That’s what a real swap engine looks like.


Announcement: our TEE/ZK/MPC privacy email service is will be called Iron Mail. Our current estimate for a release date is start of Q3 2026 (roughly a 4 month development time). If you read the article below, and comment we'll award you with a perk (read on). A lot of people boldly claim "SMTP is old, therefore privacy is impossible". That's fair, if you say it with an open mind. What is also true is that multi-party computation and zero-knowledge proofs have come a long way, and so has TEEs. By utilizing a novel stack of these technologies (a stack we call IRON), we can ensure that even if served with a subpeona, we cannot capture data while at rest, while in transit (both inbound and outbound), this includes metadata. We will have free options that give you up to 1 GB of storage, as many folders as you need. Pinned mails, and so much more. While I can't go fully into detail on the exact mechanisms of how the IRON stack works yet to achieve in-platform privacy soundness, you'll be getting it near launch to verify for yourself exactly how we make sure that you can still receive, send and store emails with no option to for the service provider (us), to read your emails. Period. Iron Mail is developed for everyone to use. We'll be doing a public ceremony to get rid of so called "toxic waste" (generating a CRS which anyone who's verified can participate in) as the entire service relies on zero-knowledge proofs that every user can verify for their email dispatch that: 1) inbound is decrypted within a TEE edge server. 2) the plaintext was directly sent to an MPC council. 3) mail routing and attribution was done correctly. 4) SMTP-specific things such as DKIM verification. 5) outbound is jointly broadcast through MPC collaboration with the final email not being visible to the service provider. All zero-knowledge circuits will be released, after they've been audited by several parties, you can audit them yourself. This means, there is no uncertainty on whether we have hidden log infrastructure, since that would be either a) tampering with the process, which would invalidate the proof chain or b) be outright impossible once it's being processed by the MPC committee. Setting expectations 1. Referrals On referrals. We will have them. If we sponsor influencers, they will not be given a script, they can give their honest opinion. We will only be giving sponsorships to niche technical channels who actually knows what they're vouching for. Ironmail is mostly meant to be deployed for institutional and governmental security. Running a permanent free service for the public is purely in the interest of promoting good opsec and giving people access to a new innovation in a space where there hasn't been much for years now, despite annual earnings in excess of $100M+ (for Proton Privacy in 2024, per Zoominfo). We might also give referral code to tech enthusiasts who write blogs or has an audience, as these are the people who can accurately assess the veracity of the claims made. This has remained our biggest issue with companies like Proton: the marketing. We've seen them be subversive or sometimes, what can easily be suspected to be, intentionally misleading. 2. Defending users Based out of Delaware, US., jurisdictionally, we'll stand up for every subpoena, and we will always carry an up-to-date warrant canary in the footer of the website that we urge you to check (or setup an automated curl for), to ensure the company is still in our control. Signing up will be through 3 options: 1. A proof of work puzzle that takes between 5-10 minutes to solve on most processors. 2. An SMS message (after which that number is marked "used", but is not associated with your email). 3. By using @onflowxyz, zero-knowledge based proof of uniqueness using an ICAO 9303 document (i.e. a passport, or ID card, none of the info is transmitted to us, only a zero-knowledge proof, which is merely a mathematical proof of the validity of information, not any of the actual information). Any request for user info, be it IP address, email, contents of email, phone number, name or setting up future snooping is impossible within the IRON protocol. But again, we always urge you to check the warrant canary. Accessing the Site We will offer both a web UI and a fork of Thunderbird to access the Ironmail. We will also have endpoints setup for TOR and I2P (though experiences may be slightly degraded in terms of smoothness due to JS blocking) if you do not want your ISP to know you're using privacy-respecting services. Users can sign up on a VPN (we suggest Mullvad), on TOR or via I2P. You can pay via credit card where we give you the option to pay via credit/debit card (but, it is not recurring, and all payment data is deleted after 20 days), you can decide if you want to renew. You can also pay using cryptocurrency, including Monero and Zcash shielded transactions. We want to keep as little information about you as possible. We do not store which transaction hash was associated with your purchase after the sufficient number of verifications. Pricing The service, as mentioned, is meant for governmental and institutional usage in private deployments, however for our public-facing site, which can also be used by organizations of any size, the pricing will be similar to that of Proton, simply due to a much larger computational overhead than something like Proton (MPC and TEE isn't cheap in overhead, neither is ZK). The service is 100% free for everyone who doesn't wish to use an extended feature set, and comes with half a gigabyte of storage by for the free tier. Political affilations We are not aligned with any party or ideology as a company, and our team rarely if ever discusses politics, we discuss privacy. Launch Due to the complex nature of the engineering the protocol to be production confident, then the auditing process, as well as stress testing, fuzzing and vulnerability testing along the way, combined with a UX we hope can rival the best, launch is set to be in approximately 4-5 months. The Prize Thank you for reading this. I've garnered a ton of support personally from a privacy-conscious crowd for talking about privacy pretty much everyday, from interesting papers to Proton to zero-knowledge and whatever else is on my mind. Sam Bent makes amazing videos, and apparently also, amazing blog posts (and hopefully he'll also make a video on the blog post he made). If you share what you liked most about his article, and why privacy-preserving emails matter to you we will reserve a handle for you, plus give you 2 months of the Enthusiast tier for free (use your own domains, more storage, aliases and unlimited email addresses). There is no upfront cost, we will simply send a code for you to enter once you sign up, which will also verify that you're trying to register the handle you reserved (some handles go quickly like first names, short words, etc.). Thank you For continuing the fight for privacy. We hope you're excited about the innovation we're trying to bring to this sector that has been very good at twisting words, using unclear marketing, only speaking up when caught and generally has tarnished the word 'privacy' for the average person in what they should expect. The more services LARP as true privacy-oriented services, that then turn out to be something different in highly publicized events, hurts the reputation of everyone else trying to build for privacy. And finally, good article Sam. Keep writing these.