r0pchain retweetledi
r0pchain
1.1K posts


r0pchain
@r0pchain
Cloudforce One REACT. Nation-state cyber actors are interesting and ♥ novel malware. The Andrew Dice Clay of ofsec. Former USIC/TAO, views my own.
USA Katılım Ocak 2017
843 Takip Edilen258 Takipçiler
r0pchain retweetledi

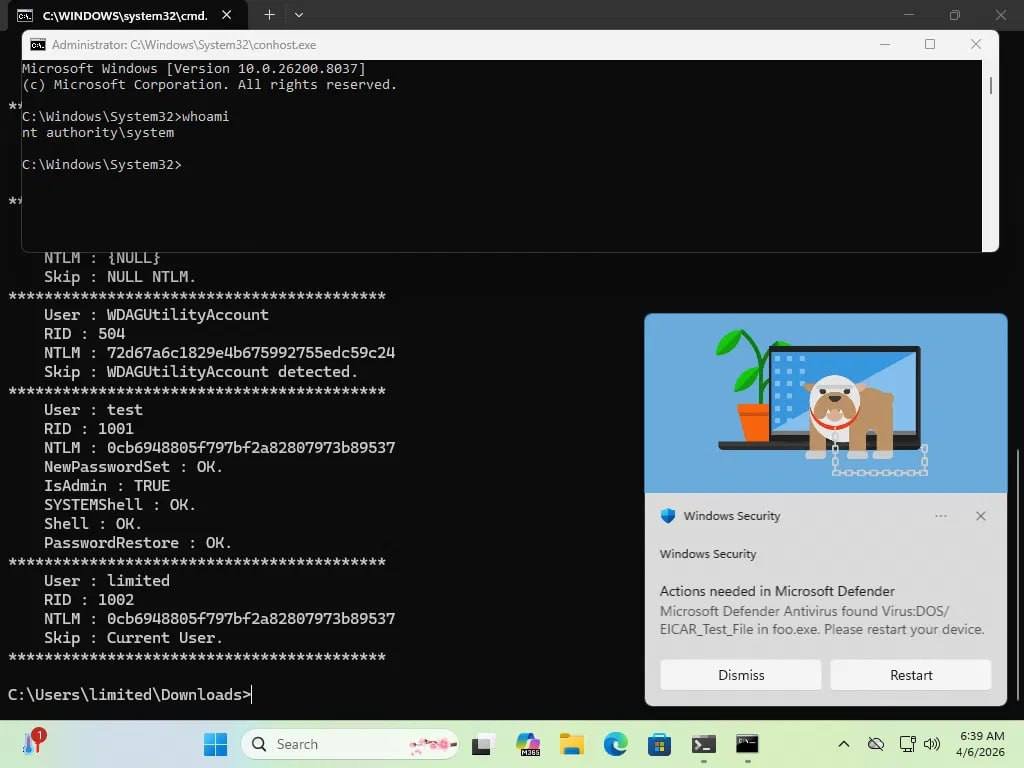
So here is new local privilege escalation zero-day I discovered, not patched yet too :).
In simple terms, if you have a service like RDP that exposes an RPC server, there many system services running as SYSTEM connect to it as RPC clients. If that service is turned off (RDP is off by default), it seems that any other process in Windows can expose the same RPC server using the same endpoint.
Now all the RPC calls from that SYSTEM processes will come to this fake server and If the process that deployed the server has SeImpersonatePrivilege, it can escalate to SYSTEM by impersonate the RPC client.
In the white paper below, I describe five exploit paths you can abuse.
However it's architecture problem and maybe there are more. It's Not A Potato
securelist.com/phantomrpc-rpc…
English
r0pchain retweetledi

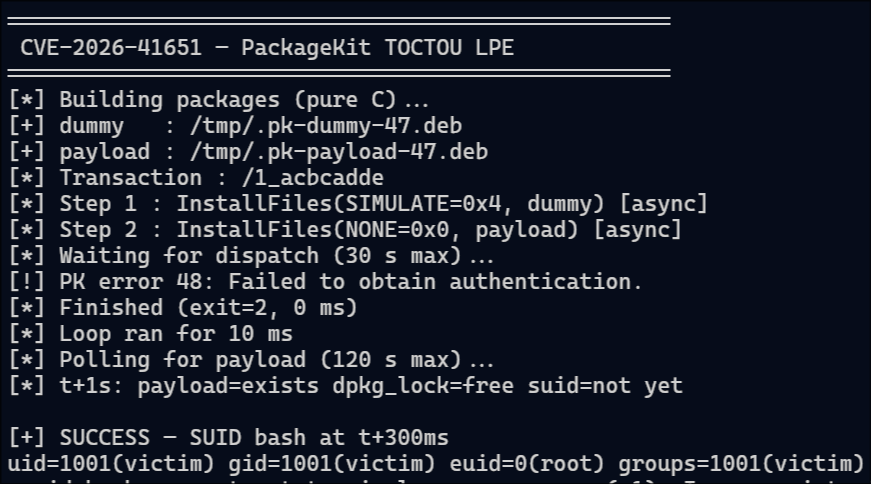
I just POC Pack2TheRoot (CVE-2026-41651) :
- github.com/Vozec/CVE-2026…
Local Privilege Escalation in PackageKit discovered by telekom.com affecting Ubuntu/Debian/RockyLinux/Fedora
English

This is bullshit and borderline CAN-SPAM violation. @Microsoft sending out marketing messages to 17 year old addresses; first message is Win7 beta group and second is BS "Microsoft Rewards" message to an alias created exclusively for that beta group.

English
r0pchain retweetledi
r0pchain retweetledi

🚨 Trojanized CPU-Z → STXRAT → PureLogs Stealer → PureHVNC → 54hrs of exfil through a hidden QEMU VM.
We caught everything after.
First documented full post-exploitation chain for this campaign. IOCs & hunting artifacts link in thread
#ThreatIntel #DFIR #Malware
English
r0pchain retweetledi

github.com/magicsword-io/…
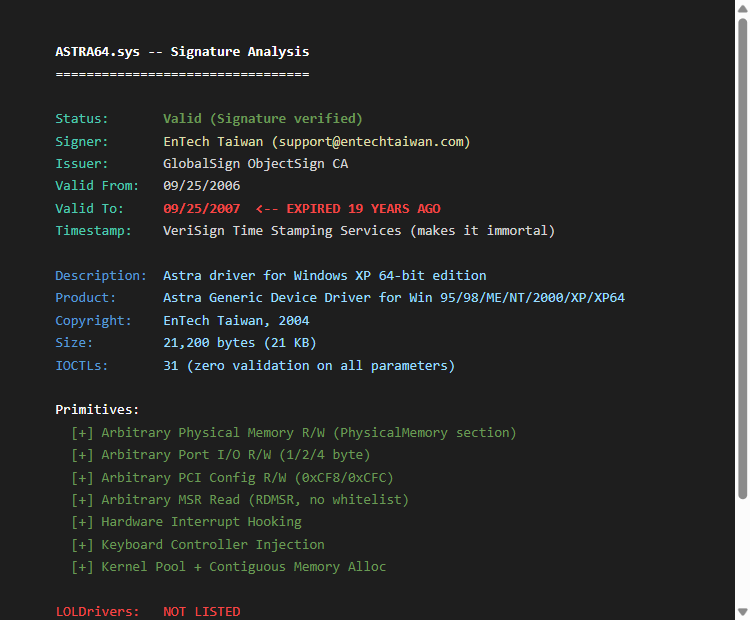
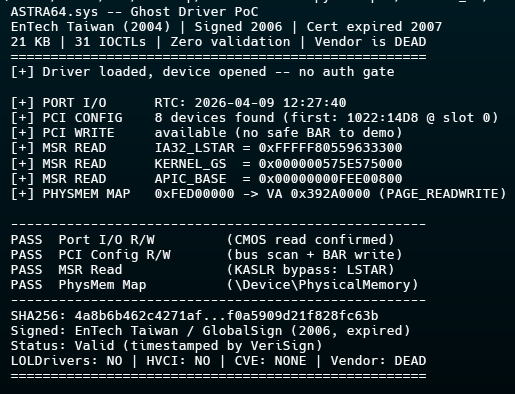
found a 21KB kernel driver from 2004 built for windows xp that still loads on windows 11 ASTRA64.sys by EnTech Taiwan. signed in 2006, cert expired in 2007, but its timestamped so windows still says "signature verified" 19 years later. the company doesnt exist anymore.
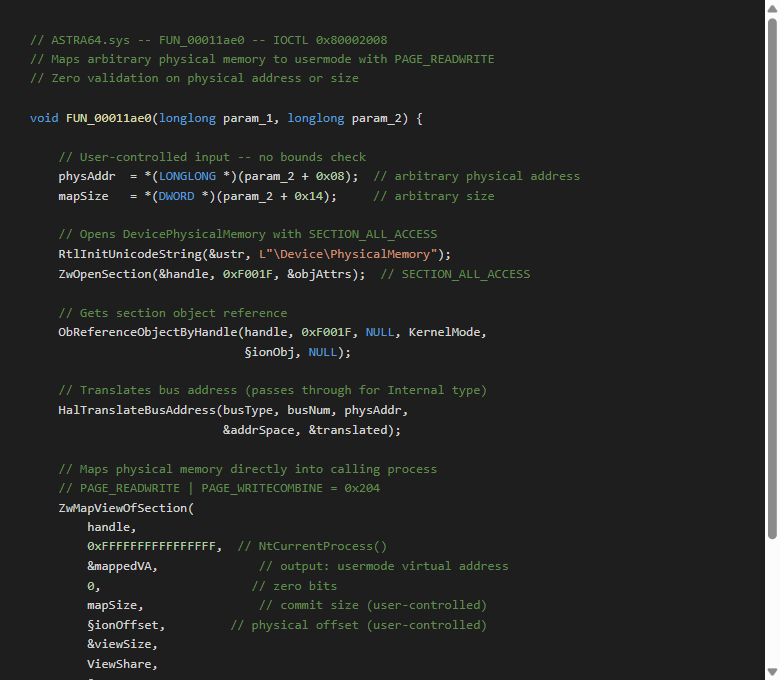
31 IOCTLs with zero validation on anything. arbitrary physmem R/W, port I/O, PCI config R/W, MSR read, interrupt hooking, keyboard injection. no auth gate, no hardware gate, loads on any system with sc.exe not on loldrivers. not on hvci blocklist. no CVE. vendor is dead so you cant even do responsible disclosure. theres nobody to email
filed an issue @M_haggis
English
r0pchain retweetledi

Bluehammer
Privilege escalation via Microsoft Defender. No patch yet
github.com/Nightmare-Ecli…
#0day #lpe
Deutsch
r0pchain retweetledi

I uploaded all the malware samples used in my book #EvasiveMalware to my Github:
github.com/d4rksystem/Eva…
I received some questions about the lab samples, so just posting it for everyone here 🤓
English
r0pchain retweetledi

@GamewithDave TIE Fighter.
It was truly revolutionary in terms of gameplay and environment.
Close second is Descent.
English
r0pchain retweetledi
My dear front-end developers (and anyone who’s interested in the future of interfaces):
I have crawled through depths of hell to bring you, for the foreseeable years, one of the more important foundational pieces of UI engineering (if not in implementation then certainly at least in concept):
Fast, accurate and comprehensive userland text measurement algorithm in pure TypeScript, usable for laying out entire web pages without CSS, bypassing DOM measurements and reflow
English
r0pchain retweetledi

Chinese 🇨🇳 APT group Red Menshen plants kernel-level BPFdoor backdoors in global telecom networks, creating "sleeper cells" for long-term espionage. New variants hide in HTTPS traffic and monitor 4G/5G signaling protocols.
Key findings:
• BPFdoor evolved from magic packet activation to Layer-7 HTTPS camouflage with RC4-MD5 encryption
• Implants target SCTP signaling protocols used in 4G/5G core networks for subscriber tracking
• Masquerades as legitimate services like HPE ProLiant hardware daemons and Docker containers
• ICMP tunneling enables covert C2 between compromised hosts using 0xFFFFFFFF terminal markers
• Affects telecom edge infrastructure: Ivanti VPNs, Cisco/Juniper routers, Fortinet firewalls
Attack chain leverages:
• Initial access via T1190 exploitation of public-facing telecom appliances
• CrossC2 beacons for Linux post-exploitation and lateral movement
• TinyShell passive backdoors on boundary devices for persistence
• Custom keyloggers with telecom-specific credential lists (usernames like "imsi")
DFIR artifacts include raw socket usage, anomalous BPF filters in kernel space, unexpected hardware service processes on non-HPE systems, and HTTPS traffic with fixed-offset padding schemes.
Hunt for unusual BPF syscalls, processes mimicking bare-metal hardware services on virtualized systems, and SCTP traffic inspection on non-telecom hosts.
#DFIR_Radar
English
r0pchain retweetledi

Why did the US ban this number in 2001? It sounds insane, but 25 years ago, the Motion Picture Association of America was genuinely trying to delete this number from the internet.
You see, back in 1999, a teenager in Norway named Jon Lech Johansen wrote a piece of code called DeCSS.
It cracked CSS, the encryption on DVDs. Suddenly, anyone could copy a movie with the click of a button. It was a nightmare for the movie studios.
They went nuclear. They sued the hacker magazine 2600: The Hacker Quarterly.
They threatened Slashdot, and their lawyers fired out cease-and-desist letters to anyone hosting the code. They called it a digital burglary tool.
But the internet found a loophole.
A computer scientist named Phil Carmody realized that computer code is just binary ones and zeros.
And you can treat that string of binary as a single number. That way, you get a really, really big integer—which is the illegal code.
But Carmody knew that just finding any number wasn’t going to be enough, because the government could still ban a random number.
So he needed a number that science would be forced to protect. He needed a prime number.
You see, the University of Tennessee maintains a prestigious academic database called the Prime Pages.
It records the 5,000 largest known prime numbers. Carmody realized that if he could turn the illegal code into a record-breaking prime number, the university would have to publish it.
His first attempt was 1,401 digits long. It was prime, but too small.
It didn’t crack the top 5,000 list. It wasn’t mathematically interesting enough to save.
So, he hacked the math.
Use this formula:
K × 256^N + B
Now, K is the illegal code part. 256^N is the mathematical equivalent of adding useless zeros at the end—like making a book longer by adding blank pages. It doesn’t change the actual content inside.
So, he kept adding “blank pages,” shifting the number, until he hit a mathematical jackpot—a 1,959-digit monster.
This wasn’t just illegal code anymore. It became the 10th largest ECP prime number ever discovered at the time.
It was checkmate.
The number was immediately added to the university database. For the MPAA to ban the code now, they would have to order a university to delete a scientific record.
You can’t censor mathematics.

English
r0pchain retweetledi

When normies ask me why I got out because clearly it was “the coolest job in the world”
America First Legal@America1stLegal
/1🚨EXPOSED — Biden CIA’s War on Motherhood: Newly released CIA documents reveal the Biden Administration identified “motherhood” and “homemaking” as indicators of “white racially and ethnically motivated violent extremism” (REMVE).
English
r0pchain retweetledi

In collaboration with Lookout and Google (thank you 🙏) we have been working on tearing down and building detections for DarkSword - iOS exploit chain for iOS 18.4 - 18.7. Super excited for this research 🎉. Please update your iPhones.
iverify.io/blog/darksword…
English
r0pchain retweetledi

If your company still forces password rotations, your security team is incompetent.
NIST, Microsoft, and the FTC all said to stop. Years ago.
georgeguimaraes.com/youre-dumb-sec…
English





