Sabitlenmiş Tweet
rayworks
1.5K posts


rayworks retweetledi
rayworks retweetledi

今天折腾 Google Play 有感而发。我觉得中国的开发者如果要开始做自己的付费产品,有一些必须要准备的事情,是完全可以提前开始做的:
1. 申请一个公司,最好是有限责任公司。如果没有条件的话,选择个体户其实也没有太大问题,可能有些地方会比较麻烦,但普通情况都能应对。
2. 准备一个国内备案的域名,有了域名之后,尤其是在国内生态下做事情会非常有用。因为基本上所有的网络服务,都需要先有一个备案域名以及一个企业组织身份,才能跨过准入门槛。比如一些第三方的 API、小程序,或者国内一些 SaaS 的 API 都是需要组织身份的,个人无法申请。
而且这些申请通常都需要半个月到一个月的时间,所以即使你现在还没用到,也应该提前准备好。
3. 如果是有做 App 的场景,最好提前准备好申请 D-U-N-S 码(邓白氏码)。
在 App Store 里面,邓白氏码的好处是可以让你显示的开发者名字不是真实姓名。如果你要上架 Google Play(这也是我今天遇到的事情),以个人方式注册 Google Play Developer 后,如果要上架一款应用,必须先拉上 12 个内测用户测试满 14 天才能正式上架,而组织身份则不需要。
这些都是可以提前做的事情,即使是你还没有用到。而且如果提前做了,当你遇到的时候,你会感谢你自己提前做好了。
(这条由语音转文字识别,并非 AI 生成)
中文
rayworks retweetledi

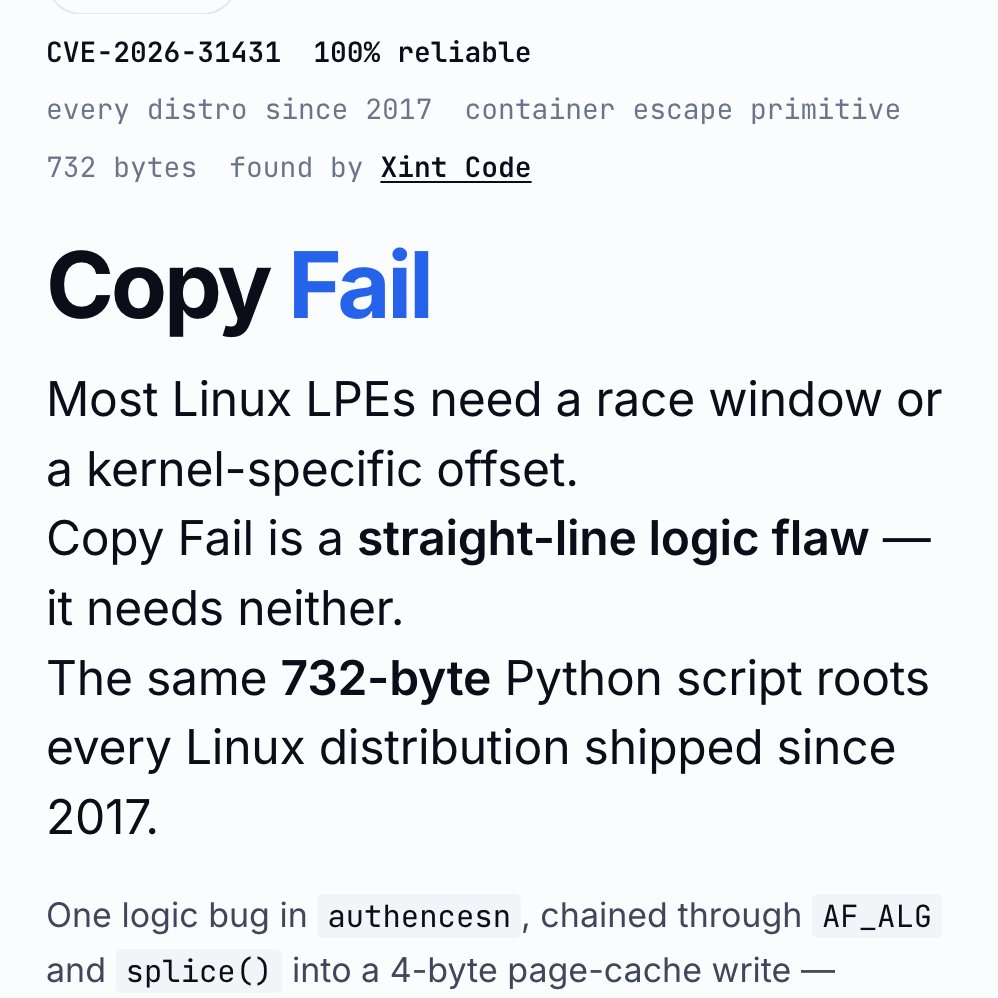
‼️🚨 BREAKING: An AI found a Linux kernel zero-day that roots every distribution since 2017. The exploit fits in 732 bytes of Python. Patch your kernel ASAP.
The vulnerability is CVE-2026-31431, nicknamed "Copy Fail," disclosed today by Theori. It has been sitting quietly in the Linux kernel for nine years.
Most Linux privilege-escalation bugs are picky. They need a precise timing window (a "race"), or specific kernel addresses leaked from somewhere, or careful tuning per distribution. Copy Fail needs none of that. It is a straight-line logic mistake that works on the first try, every time, on every mainstream Linux box.
The attacker just needs a normal user account on the machine. From there, the script asks the kernel to do some encryption work, abuses how that work is wired up, and ends up writing 4 bytes into a memory area called the "page cache" (Linux's high-speed copy of files in RAM). Those 4 bytes can be aimed at any program the system trusts, like /usr/bin/su, the shortcut to becoming root.
Result: the next time anyone runs that program, it lets the attacker in as root.
What should worry most: the corruption never touches the file on disk. It only exists in Linux's in-memory copy of that file. If you imaged the hard drive afterwards, the on-disk file would match the official package hash exactly. Reboot the machine, or just put it under memory pressure (any normal system load that needs the RAM), and the cached copy reloads fresh from disk.
Containers do not help either. The page cache is shared across the whole host, so a process inside a container can use this bug to compromise the underlying server and reach into other tenants.
The original sin was a 2017 "in-place optimization" in a kernel crypto module called algif_aead. It was meant to make encryption slightly faster. The change broke a critical safety assumption, and nobody noticed for nine years. That bug then rode every kernel update from 2017 to today.
This vulnerability affects the following:
🔴 Shared servers (dev boxes, jump hosts, build servers): any user becomes root
🔴 Kubernetes and container clusters: one compromised pod escapes to the host
🔴 CI runners (GitHub Actions, GitLab, Jenkins): a malicious pull request becomes root on the runner
🔴 Cloud platforms running user code (notebooks, agent sandboxes, serverless functions): a tenant becomes host root
Timeline:
🔴 March 23, 2026: reported to the Linux kernel security team
🔴 April 1: patch committed to mainline (commit a664bf3d603d)
🔴 April 22: CVE assigned
🔴 April 29: public disclosure
Mitigation: update your kernel to a build that includes mainline commit a664bf3d603d. If you cannot patch immediately, turn off the vulnerable module:
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || true
For environments that run untrusted code (containers, sandboxes, CI runners), block access to the kernel's AF_ALG crypto interface entirely, even after patching. Almost nothing legitimate needs it, and blocking it shuts the door on this whole class of bug...

English
rayworks retweetledi

💠 Haze 2.0-alpha01 is out!
This is a big release, splitting Haze up into layers, with the goal of enabling pluggable visual effects.
Let me know what you think!
🔗: chrisbanes.me/posts/haze-2.0/
English
rayworks retweetledi

《枪炮、病菌与钢铁》纪录片,3 集时长 2 小时 40 分钟,由原书作者贾雷德·戴蒙德亲自主持,PBS/NGC 联合制作。
相比书本来说更加生动,少了很多数据和文献信息,能快速看完。
链接:pan.quark.cn/s/39a89cd2d0b3
中文
rayworks retweetledi

This may be one of the most informative articles I've read in the past 5 years
proandroiddev.com/the-modern-gui…
English
rayworks retweetledi

Ghostty is leaving GitHub. I'm GitHub user 1299, joined Feb 2008. I've visited GitHub almost every single day for over 18 years. It's never been a question for me where I'd put my projects: always GitHub. I'm super sad to say this, but its time to go. mitchellh.com/writing/ghostt…
English
rayworks retweetledi

This is Lecture 5 of CS50 2D — recreate the classic Legend of Zelda game mechanics, dungeon generation, hitbox design, screen scrolling, and data-driven game development.
To take the course for a certificate, register at cs50.edx.org/2d.
youtu.be/iwjilbptPF

English
rayworks retweetledi

There are 2 career paths in AI right now:
The API Caller: Knows how to use an API. (Low leverage, first to be automated, $150k salary).
The Architect: Knows how to build the API. (High leverage, builds the tools, $500k+ salary).
Bootcamps train you to be an API Caller. This free 17-video Stanford course trains you to be an Architect.
It's CS336: Language Modeling from Scratch.
The syllabus is pure signal, no noise:
➡️ Data Collection & Curation (Lec 13-14)
➡️ Building Transformers & MoE (Lec 3-4)
➡️ Making it fast (Lec 5-8: GPUs, Kernels, Parallelism)
➡️ Making it work (Lec 10: Inference)
➡️ Making it smart (Lec 15-17: Alignment & RL)
Choose your path.
(I will put the playlist in the comments.)
♻️ Repost to save someone $$$ and a lot of confusion.
✔️ You can follow @techNmak, for more insights.

English
rayworks retweetledi
rayworks retweetledi

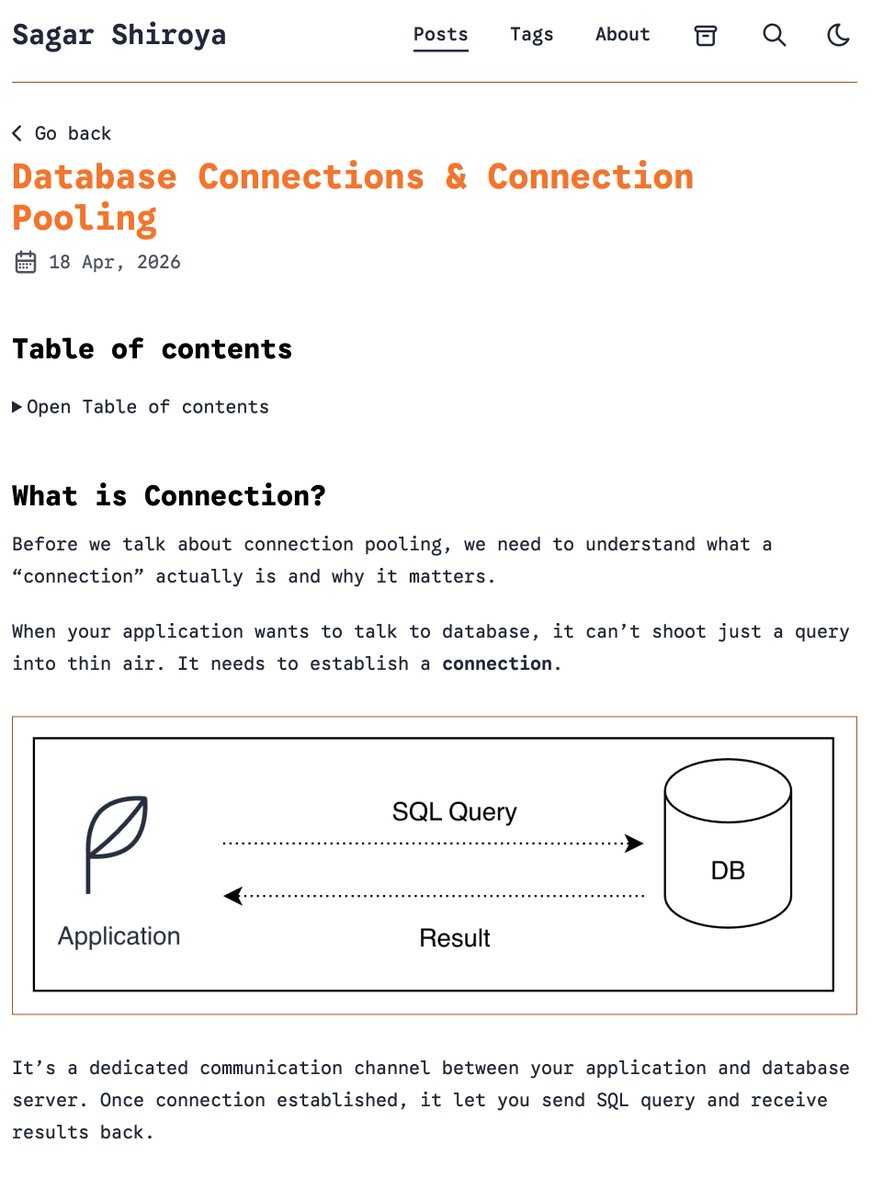
Database connections are expensive.
Opening and closing them on every request?
Even worse.
I wrote a simple breakdown on how connection pooling actually works and why it matters
Link: sagarshiroya.dev/posts/database…
#Database #SytemDesign
English
rayworks retweetledi

兄弟们,挖到个真正能落地的AI编程硬货课程!
Anthropic工程师Cal Rueb的25分钟Claude Code实操工作坊,含金量直接吊打你今年刷过的95%同类教程。
核心玩法就三招,全是Cal在内部天天用的实战逻辑,拿来就能直接套:
1. 先靠CLAUDE.md把项目规范、需求边界、细节要求一次性写死,从根上避免AI写跑偏、瞎发挥
2. 强制开规划模式,让它先把完整执行步骤想清楚、列明白,再动手写代码,彻底杜绝边写边改、逻辑混乱
3. 全程用测试驱动逻辑,让它写完代码自己写用例、自己验证结果,出了问题自己排查修正,不用你逐行抠bug
Cal这套东西的核心设计哲学,四个字就能说透:简单管用。
不搞花里胡哨的炫酷玩法,只追求代码稳定、不出错、能落地,这才是程序员真正需要的东西。
真心建议所有用Claude写代码的朋友,都去看看这个工作坊,看完直接收藏,下次写代码前翻一遍,效率直接拉满👇
看不懂的SOL@DtDt666
兄弟们,斯坦福这场两小时的讲座,把 ChatGPT、Claude这类大模型的真实构建逻辑拆解得一清二楚。 通透程度甚至超过了很多 AI 领域顶尖从业者日常能接触到的内容。 赶紧收藏好,今天少刷点抖音,匀出两个小时看一看, 它很可能会成为你这一整周最有价值的学习收获。
中文
rayworks retweetledi

Since we open-sourced pi-autoresearch, @Shopify teams have been running it on everything.
Results so far:
Unit tests: 300x faster
React component mounting: 20% faster
CI build time: 65% reduction
Made pnpm run faster
Autoresearch never stops trying things you'd never have time to try.
Repo: github.com/davebcn87/pi-a…
English
rayworks retweetledi
rayworks retweetledi

25 signs your team is not senior enough:
1. Jumping to code without understanding the problem.
2. No discussion of tradeoffs.
3. Over-engineering simple features.
4. Ignoring edge cases.
5. Weak code reviews.
6. No ownership mindset.
7. Avoiding difficult decisions.
8. No architectural thinking.
9. Debugging takes too long.
10. Blaming instead of fixing systems.
11. No documentation habits.
12. Repeating the same mistakes.
13. No performance awareness.
14. Ignoring security basics.
15. Tight coupling everywhere.
16. No testing discipline.
17. No long-term thinking.
18. Over-reliance on one engineer.
19. No clear coding standards.
20. Poor communication.
21. No estimation skills.
22. No monitoring awareness.
23. No rollback planning.
24. Panic during production issues.
25. No mentorship culture.
English
rayworks retweetledi