Sabitlenmiş Tweet

The $15,000 secret of viewing posts from private Instagram accounts.
003random.com/posts/meta-bou…
#bugbounty #bugbountytips #writeup
English
003random
825 posts


@rub003
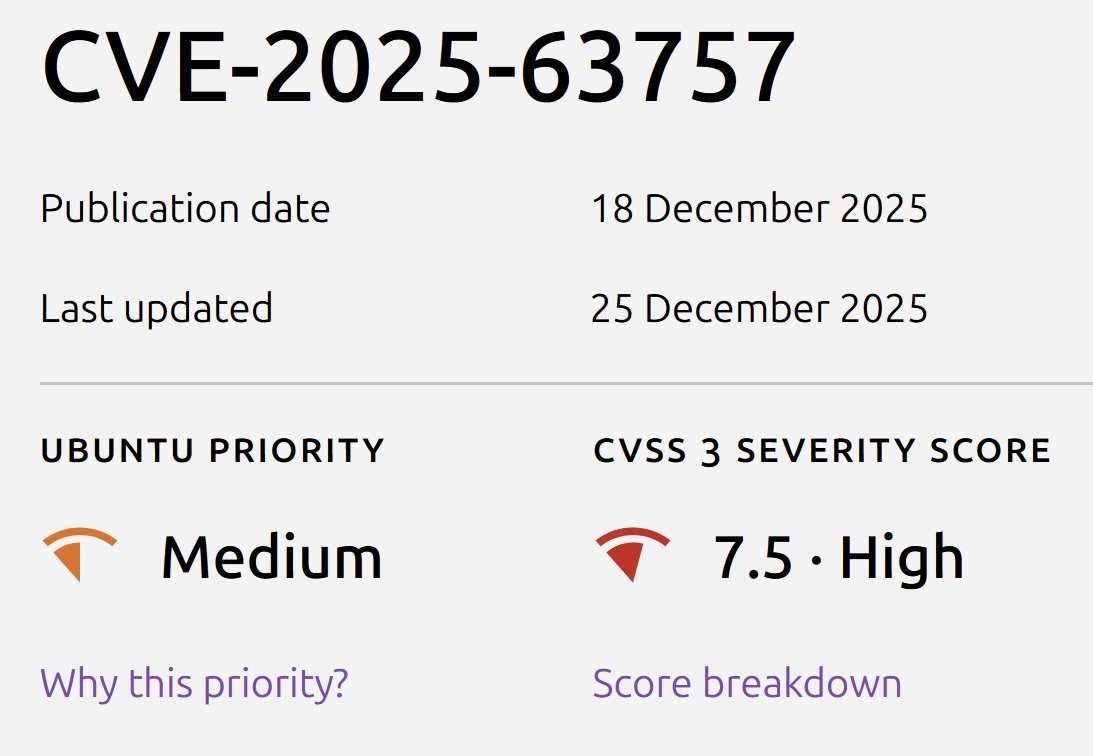
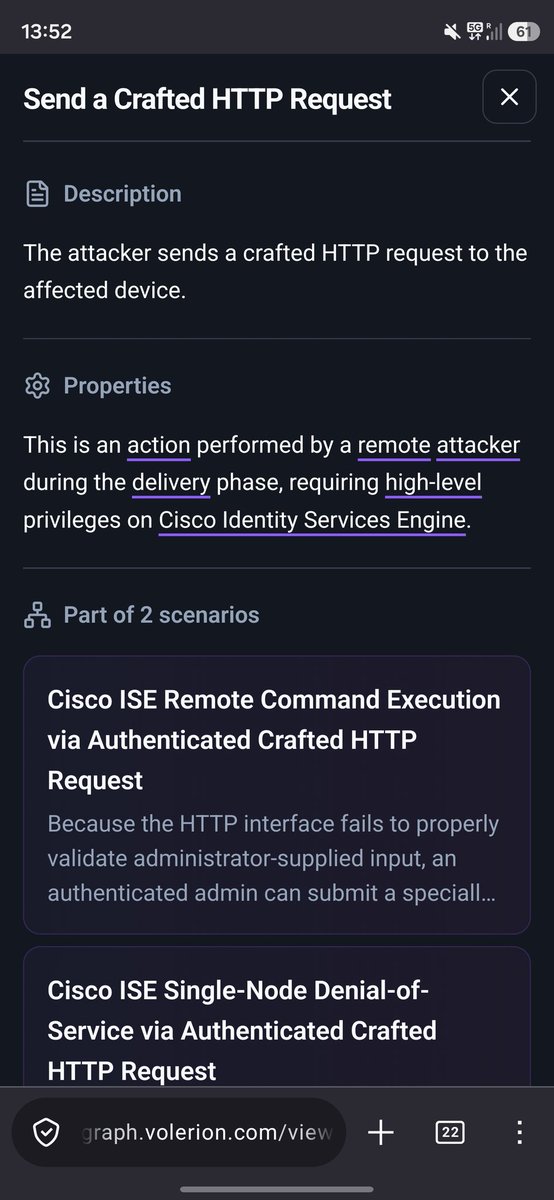
Working on fast, accurate and auditable CVE enrichment at Volerion.








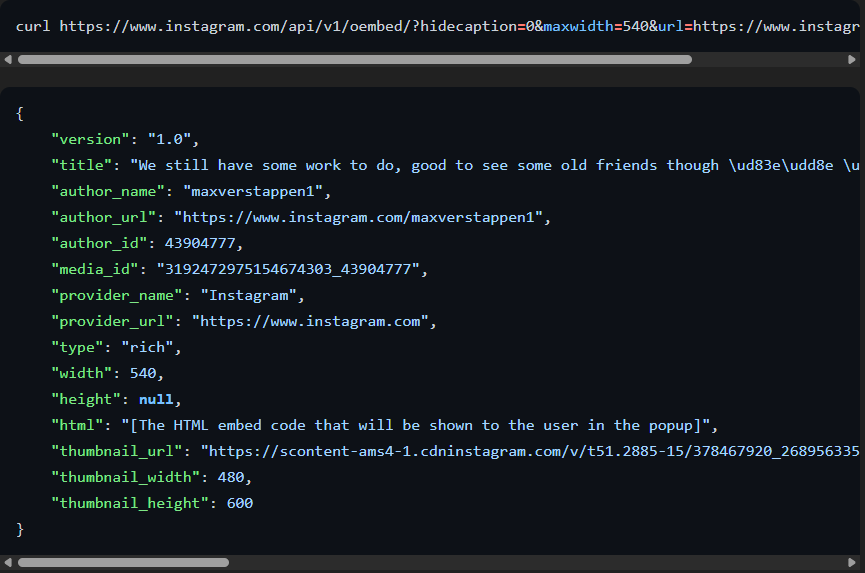



1️⃣ How I Exposed Instagram's Private Posts by Blocking Users @rub003 won 3rd place at BountyCon 2022 by chaining Instagram oEmbed endpoint quirks with mobile user agent detection to access private posts (earning him $14,500 in bounties). 003random.com/posts/meta-bou…