Sabitlenmiş Tweet

Hello community, I will be posting write ups on my new website sabotagesec.com . You can read all my old posts there.
Thank you for all the support and love!
#cybersecurity #malware #Windows #threatintell
GIF
English
sabotage
116 posts


@saab_sec
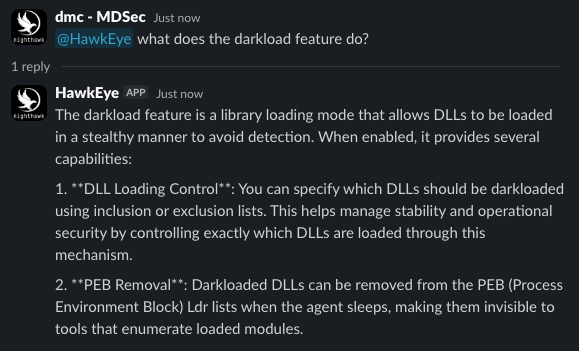
Nighthawk dev team @Mdseclabs



I guess we'll talk a bit about modern red teaming. The difficulty has increased severely. Lots of people be like just vibe code a stage0 with legit code for your pretext. How are you delivering it to bypass app control? Lots of words, no substance.