

Stefanos Chaliasos
216 posts


@schaliasosvons
security & research @zksecurityXYZ, Lecturer @ucl - Exploring ZKPs, PhD @imperialcollege




The first two known exploits against live ZK circuits just happened, and they weren't subtle underconstrained bugs. They were Groth16 verifiers deployed without completing the trusted setup ceremony. One was white-hat rescued for ~$1.5M, the other drained for 5 ETH. 🧵

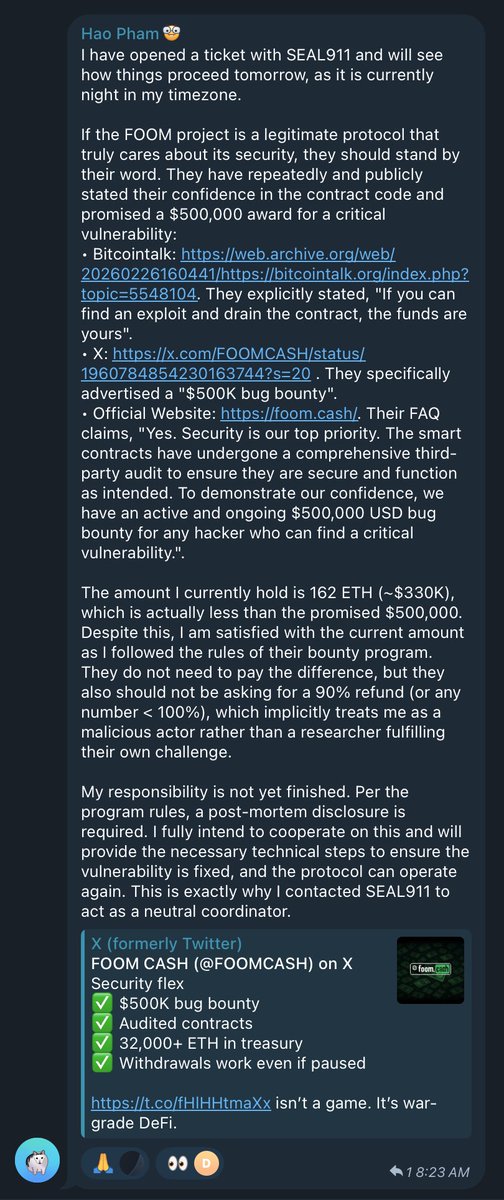


Here’s the core of Groth16 verification: e(A,B) = e(alpha,beta) + e(vk_x, gamma) + e(C, delta) Where: • (A, B, C) = the proof • vk_x = linear combo of public inputs • gamma & delta = fixed constants in the verifier With gamma == delta, the equation collapses to: vk_x + C = 0 → C = -vk_x Since vk_x comes only from public inputs, anyone can compute it, no secret needed.

🚨 Community Alert Blockaid's exploit detection system has detected a $1.1 m exploit on @foomclub_ protocol on Base and Ethereum. The root cause is a cryptographic issue in the ZK verifier. More details in 🧵

2 days ago, Veil Cash project was exploited on the Base blockchain. Their old pools were drained for 2.9 ETH. A small, but real hack. The misconfigured `Verifier` contract was out of scope for our audit engagement with Veil. Here is a nice root cause analysis from the community (Thanks to @beacon302). Veil's new pools are not vulnearble to this attack, we hope the project stays safe and secure🙏 github.com/DK27ss/VeilCas…


Introducing EVMbench—a new benchmark that measures how well AI agents can detect, exploit, and patch high-severity smart contract vulnerabilities. openai.com/index/introduc…


Introducing EVMbench—a new benchmark that measures how well AI agents can detect, exploit, and patch high-severity smart contract vulnerabilities. openai.com/index/introduc…



AI vulnerability research is non-deterministic. The same model looking at the same code won't take the same reasoning path every time. Some paths find nothing. Some paths find the bug. A single scan is a coin flip. But what if you keep flipping? Introducing zkao.




How do we minimize risk when integrating zkEVM proving into Ethereum L1? My latest blog post (link in thread) approaches this question by breaking down the risks into granular categories, making tradeoffs explicit. 1/7