ShadowArcanist
12 posts




It’s here! Our newest addition to our GPU line arrived with the NVIDIA RTX PRO 6000 Blackwell Max-Q graphics card and the Intel® Xeon® Gold 5412U 24-core CPU 🙌
Get now more VRAM to a lower price!
htznr.li/GEX131_tw

English

@duborges > (my project was running on "next": "15.5.4", behind cloudflare dns, but their recent fix didn't work apparently)
I think the WAF only kicks in if your domain is proxied (orange-cloud) through cloudflare
English

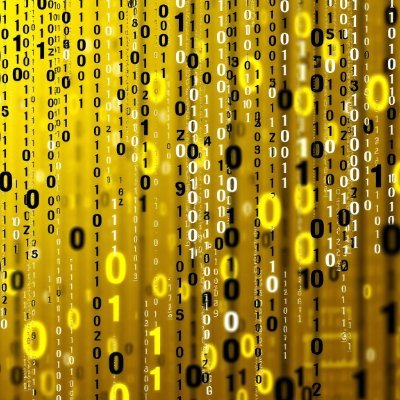
i've been hacked
and traced the malware's wallet to see how much money they actually made from this new exploit
(if you use Next.js/React, READ THIS!)
I woke up to a terrifying email from Hetzner: "Netscan Detected."
my server was blocked and a botnet was using my IP to attack others
i dug into the logs and what I found the anatomy of the attack:
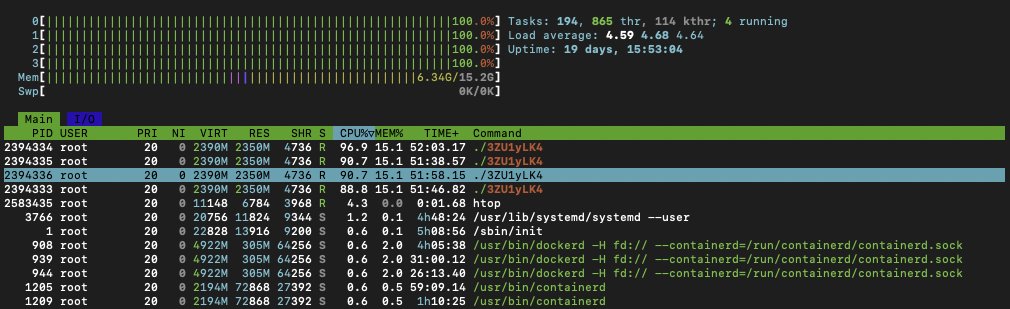
1) The Symptoms: I logged into htop and saw the mess:
- CPU usage: 361%
- A process named ./3ZU1yLK4 running wild
- Random connections to an IP in the Netherlands
my server wasn't serving my app anymore; it was mining crypto for someone else!
2) The Culprit: It wasn't a random SSH brute force. It was inside my Next.js container
the malware was sophisticated
it renamed itself nginxs and apaches to look like web servers
it even had a "killer" script that hunted down other hackers' miners to kill the competition
3) The "Root" Cause (literally): Probably the recent React/Next.js CVE-2025-66478 exploit was the entry point
(my project was running on "next": "15.5.4", behind cloudflare dns, but their recent fix didn't work apparently)
but the fatal error was mine: my Docker container was running as ROOT
Coolify deploys like this automatically when using Nixpacks, and I never changed it...
so because of USER root, the malware could install cron, systemd, and persistence scripts to survive reboots
meaning, it was able to infect my whole server, from a single Next.js docker!
4) The Forensics: I ran docker diff on the container - the hacker didn't just run a script, they installed a whole toolset..
- /tmp/apaches.sh (The installer)
- /var/spool/cron/root (The persistence)
- /c.json (The wallet config)
5) The Fix: I killed the container, scrubbed the host, and extracted the malware for analysis.
but the real fix is in the Dockerfile. if you are deploying Node/Next.js, DO NOT use the default (root), you must:
- RUN adduser --system nextjs
- USER nextjs
if you have Docker on ROOT and didn't update the exploited react version, you'll be hacked soon
check your containers NOW. Run: docker exec id
(or get the full list first: docker stats --no-stream)
If it says uid=0(root), you are one vulnerability away from being a crypto-miner host.
(it's easy to notice when hacked, it will be a command running on the top CPU%, using all your hardware resources)
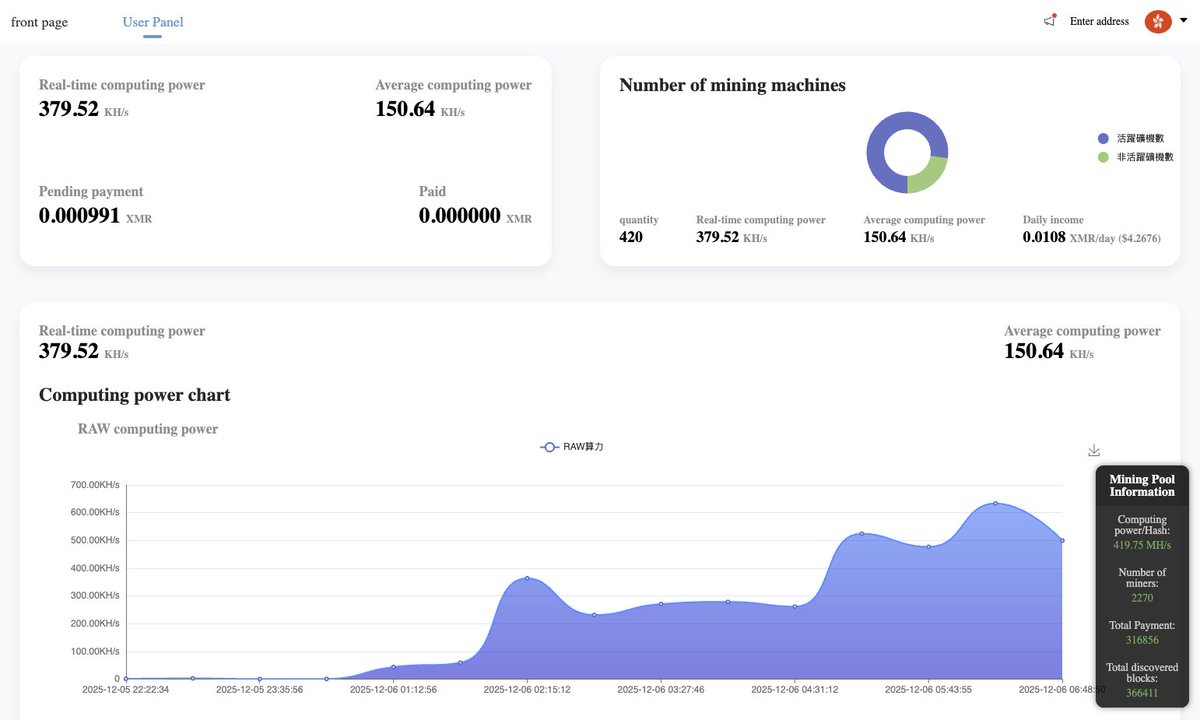
6) The Money: I dug deeper and recovered the config file (c.json)
- Wallet: A Monero (XMR) address: 831abXJn8dBdVe5nZ***
- Pool: auto.c3pool . org
and ofc i tracked the hacker’s wallet on the mining pool
7) The Scale: My server wasn't alone. It was just 1 of 415 active zombies in this botnet
they are burning the CPU of 400+ cloud servers... to earn...
guess how many millions?
$4.26/day
on the image attached you can see: "Total Paid: 0.00", meaning this campaign just started. I caught them on Day 1.
i also tracked back the server where they hosted the malware, and by inspecting the code, I found several comments in Chinese, so I guess that's their origin
im rebuilding from scratch on a fresh VPS. the lesson was expensive, but at least I caught it before the hosting nuked my account permanently...
PS: I have the IP for all the other machines mining with that malware, not sure how I can help them, but feel free to contact me if ur doing infosec
stay safe
English

@heyandras @Cloudflare Hopefully, you are not getting inspired by their recent downtime too
Anyways excited for your new release
English

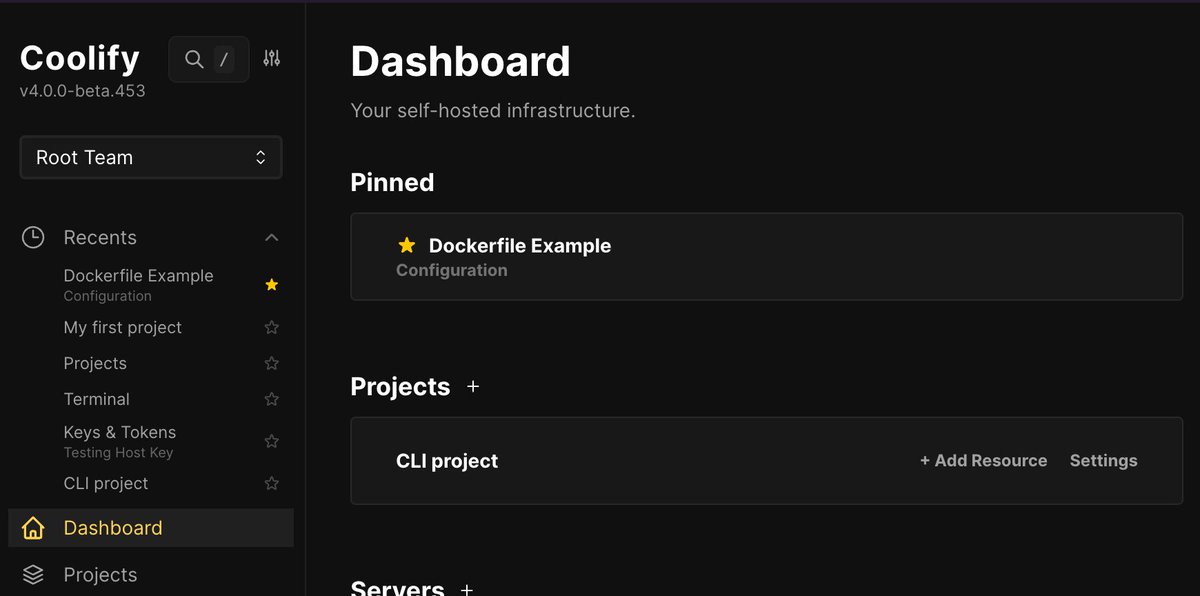
🛠️ A small surprise for the next version: recent and pinned items, inspired by @Cloudflare 's new sidebar.
English

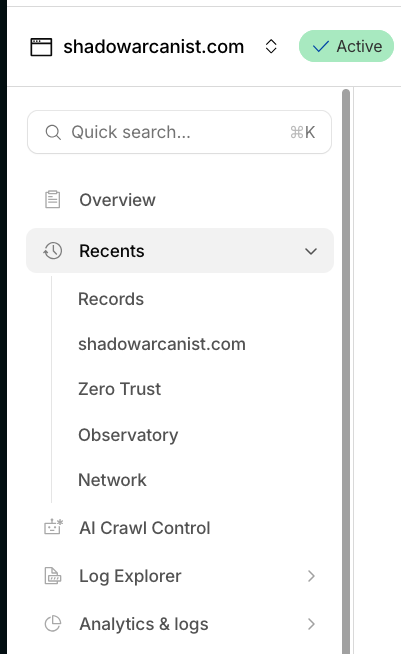
@heyandras @Cloudflare Andras the sub text under the recent items feels we are forcing text into a small area, which is one of the reason I hated Cloudflare's sidebar but very recently they removed it and improved the recent like this:
English

@xnova_pritam @heyandras @Cloudflare About 2 weeks ago I slightly improved the cards: github.com/coollabsio/coo…
Can you share some examples of the "bit modern" ?
English

@heyandras @Cloudflare hey, can you also update the project's🙃 cards ui a bit modern?
English

@heyandras I heard @coolifyio solves this, and the team behind Coolify is awesome, you should definitely give it a try!
English


@Hetzner_Online 's server backups feature is a life saver!
Yesterday on @coolifyio support we had a user who accidentally deleted Coolify database decryption key.
Restoring a Hetzner backup saved the day, and it only cost 20% of the server price. Totally worth it!

English

Should I check it with real use case?
Like developing Coolify?
These benchmarks are pure nothing if it cannot help you during development.
Elon Musk@elonmusk
Not bad. And Grok 4.20 will be much better.
English

@peaklabs_dev > Adjusted license inside composer.json to AGPLv3
What is this license for? is it for Coolify v5 or some other stuff we use on v5? (no idea what composer.json is for xD)
English
Development Log #173
👨🍳 Core Coolify Development
✅ Force pushed the v5.x branch with all updated commits
✅ Added a new security readme file to v5
✅ Improved overall repo structure and other overall things and squashed the commits into existing ones
✅ Squashed some more existing commits to clean up the Git history
✅ Removed some more v5 commits that are no longer needed
✅ Improved the .gitignore file
✅ Adjusted license inside composer.json to AGPLv3
🩹 Health
❌ Skipped my walk
English

@RochasRomain @ahlimanhuseynov @peaklabs_dev I checked the PR and it's out of my knowledge level of Coolify's codebase :/
So we have to wait for Peak or Andras to review PR like this one.
@heyandras just pinging you here incase you haven't seen that PR yet.
English